What Is a Memory Leak in Linux Servers and Why It Breaks Production Systems
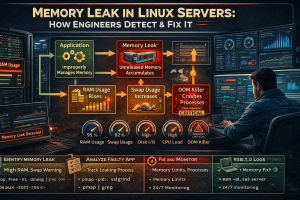
A memory leak in Linux servers occurs when an application continuously consumes RAM without releasing it back to the operating system. Over time, this leads to memory exhaustion, system slowdowns, and eventually a complete outage. Engineers detect memory leaks by analyzing process-level memory growth and fix them by optimizing application behavior, restarting affected services, and implementing proactive Linux server management services. If left unresolved, memory leaks silently degrade performance until the server becomes unresponsive.
Key Takeaways for Memory Leak Detection and Fixing
A memory leak is not a sudden failure. It is a gradual degradation of system performance caused by inefficient memory handling at the application level. Engineers identify memory leaks by tracking consistent RAM growth in processes and correlating it with system slowdowns.
- Memory leaks occur when applications fail to release allocated memory
- RAM usage increases steadily even under constant workload
- Swap usage increases when RAM becomes insufficient
- System performance degrades before complete failure
- OOM killer terminates processes under extreme conditions
- Continuous monitoring prevents long-term outages
Organizations that deploy Linux server management services and 24/7 technical support identify and resolve leaks before they impact uptime.
Problem Diagnosis: Identifying Memory Leak Symptoms at Network Level
When a server suffers from a memory leak, the first visible symptom appears as delayed or failed network responses. SSH sessions become slow, web applications take longer to respond, and FTP connections may fail intermittently.
At the kernel level, memory exhaustion prevents the system from allocating buffers required for network operations. This leads to connection timeouts and dropped packets. Engineers often misinterpret this as a network issue, but the root cause lies in memory starvation.
Root Cause Analysis: How Memory Leaks Occur at Application Level
Memory leaks originate within application code. Programs allocate memory dynamically but fail to release it after usage. This results in continuous memory consumption even when workload remains constant.
Languages like C and C++ require manual memory management, making them more prone to leaks. However, leaks also occur in managed environments like Java and Python due to improper object handling or garbage collection issues.
At the system level, the kernel continues to allocate memory until it reaches the limit, after which system stability degrades.
Root Cause Analysis: Heap Memory Growth and Resource Exhaustion
Applications store dynamic data in heap memory. When objects remain referenced unintentionally, the garbage collector cannot reclaim memory.
This leads to gradual heap expansion. Over time, the process consumes a significant portion of available RAM. The system eventually reaches a point where it cannot allocate memory for new processes, causing system instability.
Root Cause Analysis: Swap Usage and Performance Degradation
When physical memory is exhausted, the Linux kernel uses swap space as a fallback. Swap resides on disk, making it significantly slower than RAM.
As swap usage increases, system performance drops drastically. Disk I/O increases, leading to higher latency for all operations. This creates a cascading effect where applications slow down and eventually stop responding.
Root Cause Analysis: OOM Killer and Forced Process Termination
The Out-Of-Memory (OOM) killer is a kernel mechanism that protects the system from complete failure. When memory usage reaches critical levels, the kernel terminates processes to free memory.
However, the OOM killer does not always select the correct process. It may terminate essential services such as databases or web servers, leading to immediate service disruption.
Root Cause Analysis: File Descriptor and Resource Leakage
Memory leaks often correlate with resource leaks such as file descriptors or sockets. Applications that fail to close files or network connections consume system resources continuously.
Over time, this leads to resource exhaustion, preventing new connections from being established. This results in errors similar to connection failures, even though the root cause lies in resource mismanagement.
Root Cause Analysis: Long-Running Processes and Application Behavior
Long-running processes are more prone to memory leaks. Applications such as web servers, database engines, and background workers continuously handle requests.
If these processes contain inefficient memory handling, leaks accumulate over time. Restarting the service temporarily resolves the issue, but the problem reappears if the root cause remains unaddressed.
