How Do Virtual Data Center Support Services Ensure Enterprise Infrastructure Excellence and Reliability?
Server Management,Server Management Services,Summary: Virtual Data Center Support Services for Modern Enterprises Virtual Data Center Support plays a crucial role in modern IT infrastructure management by ensuring that virtualized environments remain stable, secure, and highly efficient. As organizations increasingly adopt virtualization technologies and hybrid cloud models, the complexity of managing compute, storage, and network resources has significantly increased.…
Read moreDual-Core vs Quad-Core vs Hexa-Core vs Octa-Core: Which Processor is Best for Gaming in 2026?
Server Hardening,Server Management,Server Management Services,Understanding Modern Processor Technology in 2026 The processor market has changed dramatically over the last few years. Earlier, users only compared dual-core vs quad-core processors, but modern computing now includes hexa-core, octa-core, and even AI-powered processors built specifically for gaming, streaming, content creation, virtualization, and multitasking. In 2026, modern CPUs from Intel Core Ultra, AMD…
Read moreHow ActSupport Delivers 24×7 Server Management, Monitoring, and DevOps Support for High-Availability Infrastructure
Server Hardening,Server Management,Server Management Services,Introduction: Why High Availability Fails in Real Infrastructure Modern infrastructure does not fail suddenly. It degrades silently long before users notice downtime. CPU spikes remain unnoticed until applications freeze. Disk usage grows gradually until writes fail. Database connections saturate until login systems collapse. Network latency increases until APIs start timing out. High availability fails when…
Read moreHow to Choose and Configure a Dedicated Server? Complete Hardware, Security & Setup Guide
