AI Finds 271 Hidden Flaws in Your Browser
cyber security,IT Management,Overview For years, browsers have been treated as a safe and neutral layer between users and the internet. However, that assumption no longer holds true in today’s complex digital environment. Modern browsers are deeply integrated with business systems, cloud platforms, and sensitive data workflows. Recent AI-driven discoveries have revealed that many vulnerabilities were always present…
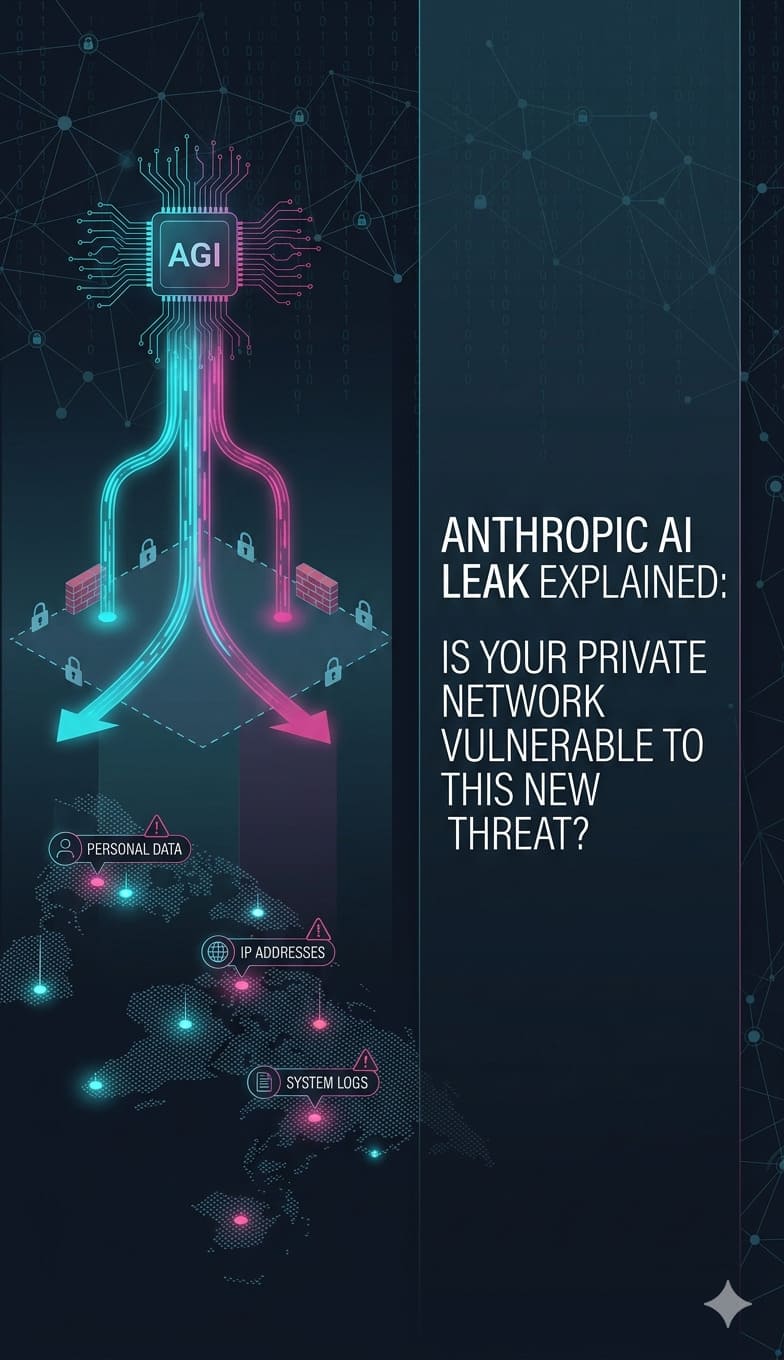
Read moreAnthropic AI Leak Explained: Is Your Private Network Vulnerable to This New Threat?
