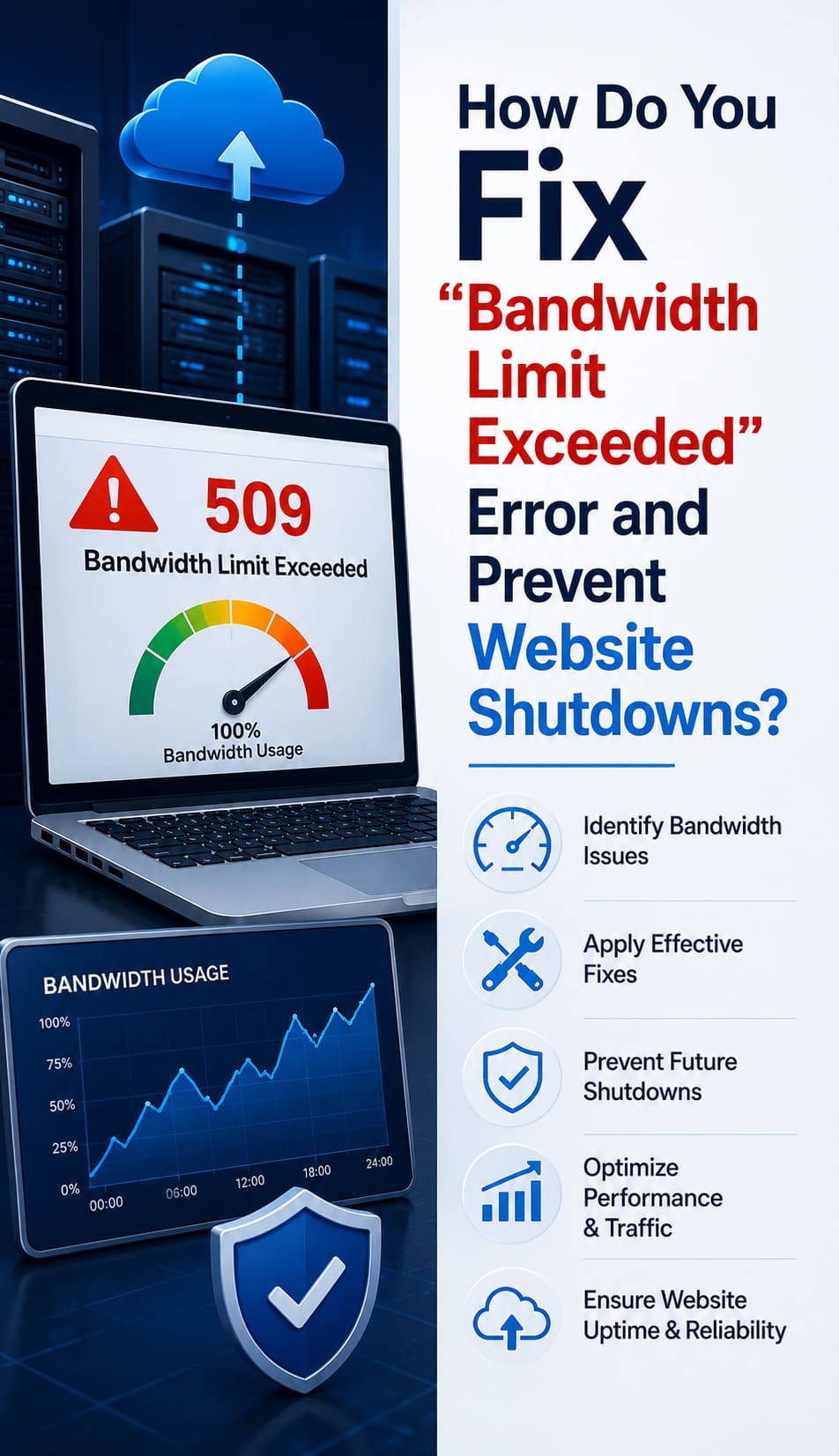
How Do You Fix the “Bandwidth Limit Exceeded” Error and Prevent Website Shutdowns?
