Your VPN Is the Unlocked Back Door Hackers Are Walking Through Right Now
Cloud Infrastructure,cyber security,IT Infrastructure,Overview For a long time, VPNs were treated like the gold standard of remote access. If someone connected through the VPN, they were considered “inside” the network and therefore safe to trust. That model worked when offices were fixed, users were limited, and applications lived in one place. That world is gone. Today, employees work…
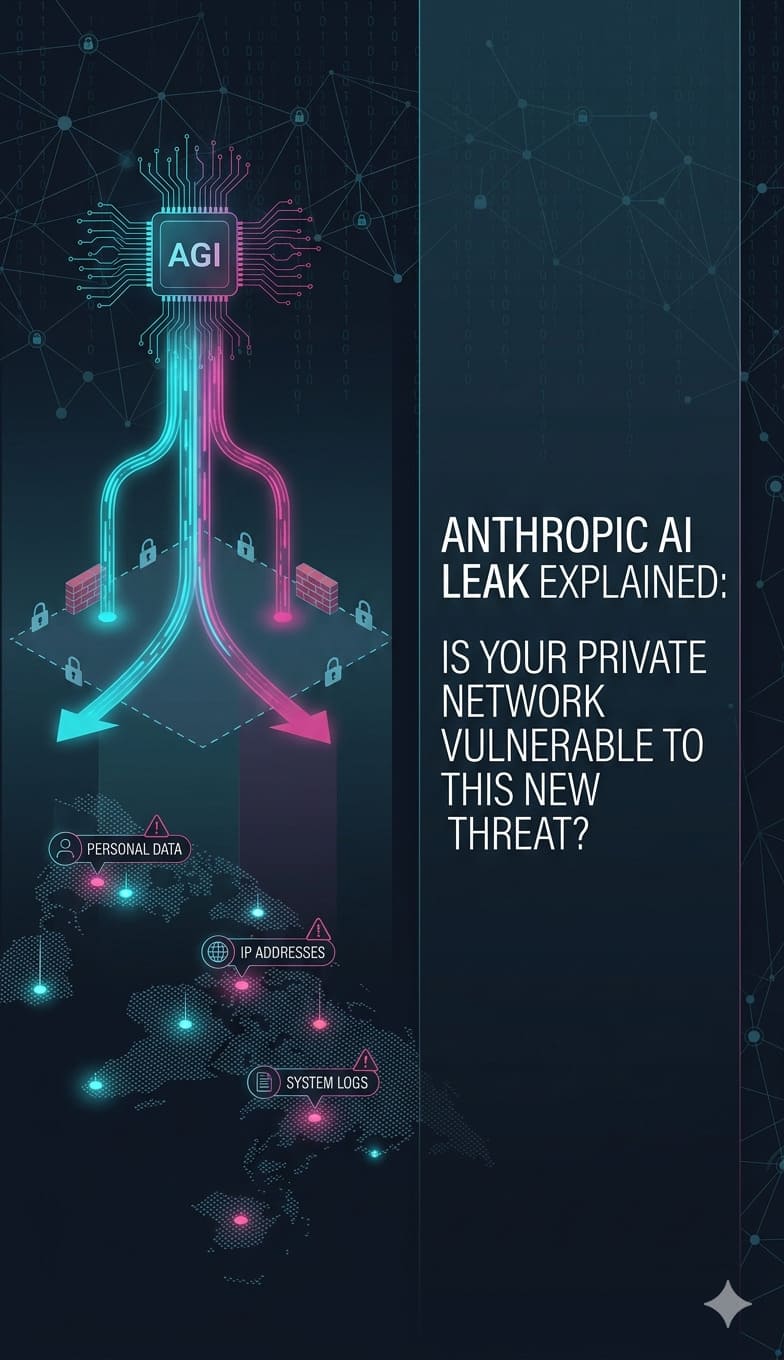
Read moreAnthropic AI Leak Explained: Is Your Private Network Vulnerable to This New Threat?
