Overview
For years, browsers have been treated as a safe and neutral layer between users and the internet. However, that assumption no longer holds true in today’s complex digital environment.
Modern browsers are deeply integrated with business systems, cloud platforms, and sensitive data workflows. Recent AI-driven discoveries have revealed that many vulnerabilities were always present but remained undetected due to limitations in traditional security approaches.
The Problem: Security Was Built for Simplicity, Not Complexity
Browsers like Firefox undergo continuous security testing, patching, and auditing. Despite this, high-severity vulnerabilities continue to emerge regularly.
The reason is simple: browsers have evolved into complex systems that function as identity gateways, SaaS access layers, and extension ecosystems.
Each additional feature increases usability but also introduces new risks, especially when different components interact in unexpected ways.
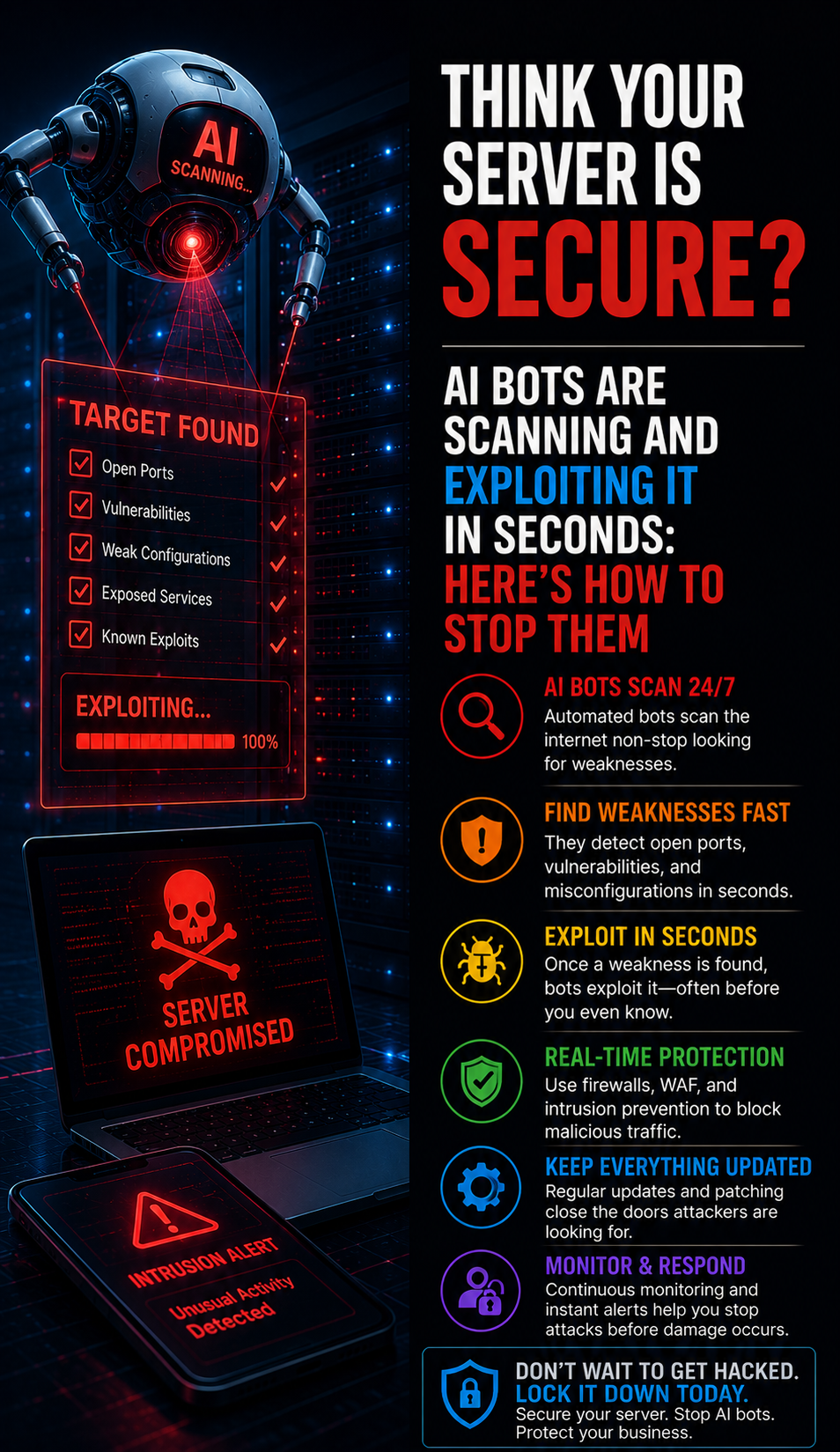
Where Traditional Security Falls Short
Traditional security focuses on identifying known threats and isolated vulnerabilities. However, modern attacks exploit interactions between multiple components rather than single points of failure.
A feature may be secure individually but become vulnerable when combined with extensions, permissions, or specific user behaviors.
This creates a structural blind spot where attackers can exploit gaps that standard testing methods fail to detect.