Server Hardening,Server Management,Quick Summary: The Dedicated Server Deployment Checklist Selecting and configuring a Dedicated Server in 2026 requires a balance between high-performance hardware and a “Zero-Trust” security architecture. To ensure production uptime and scalability for AI or SaaS workloads, follow these high-level technical requirements: Hardware Selection: Prioritize AMD EPYC or Intel Xeon processors with ECC Memory and…
Read moreWhat CTOs Look for Before Hiring a Managed Infrastructure Support Company
Server Management,Server Management Services,Managed server support services require a high degree of technical competence and cultural alignment to successfully bridge the gap between internal development cycles and external infrastructure stability. When a CTO evaluates a potential partner, they do not simply look for a list of supported technologies; they look for operational maturity, proactive risk mitigation, and a…
Read moreWhy Your Linux Server Is a Target for Bots? How to Block the Bots
Linux General,Server Management,Summary: Protecting Linux Servers from Bots & Brute Force Attacks Automated bots constantly scan the internet to exploit vulnerable Linux servers through brute force attacks and credential stuffing. To stop these threats, engineers must implement multi-layered security strategies including SSH hardening, Fail2Ban configurations, and advanced firewall management. These proactive measures significantly reduce server load and…
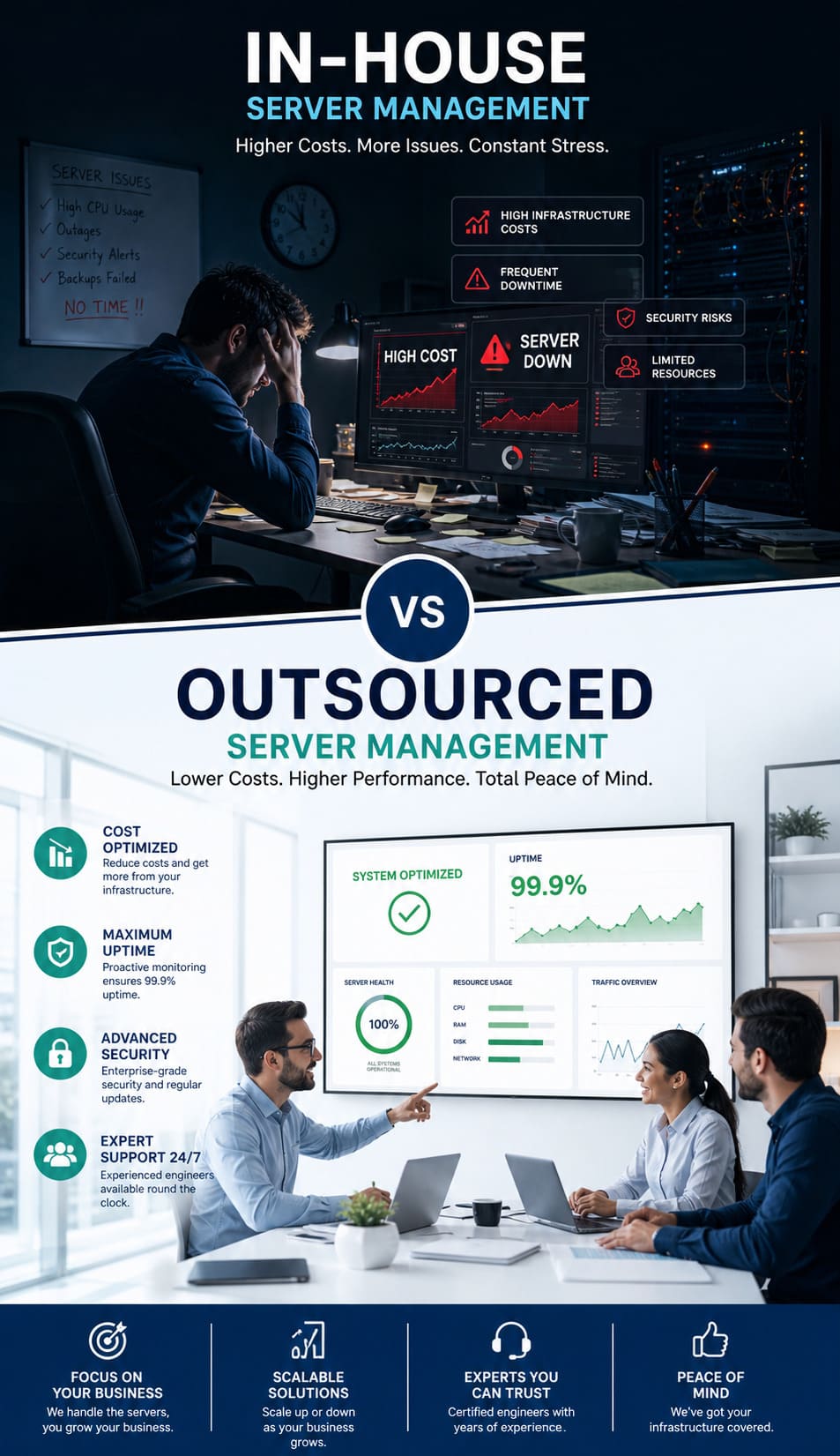
Read moreIn-House vs Outsourced Server Management: Fixing High Server Costs & Downtime
Server Management,Server Management Services,Summary Managing infrastructure in-house often leads to rising server costs and unexpected downtime. This happens due to the high cost of specialized talent and the need for 24/7 monitoring. Outsourced server management offers a scalable and cost-effective solution. It gives you access to senior-level engineers and proactive maintenance. All this comes at a fraction of…
Read moreWhat Are the First Steps When a Website Goes Down?