AI in IT Support & Infrastructure,IT Infrastructure,IT Management,Summary: The accidental exposure of Anthropic’s Claude Code source code in April 2026 has introduced severe risks, including CVE-2026-35022, which allows remote code execution via shell metacharacter injection. This leak gives hackers a roadmap to bypass security filters and hijack agentic AI systems to exfiltrate API keys, SSH credentials, and environment variables. To fix these…
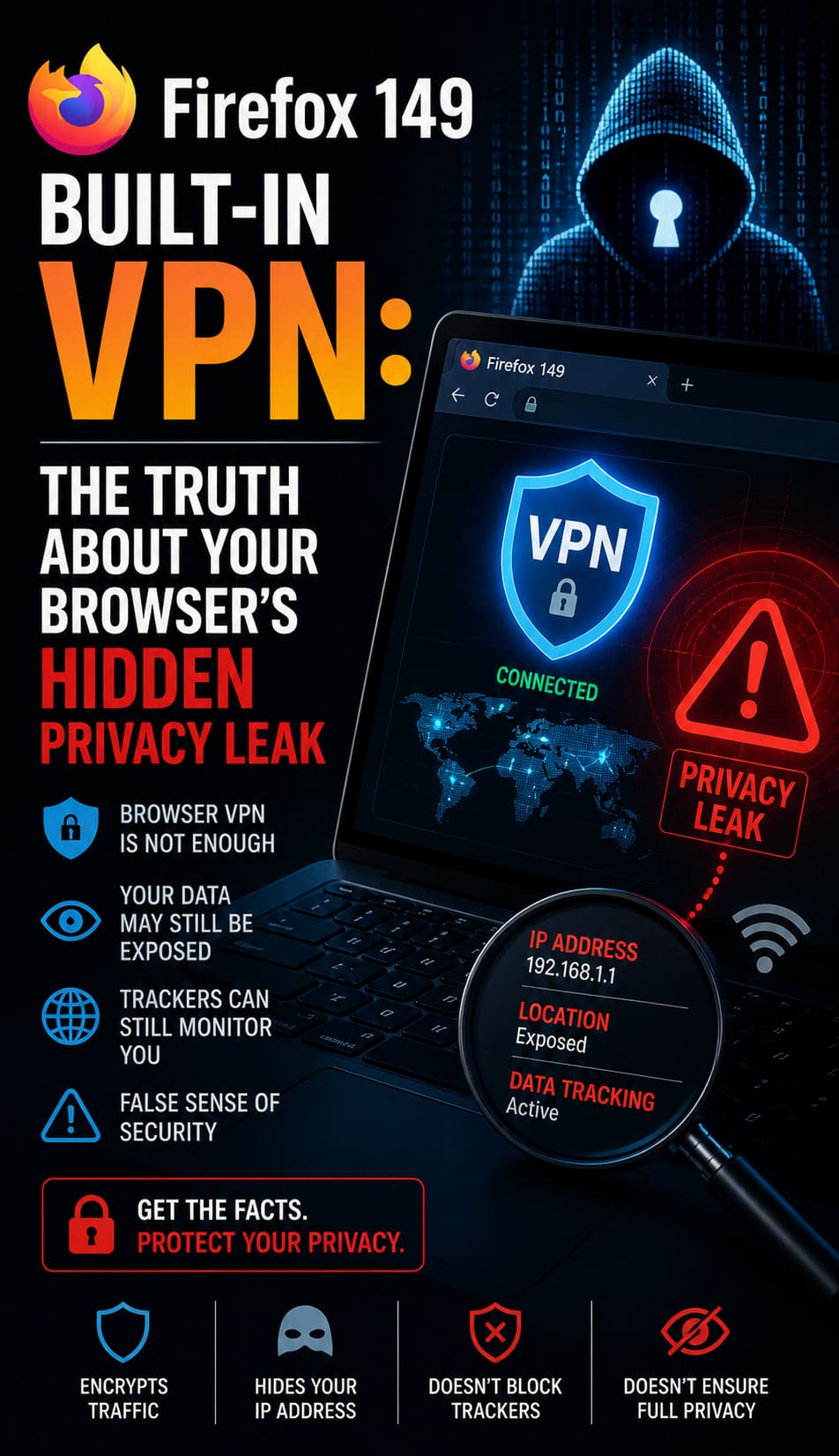
Read moreFirefox 149 Built-In VPN: The Truth About Your Browser’s Hidden Privacy Leak
Firewall/Iptables/Security,IT Infrastructure,Linux General,What You Need to Know: Firefox 149 Built-In VPN Direct Impact Analysis Firefox 149 features a native, built-in browser VPN designed to stop the “Hidden Privacy Leak” where websites and ISPs harvest your real IP address. Unlike standard private browsing modes that only clear local history, this integrated proxy creates a secure, zero-log tunnel for…
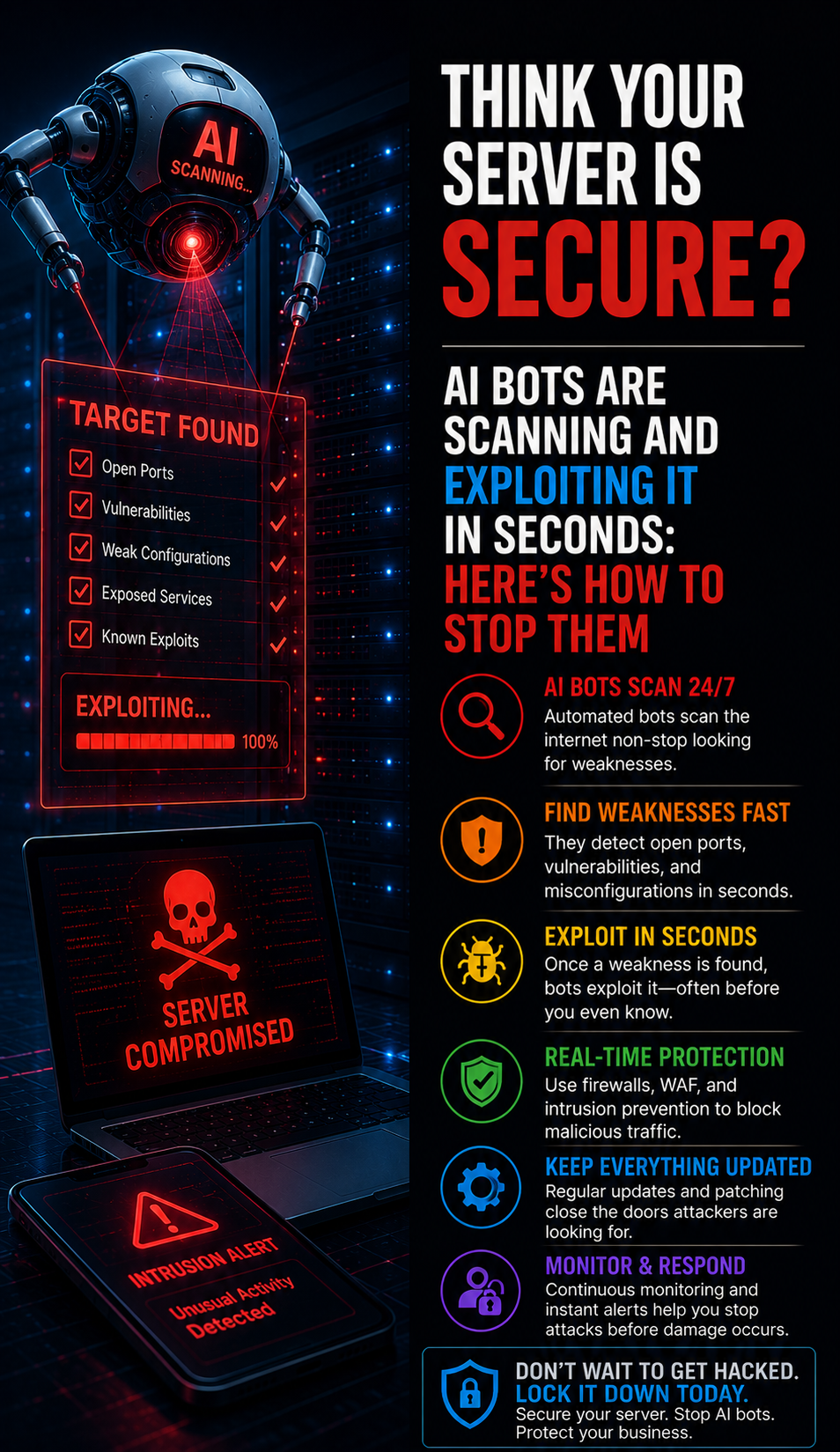