AI in IT Support & Infrastructure,IT Infrastructure,IT Management,Summary: The accidental exposure of Anthropic’s Claude Code source code in April 2026 has introduced severe risks, including CVE-2026-35022, which allows remote code execution via shell metacharacter injection. This leak gives hackers a roadmap to bypass security filters and hijack agentic AI systems to exfiltrate API keys, SSH credentials, and environment variables. To fix these…
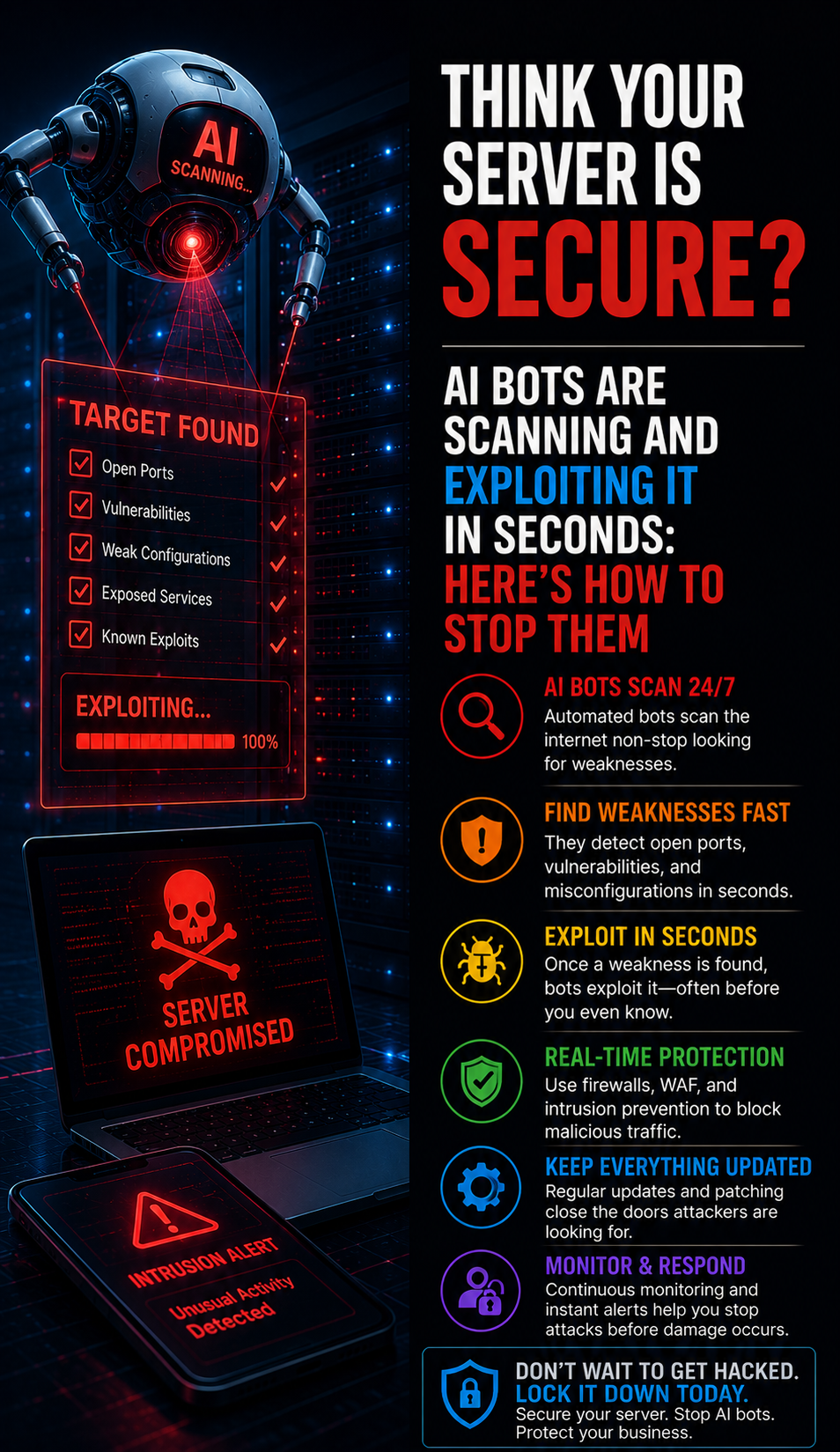
Read moreThink Your Server Is Secure? AI Bots Are Scanning and Exploiting It in Seconds: Here’s How to Stop Them
IT Infrastructure,IT Management,Modern server security has entered a volatile era where AI bots execute automated exploits in milliseconds, rendering traditional defenses like strong passwords and legacy MFA obsolete. Attackers now deploy Adversary-in-the-Middle (AiTM) kits