cPanel & WHM,Linux General,You fix the “509 Bandwidth Limit Exceeded” error by increasing the monthly data quota in your hosting control panel, optimizing heavy media assets, or implementing a Content Delivery Network (CDN) to offload traffic. This error occurs when a website consumes its allocated data transfer limit, leading to an immediate suspension of web services and a…
Read moreWhy Your Linux Server Is a Target for Bots? How to Block the Bots
Linux General,Server Management,Summary: Protecting Linux Servers from Bots & Brute Force Attacks Automated bots constantly scan the internet to exploit vulnerable Linux servers through brute force attacks and credential stuffing. To stop these threats, engineers must implement multi-layered security strategies including SSH hardening, Fail2Ban configurations, and advanced firewall management. These proactive measures significantly reduce server load and…
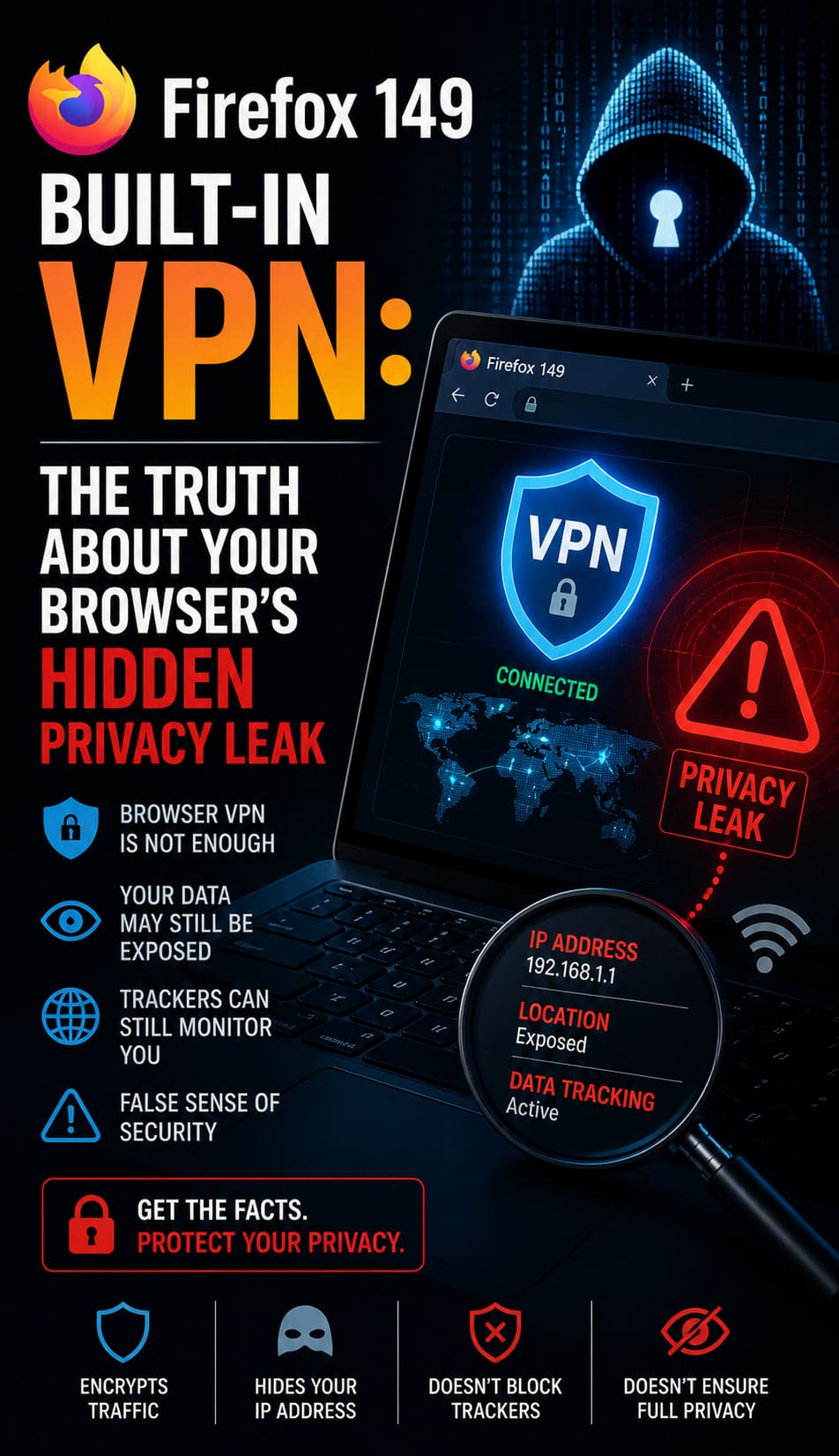
Read moreFirefox 149 Built-In VPN: The Truth About Your Browser’s Hidden Privacy Leak
Firewall/Iptables/Security,IT Infrastructure,Linux General,What You Need to Know: Firefox 149 Built-In VPN Direct Impact Analysis Firefox 149 features a native, built-in browser VPN designed to stop the “Hidden Privacy Leak” where websites and ISPs harvest your real IP address. Unlike standard private browsing modes that only clear local history, this integrated proxy creates a secure, zero-log tunnel for…
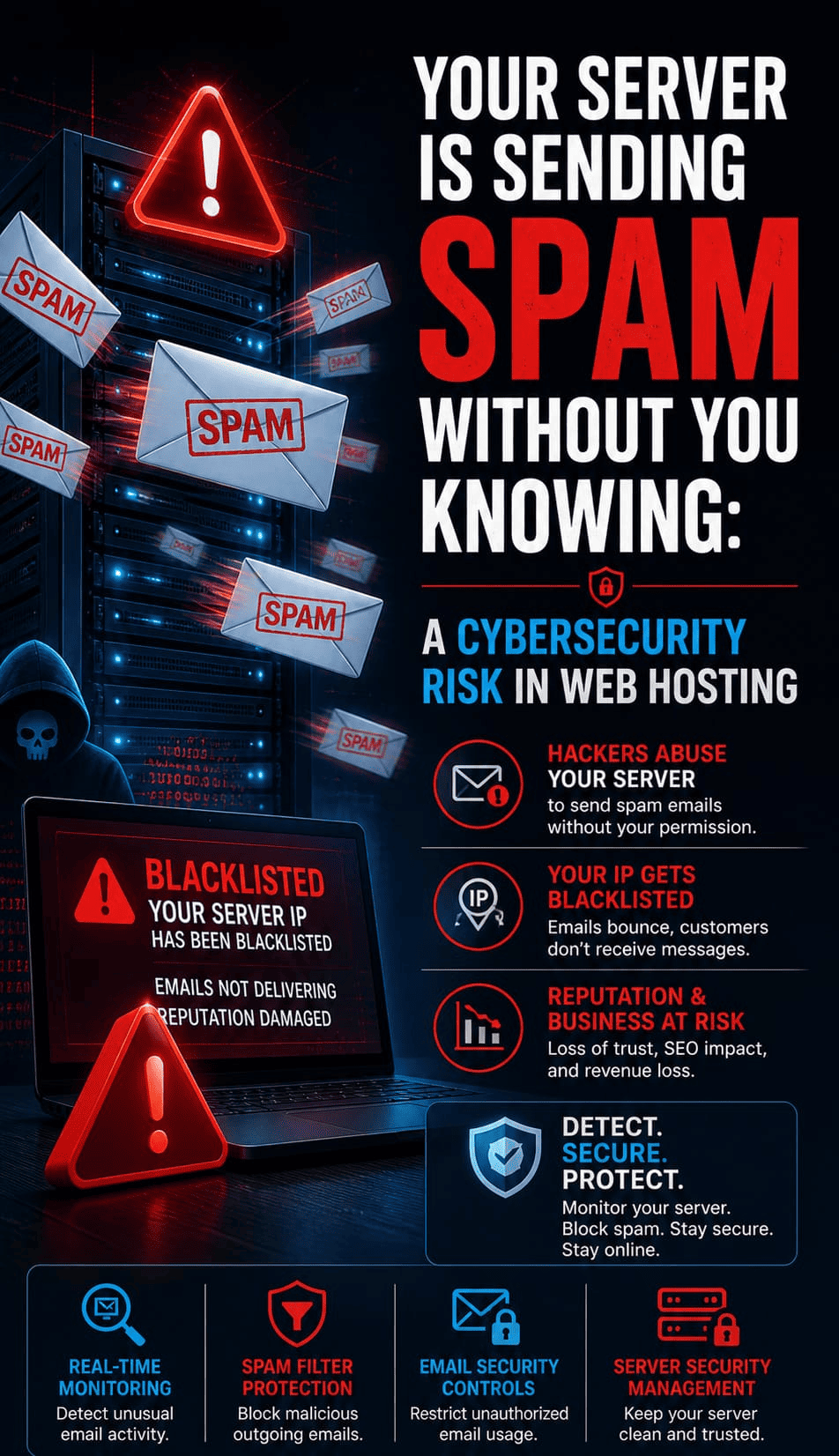
Read moreYour Server Is Sending Spam Without You Knowing: A Cybersecurity Risk in Web Hosting