Step-by-Step Resolution: Stabilizing a Server with Memory Leak
Engineers first stabilize the system by reducing memory pressure. They identify processes consuming excessive memory and restart or isolate them.
This immediate action restores system responsiveness and prevents complete failure. However, it serves only as a temporary solution until the underlying issue is fixed.
Step-by-Step Resolution: Identifying the Faulty Application
Engineers analyze process behavior to identify abnormal memory growth. They monitor memory usage patterns over time and isolate processes that exhibit continuous growth.
This approach helps pinpoint the exact application responsible for the leak, enabling targeted troubleshooting.
Step-by-Step Resolution: Fixing Application-Level Memory Leaks
Engineers resolve memory leaks by optimizing application code and improving memory management. They ensure that objects are released properly and unnecessary references are removed.
In managed environments, they tune garbage collection settings to improve memory reclamation. These changes prevent continuous memory growth and stabilize the system.
Step-by-Step Resolution: Implementing Memory Limits and Controls
Engineers enforce memory limits at the application and system level. This prevents individual processes from consuming excessive resources.
They configure resource limits to ensure fair allocation and prevent system-wide impact from a single faulty application.
Step-by-Step Resolution: Monitoring and Preventing Future Leaks
Engineers implement monitoring tools to track memory usage continuously. Alerts trigger when memory consumption exceeds predefined thresholds.
This proactive approach ensures early detection and prevents recurrence of memory leaks.
Architecture Insight: How Memory Leak Leads to Full System Failure
Memory leaks do not cause immediate failure. They create gradual degradation. As memory usage increases, the system starts using swap, which slows down performance.
Eventually, the kernel cannot allocate memory for critical operations. This leads to process failures, service disruptions, and complete system unresponsiveness.
Architecture Insight: Relationship Between Memory, CPU, and Disk I/O
Memory leaks impact multiple subsystems. Increased swap usage leads to higher disk I/O, which increases latency.
As processes wait for memory and disk operations, CPU scheduling becomes inefficient. This interconnected failure leads to system-wide performance degradation.
Real-World Use Case: Memory Leak in cPanel Server Environment
A production server under cPanel server management experienced gradual performance degradation. Users reported slow response times, followed by intermittent outages.
Engineers identified a PHP-based application consuming increasing memory over time. The application failed to release memory after processing requests.
Root Cause in Real Case: Application-Level Memory Leak
The application maintained persistent object references, preventing memory cleanup. Over time, RAM usage increased continuously, leading to swap usage and system slowdown.
This resulted in delayed responses and eventual service unavailability.
Resolution in Real Case: Optimization and Monitoring Implementation
Engineers optimized the application code and implemented memory monitoring. They also configured periodic service restarts to mitigate temporary issues.
These changes stabilized the system and prevented recurrence of memory-related failures.
Hardening Strategy: Implementing Server Hardening for Memory Stability
Server hardening involves optimizing system configuration to prevent resource misuse. Engineers disable unnecessary services and enforce strict resource limits.
This ensures that critical applications receive sufficient resources while preventing misuse by non-essential processes.
Hardening Strategy: Adopting 24/7 Monitoring for Early Detection
24/7 technical support teams continuously monitor system performance. They detect abnormal memory usage patterns and respond immediately.
This proactive approach prevents minor issues from escalating into major outages.
Hardening Strategy: Leveraging Linux Server Management Services
Professional Linux server management services ensure continuous optimization and monitoring of server infrastructure. Engineers analyze system performance, detect anomalies, and implement corrective actions.
This ensures long-term stability and performance consistency.
Struggling with Traffic Spikes and Downtime?
Partner with our experts for reliable cloud auto-scaling, proactive monitoring, and high-availability infrastructure solutions.
Authoritative Conclusion: Building Memory-Stable Linux Infrastructure
A memory leak in Linux servers is not a random failure. It is a predictable outcome of inefficient resource management at the application level. Engineers who understand memory behavior can detect leaks early and prevent system outages.
Organizations that invest in Linux server management services, implement server hardening, and rely on 24/7 technical support maintain stable and high-performing infrastructure.