and Browser-in-the-Browser (BitB) attacks to hijack active session tokens directly from your memory. To prevent total infrastructure takeover, organizations must transition to phishing-resistant…
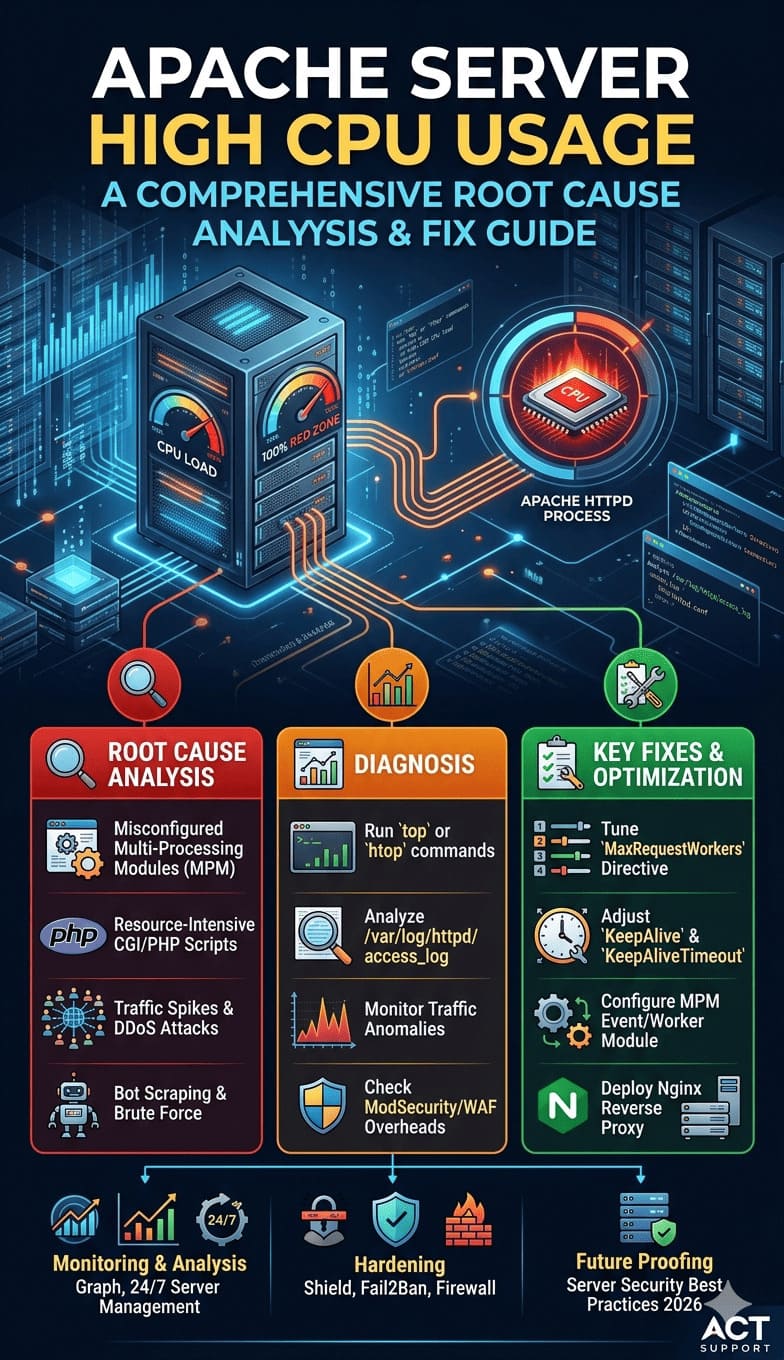
Read moreApache Server High CPU Usage: A Comprehensive Root Cause Analysis and Fix Guide
cPanel & WHM,IT Management,Linux General,Server Management,Server Management Services,What you need to Know: To fix Apache server high CPU usage, you must tune the MPM modules, reduce KeepAliveTimeout to 3 seconds, and optimize MaxRequestWorkers to prevent process loops. To resolve this, engineers must tune the MaxRequestWorkers directive, optimize KeepAlive settings, and identify bottlenecked PHP-FPM processes or database queries. Implementing proactive Linux server management…
Read moreFTP vs SFTP vs SSH: Which Protocol Is Best for Hosting?