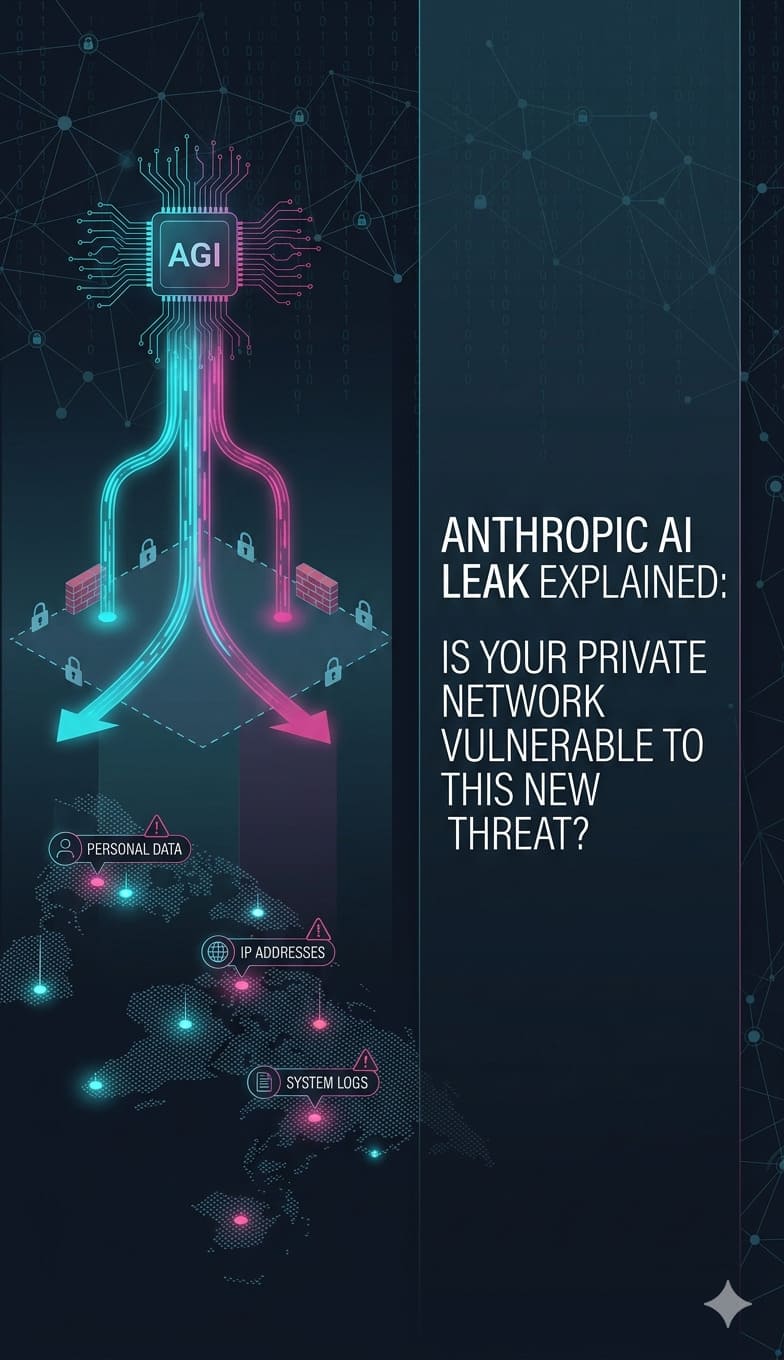
What AI Is Changing in Cybersecurity
AI is transforming cybersecurity by shifting from static validation to behavioral analysis.
Instead of asking:
👉 “Is this component secure?”
AI asks:
👉 “How does this behave in combination with everything else?”
This allows AI to:
-
identify abnormal interaction patterns
-
detect inconsistencies across environments
-
surface low-signal vulnerabilities at scale
-
prioritize risks based on real-world impact
The result is not just faster detection.
It is deeper visibility into risk that previously went unnoticed.
This is why AI is not just an improvement.
It is a necessary evolution in cybersecurity strategy.
AI-Powered Cybersecurity
Your Browser Is an Attack Surface.
Is Your AI Defense Ready?
Traditional security misses what AI catches — hidden interaction-based vulnerabilities that bypass static testing. ACTSupport’s AI-driven threat detection monitors behavioral patterns across your environment before they become breaches.
Why This Is a Business-Level Risk
Browser vulnerabilities are not confined to technical teams.
They directly impact:
-
access control
-
customer data security
-
operational continuity
-
internal system integrity
A single exploited browser flaw can lead to:
-
credential compromise
-
session hijacking
-
unauthorized administrative access
-
data exposure across platforms
And because browsers are deeply embedded in daily workflows, they provide attackers with low-friction, high-impact entry points.
This is not a theoretical risk.
It is an operational vulnerability.
What Organizations Need to Do Now
Organizations must treat browsers as a core part of their security infrastructure.
-
Treat the Browser as a Security Layer
The browser should be managed with the same discipline as servers, endpoints, and networks.
-
Control of the Extension Ecosystem
Unregulated extensions are one of the most overlooked attack surfaces.