Linux General,Linux/Windows Support,Server Management,Crunch Points: How to Stop Unauthorized Server Spam To stop unauthorized server spam, you must identify compromised PHP scripts, secure your Mail Transfer Agent (MTA), and prevent session hijacking. Unauthorized spam typically originates from obfuscated scripts hidden in directories like /wp-content/uploads/ or through stolen session tokens that bypass traditional MFA. We found that the most…
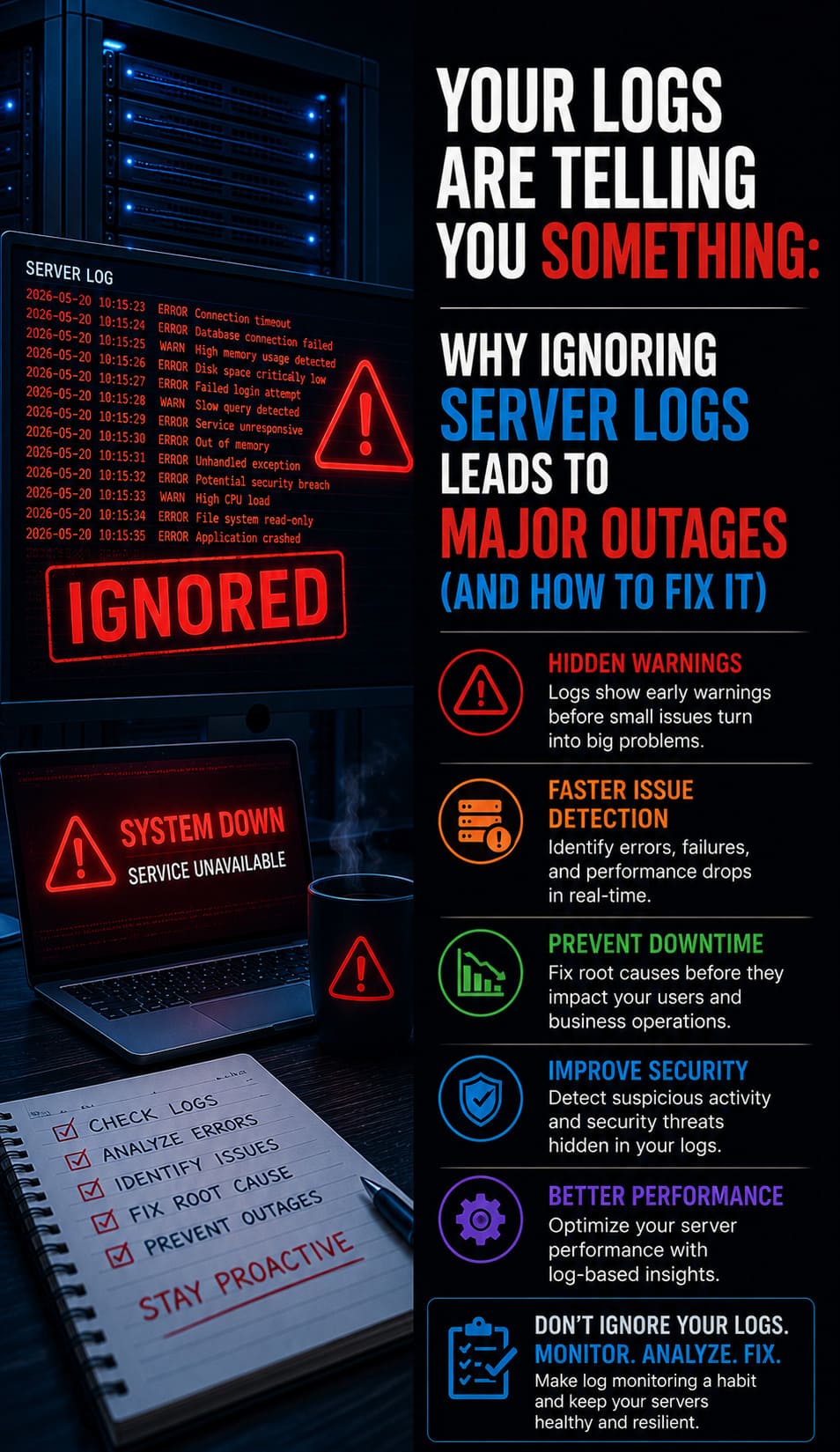
Read moreYour Logs Are Telling You Something: Why Ignoring Server Logs Leads to Major Outages (And How to Fix It)
Linux General,Server Management,What You Need to Know: How to Prevent Infrastructure Outages with Server Log Analysis Server log analysis prevents