Firewall/Iptables/Security,IT Management,Linux/Windows Support,FTP vs SFTP vs SSH are the three most commonly used protocols for file transfer and server access, but they differ significantly in security, performance, and real-world usage. FTP is a legacy protocol that transfers data in plain text, while SFTP and SSH provide encrypted communication, making them the preferred choice for modern hosting environments.…
Read moreOptimizing Virtual Data Centers: Infrastructure Engineering Performance Tips.
Cloud Infrastructure,IT Infrastructure,IT Management,Virtualization,Introduction: Why Virtual Data Center Performance Optimization Is Critical Virtual data centers (VDCs) power modern digital infrastructure, supporting everything from SaaS platforms to enterprise applications. However, many organizations struggle with how to optimize virtual data center performance, assuming that virtualization automatically guarantees efficiency. In reality, infrastructure engineers consistently observe performance degradation when systems lack proper…
Read moreWhat Do Technical Support Services Include? How Managed IT, Cloud & Server Support Works.
IT Infrastructure,IT Management,Introduction: Technical support services include proactive server monitoring, infrastructure management, troubleshooting, security hardening, cloud operations, and 24/7 incident response handled by experienced engineers to ensure high uptime and performance. In real-world environments, technical support is not limited to fixing issues; instead, it involves continuously monitoring servers, optimizing resources, securing systems, and preventing downtime before it…
Read moreHow Providers Monitor Thousands of Servers: Scalable Architecture Insights
IT Management,Managed Services IT,outsourced web hosting support,Scaling Challenges: The Need for Multi-Layer Monitoring Modern hosting providers manage vast infrastructure environments, often operating hundreds to thousands of Linux and Windows servers. These platforms support a wide range of services, including shared hosting accounts, SaaS applications, e-commerce platforms, enterprise APIs, and cloud workloads—making reliability and performance critical. Downtime can have serious financial and…
Read moreScaling Safely: Why Managed Cloud Server Monitoring is Critical for Business Continuity
Cloud Infrastructure,IT Management,Server Management,Why Monitoring is No Longer Optional for Cloud Infrastructure In modern digital infrastructure, application availability is directly tied to business continuity. Whether organizations operate SaaS platforms, high-traffic e-commerce applications, or web hosting platforms, even a few minutes of server downtime can result in lost revenue, operational disruption, and reputational damage. As applications increasingly migrate to…
Read moreBeyond the “Slow” Sign: The Infrastructure Team’s Guide to Linux Performance Bottlenecks
IT Management,Linux General,Server Management,Linux is the bedrock of modern digital services, powering over 70% of the world’s web servers. But even the most robust infrastructure can hit a wall. For DevOps and infrastructure teams, “the server is slow” is a high-stakes puzzle where every second of latency impacts the bottom line. Identifying bottlenecks isn’t just about running a…
Read more