Cpanel,cPanel & WHM,Server Management,Overview: How to Quickly Diagnose and Fix a Website Downtime Issue A website goes down when failures occur across the DNS layer, server infrastructure, or application stack. The fastest way to recover is to first confirm whether the outage is global or limited to your network using external monitoring tools. Once confirmed, check DNS resolution…
Read moreSolving High Churn: How 24/7 Outsourced Hosting Support Stops Client Attrition
Cpanel,cPanel & WHM,Server Management,Overview: How 24/7 Outsourced Hosting Support Stops Client Attrition Outsourced hosting support is a direct strategy to stop client churn by ensuring 24/7 technical expertise is available to fix server issues the moment they arise. When hosting providers struggle with slow response times or technical bottlenecks, client trust breaks down and attrition follows. By integrating…
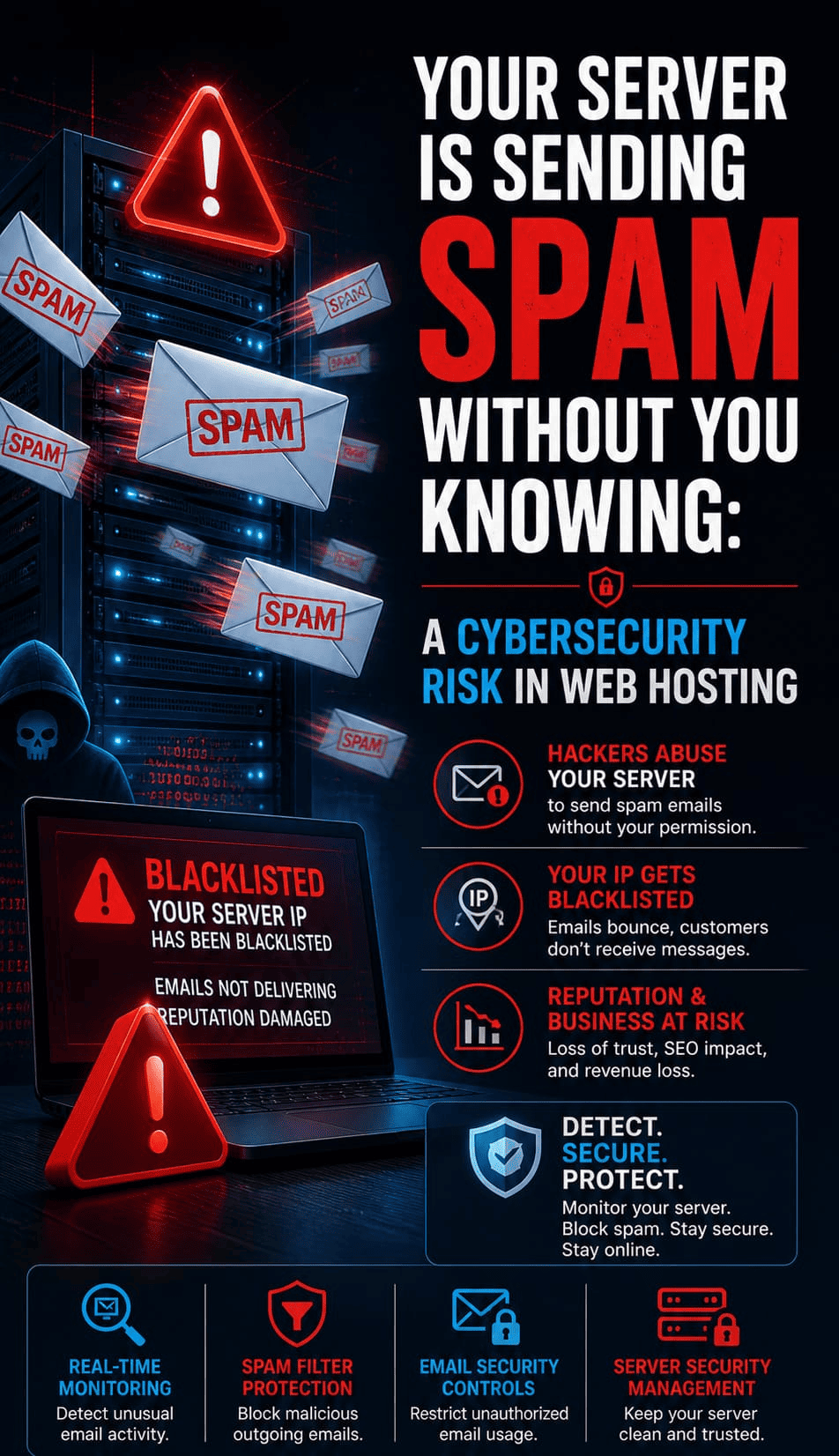
Read moreYour Server Is Sending Spam Without You Knowing: A Cybersecurity Risk in Web Hosting
Linux General,Linux/Windows Support,Server Management,Crunch Points: How to Stop Unauthorized Server Spam To stop unauthorized server spam, you must identify compromised PHP scripts, secure your Mail Transfer Agent (MTA), and prevent session hijacking. Unauthorized spam typically originates from obfuscated scripts hidden in directories like /wp-content/uploads/ or through stolen session tokens that bypass traditional MFA. We found that the most…
Read more