- Audit all extensions
- Remove Unnecessary Tools
- Restrict permissions aggressively
-
Enforce Identity-Level Protection
- Multi-factor authentication should be mandatory
- Session control should be monitored
- Access should follow Zero Trust principles
-
Separate Environments
Work and personal usage should never share the same browser profile.
-
Monitor Behavior, Not Just Systems
Security is no longer about static configurations.
It is about detecting unusual patterns in real time.
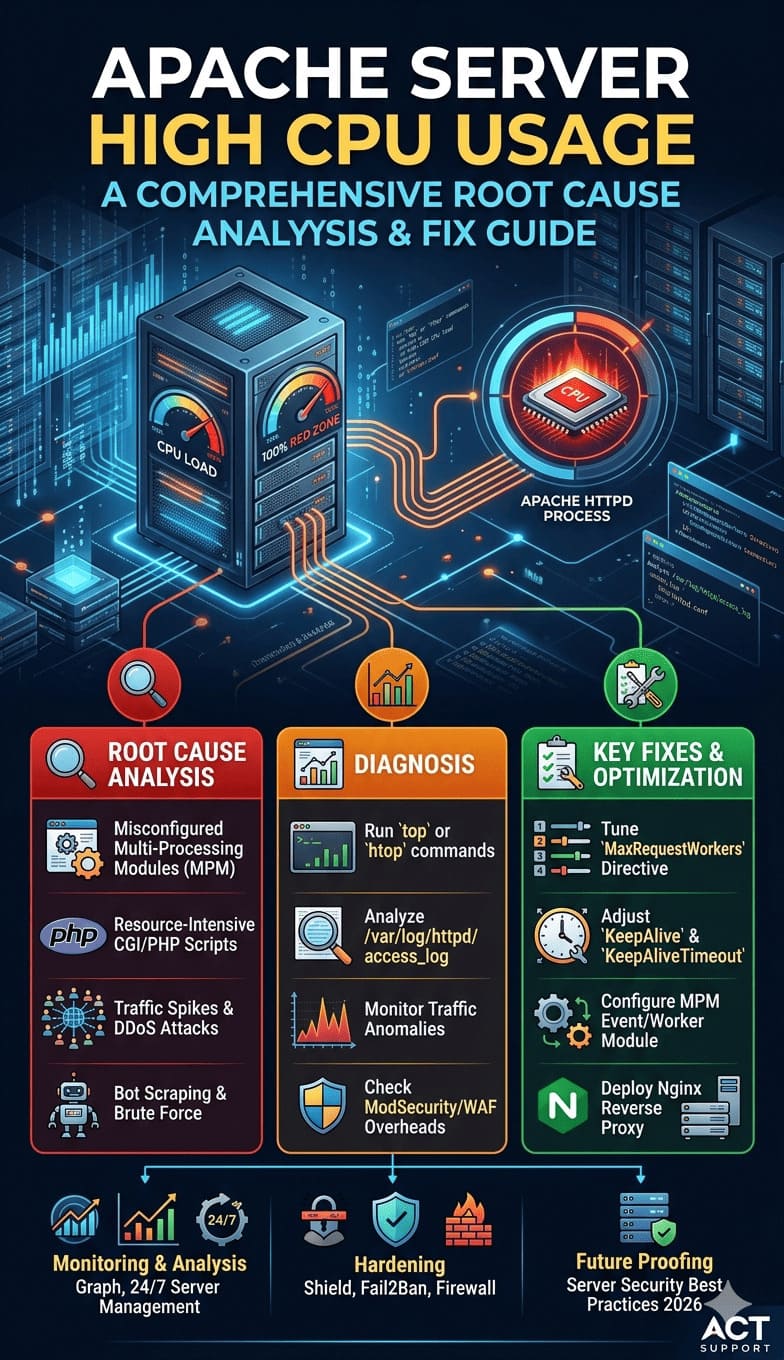
A Practical Browser Security Framework
Organizations looking to strengthen browser-level security should:
-
enforce automatic browser updates
-
restrict extension installation policies
-
disable unnecessary permissions
-
implement session monitoring
-
isolate privileged access environments
-
train teams on browser-based attack patterns
These are not advanced strategies.
They are baseline requirements in a modern threat environment.
Why This Matters for ActSupport
This shift in browser security aligns directly with how modern cybersecurity services need to evolve.
At ActSupport, the focus is not just on protecting infrastructure, but on securing every layer of access including the browser, where most real-world interactions happen.
This includes:
-
proactive vulnerability management
-
endpoint and access security
-
incident response readiness
-
continuous monitoring of user-level activity
Because in today’s environment, security failures rarely start at the server.
They start where access begins.
Enterprise Cybersecurity
Browser Flaws Are Business Risks.
Protect Every Access Layer.
A single exploited browser vulnerability can compromise credentials, hijack sessions, and expose customer data across platforms. ActSupport’s enterprise cybersecurity services secure every layer — from access control and extension management to Zero Trust enforcement and real-time monitoring.
Conclusion
AI has not introduced new risks but has made existing vulnerabilities more visible.
Organizations must evolve their security strategies and treat browsers as an active part of their security architecture.