infrastructure collapse by identifying early warning signs of hardware failure, resource exhaustion, and security breaches before they scale into production outages. We found that over 70% of avoidable downtime occurs because administrators ignore “pre-fault” indicators in telemetry,…
Read moreToo Many Users Have Access to Your Server: Why Poor IAM Leads to Data Breaches
Linux General,Server Hardening,Server Management,Key Takeaways: The Critical Link Between IAM and Data Breaches Poor Identity and Access Management (IAM) causes over 80% of data breaches by allowing attackers to exploit excessive permissions and hijacked session tokens. Organizations often fail when they grant permanent access instead of practicing the Principle of Least Privilege, which limits every user to the…
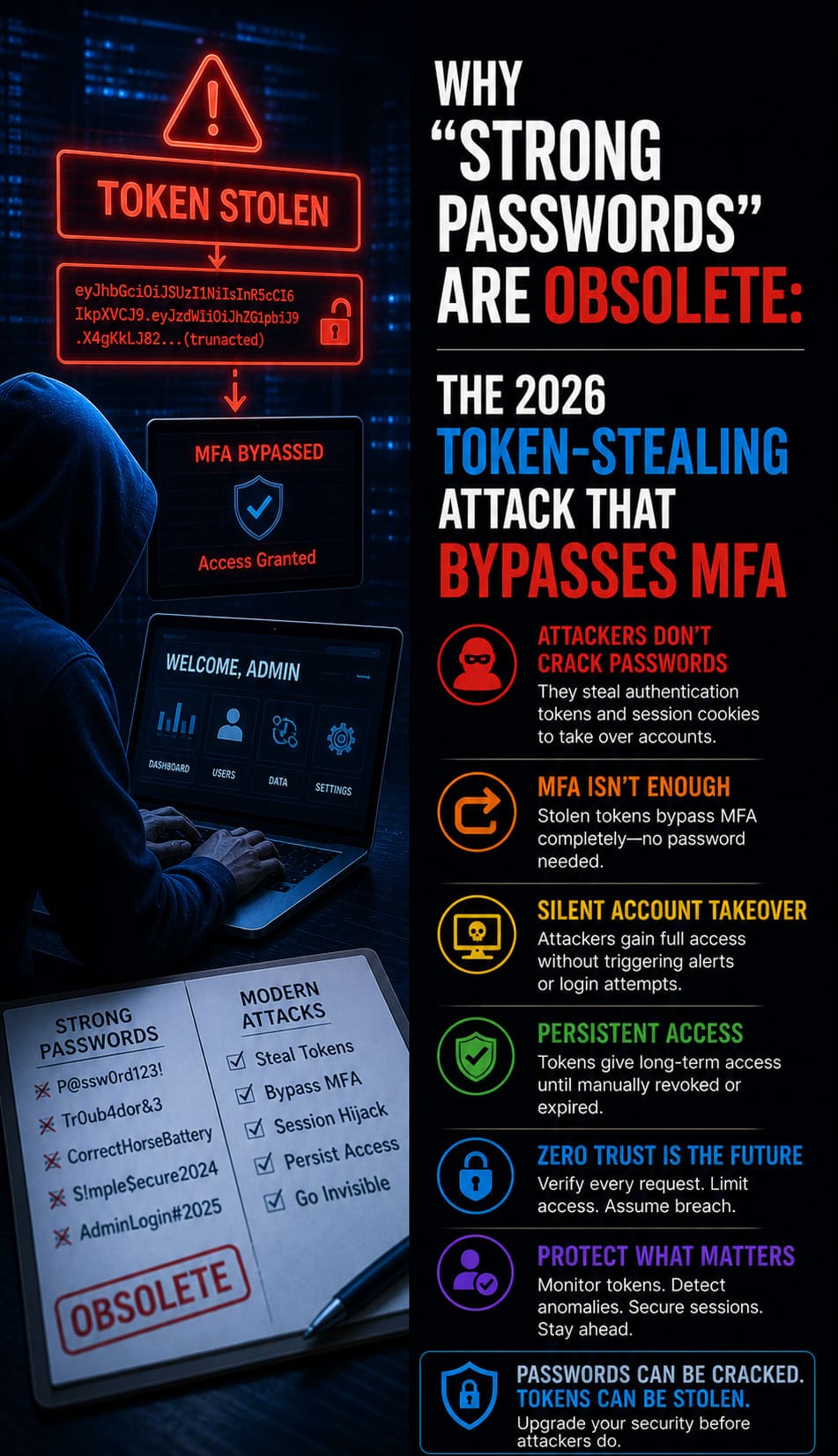
Read moreWhy “Strong Passwords” Are Obsolete: The 2026 Token-Stealing Attack That Bypasses MFA
Linux General,Machine Learning,Quick Breakdown: Your Browser Is the New Security Hole Strong passwords and traditional MFA have collapsed because modern Adversary-in-the-Middle (AiTM) and Browser-in-the-Browser (BitB) attacks steal authenticated session tokens directly from browser memory. We found that phishing kits like EvilProxy now bypass 6-digit SMS codes by acting as a live proxy to capture session cookies in…
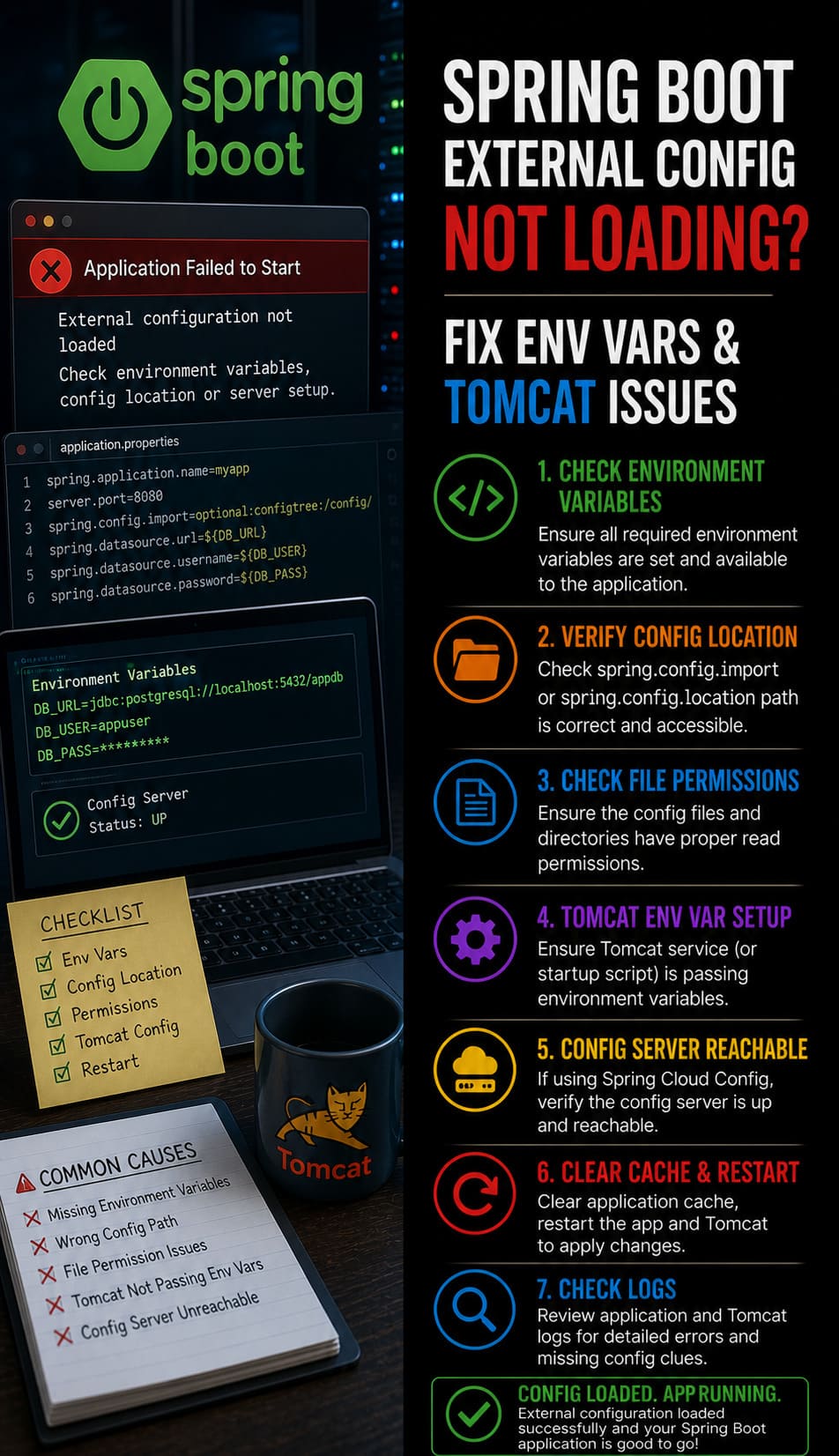
Read moreSpring Boot External Config Not Loading? Fix Env Vars & Tomcat Issues