Read moreThink Your Server Is Secure? AI Bots Are Scanning and Exploiting It in Seconds: Here’s How to Stop Them
IT Infrastructure,IT Management,Modern server security has entered a volatile era where AI bots execute automated exploits in milliseconds, rendering traditional defenses like strong passwords and legacy MFA obsolete. Attackers now deploy Adversary-in-the-Middle (AiTM) kits and Browser-in-the-Browser (BitB) attacks to hijack active session tokens directly from your memory. To prevent total infrastructure takeover, organizations must transition to phishing-resistant…
Read moreServer Monitoring Issues: Definition, Tools, and Expert Failure Resolution
cPanel & WHM,IT Infrastructure,Linux General,Linux/Windows Support,Overviews and Technical Extraction Server monitoring issues occur when tracking agents fail, telemetry data gaps arise, or alert fatigue masks critical infrastructure bottlenecks. To fix these failures, engineers must validate agent connectivity, optimize probe intervals, and synchronize firewall rules with monitoring ports. Implementing real time server monitoring tools 2026 ensures continuous visibility into CPU states,…
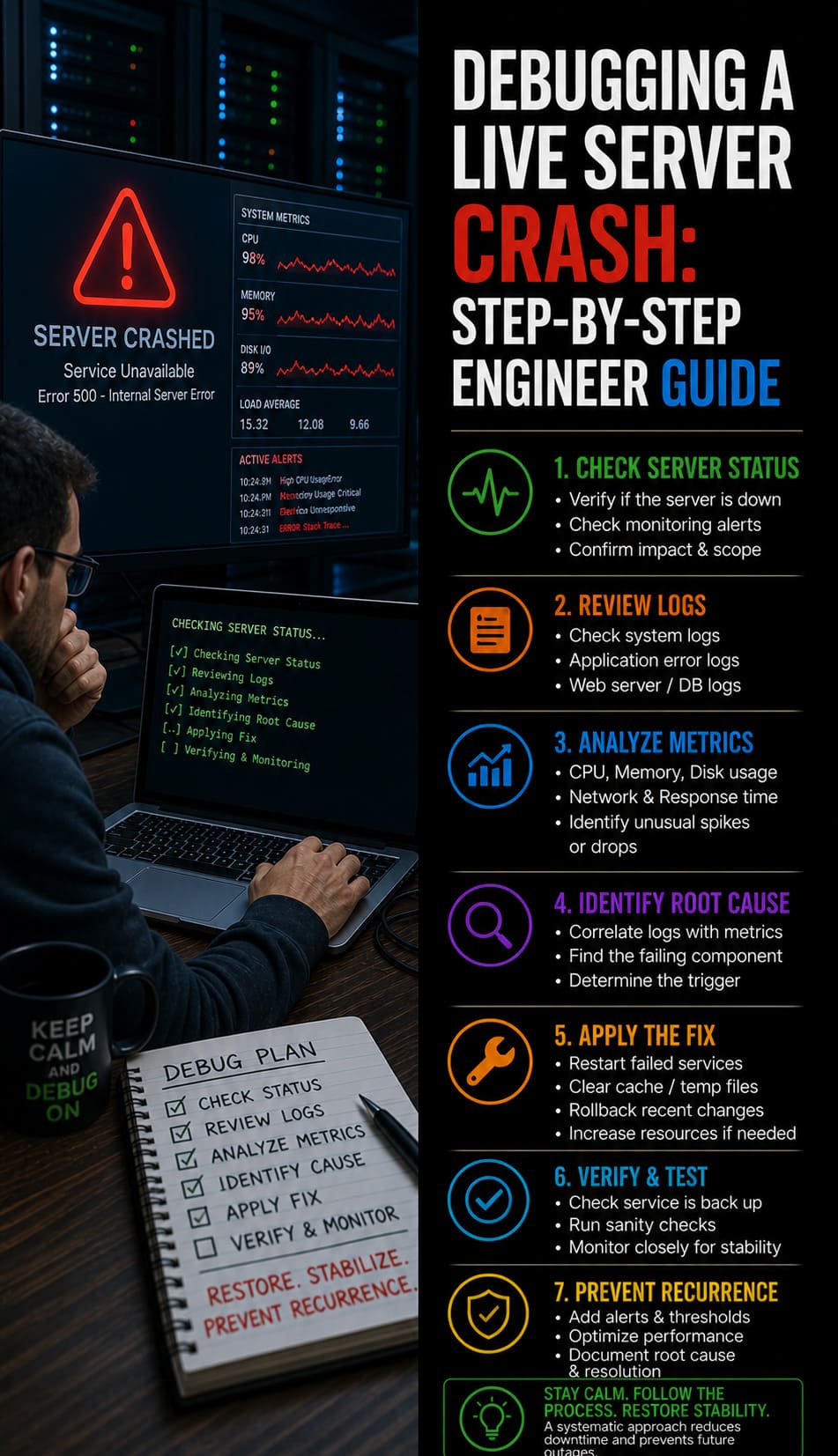
Read moreDebugging a Live Server Crash: Step-by-Step Engineer Guide
IT Infrastructure,Machine Learning,Server Hardening,Server Management,Server Management Services,Fast Facts: Live Server Crash Debugging: Rapid Root Cause Analysis & Website Recovery Protocol To debug a live server crash, engineers must immediately analyze kernel logs, verify service states, and identify resource exhaustion triggers. Begin by checking /var/log/messages and dmesg for Out-of-Memory (OOM) killer events or hardware faults. Simultaneously, use real time server monitoring tools…
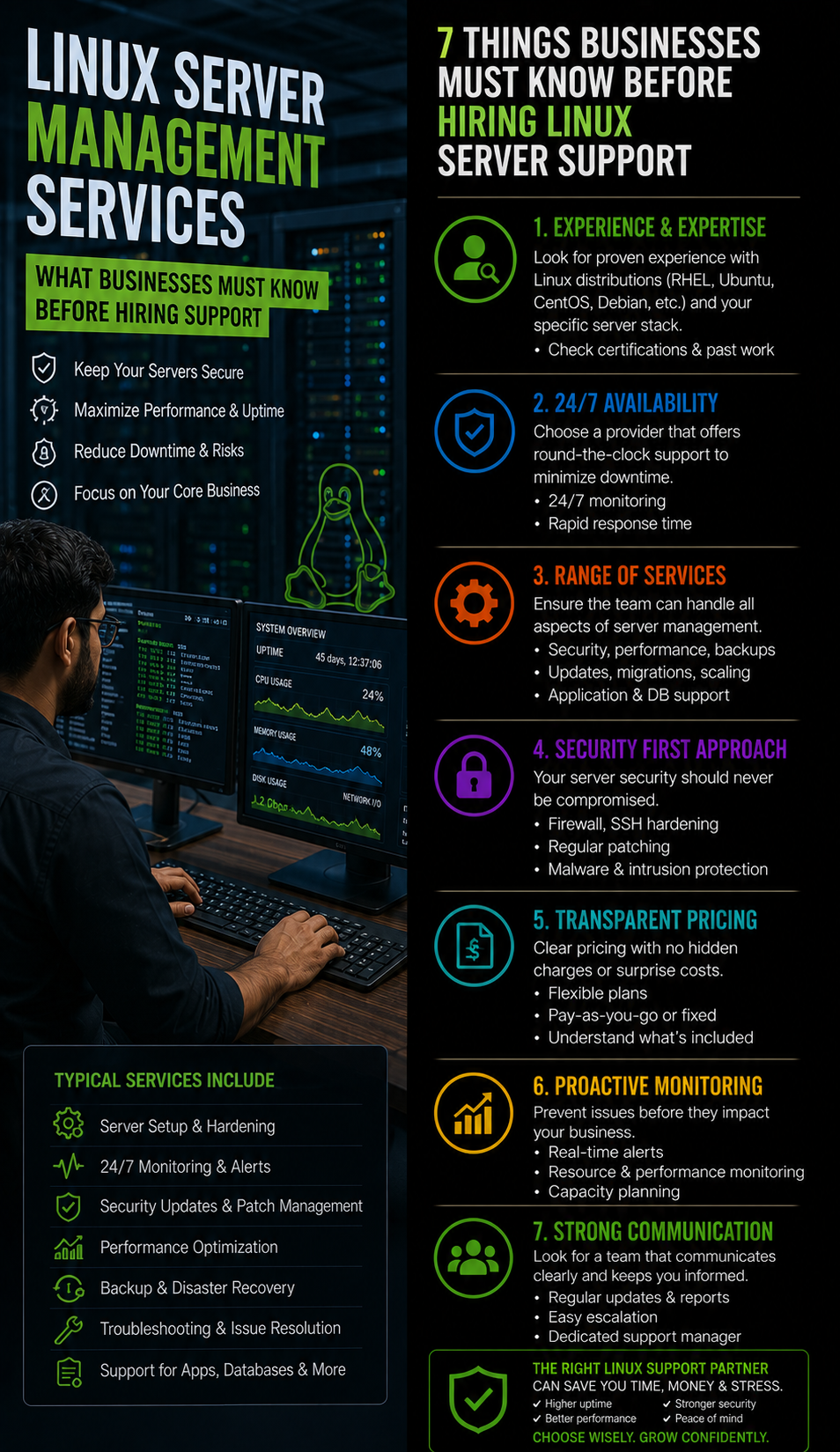
Read moreLinux Server Management Services: What Businesses Must Know Before Hiring Support
IT Infrastructure,Linux General,Linux/Windows Support,Infrastructure Resilience: Solving the Lifecycle of Server Decay: Linux server management services involve the continuous oversight, securing, and