All,cPanel & WHM,Linux General,Server Management,Summary: Spring Boot external configurations fail to load when the application defaults to internal classpath resources due to incorrect property precedence or environment variable invisibility. We found that most production issues occur because the Tomcat service user cannot access variables defined in a developer’s personal profile. To fix this, you should explicitly define JVM arguments…
Read moreServer Monitoring Issues: Definition, Tools, and Expert Failure Resolution
cPanel & WHM,IT Infrastructure,Linux General,Linux/Windows Support,Overviews and Technical Extraction Server monitoring issues occur when tracking agents fail, telemetry data gaps arise, or alert fatigue masks critical infrastructure bottlenecks. To fix these failures, engineers must validate agent connectivity, optimize probe intervals, and synchronize firewall rules with monitoring ports. Implementing real time server monitoring tools 2026 ensures continuous visibility into CPU states,…
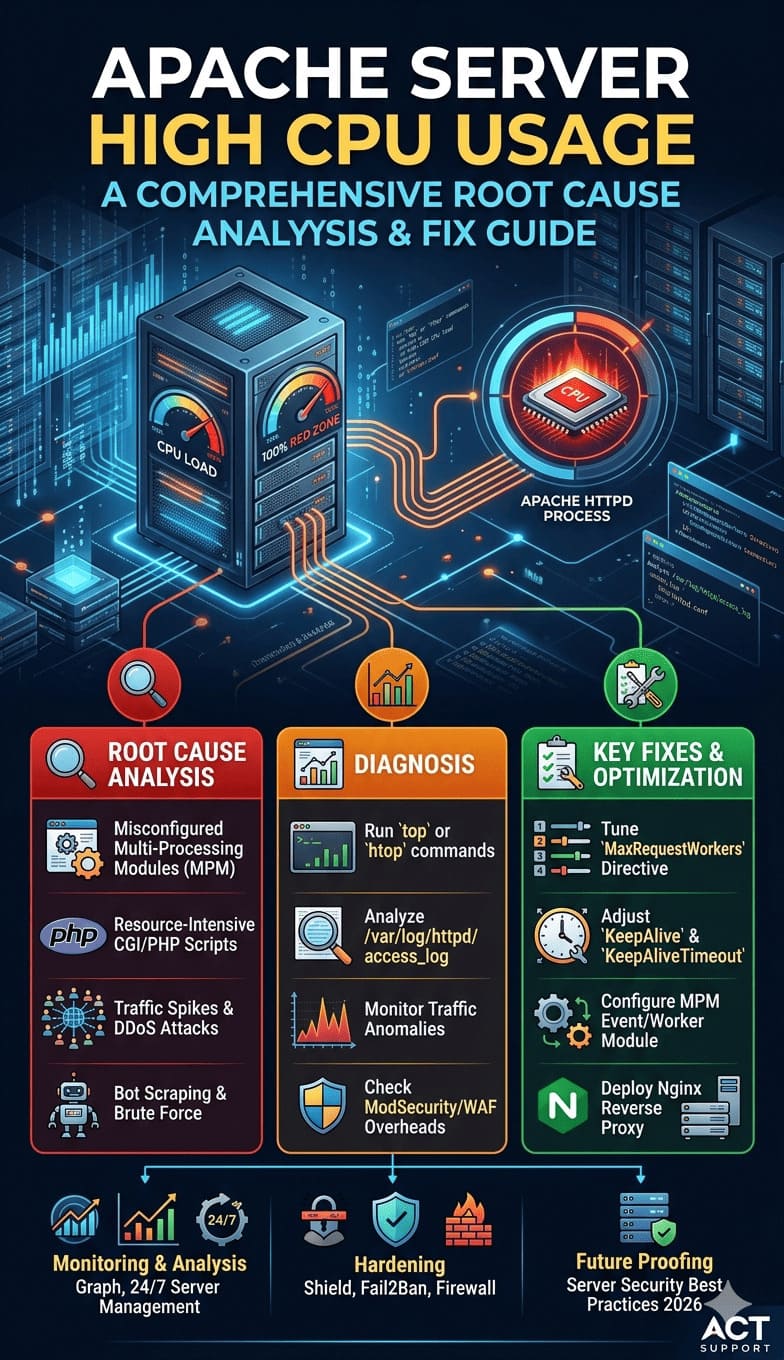
Read moreApache Server High CPU Usage: A Comprehensive Root Cause Analysis and Fix Guide
cPanel & WHM,IT Management,Linux General,Server Management,Server Management Services,What you need to Know: To fix Apache server high CPU usage, you must tune the MPM modules, reduce KeepAliveTimeout to 3 seconds, and optimize MaxRequestWorkers to prevent process loops. To resolve this, engineers must tune the MaxRequestWorkers directive, optimize KeepAlive settings, and identify bottlenecked PHP-FPM processes or database queries. Implementing proactive Linux server management…
Read more