optimization of server infrastructure to ensure maximum business uptime. We found that most production outages stem from minor misconfigurations, such as incorrect firewall rules or service-level failures like the ECONNREFUSED error. You should prioritize proactive monitoring and…
Read moreOptimizing Virtual Data Centers: Infrastructure Engineering Performance Tips.
Cloud Infrastructure,IT Infrastructure,IT Management,Virtualization,Introduction: Why Virtual Data Center Performance Optimization Is Critical Virtual data centers (VDCs) power modern digital infrastructure, supporting everything from SaaS platforms to enterprise applications. However, many organizations struggle with how to optimize virtual data center performance, assuming that virtualization automatically guarantees efficiency. In reality, infrastructure engineers consistently observe performance degradation when systems lack proper…
Read moreWhat Do Technical Support Services Include? How Managed IT, Cloud & Server Support Works.
IT Infrastructure,IT Management,Introduction: Technical support services include proactive server monitoring, infrastructure management, troubleshooting, security hardening, cloud operations, and 24/7 incident response handled by experienced engineers to ensure high uptime and performance. In real-world environments, technical support is not limited to fixing issues; instead, it involves continuously monitoring servers, optimizing resources, securing systems, and preventing downtime before it…
Read moreThe SaaS 99.99% Blueprint: Managed Infrastructure & Disaster Recovery
backup and recovery,IT Infrastructure,Managed Services IT,SaaS Operations,For modern SaaS platforms, uptime is not simply a performance metric. It is a fundamental business requirement that directly affects revenue, customer trust, and product reliability. A SaaS platform that experiences frequent outages quickly loses customer confidence. Even a few minutes of downtime can interrupt business workflows, delay customer transactions, and create support escalations. Industry…
Read more