How Do Virtual Data Center Support Services Ensure Enterprise Infrastructure Excellence and Reliability?
Server Management,Server Management Services,Summary: Virtual Data Center Support Services for Modern Enterprises Virtual Data Center Support plays a crucial role in modern IT infrastructure management by ensuring that virtualized environments remain stable, secure, and highly efficient. As organizations increasingly adopt virtualization technologies and hybrid cloud models, the complexity of managing compute, storage, and network resources has significantly increased.…
Read more15 Common Web Hosting Problems Every Business Faces in 2026.
Server Management Services,Web Hosting Providers,Introduction to Modern Web Hosting Challenges in 2026 Web hosting infrastructure in 2026 has become significantly more complex compared to previous years. Businesses today depend heavily on websites, SaaS applications, APIs, cloud platforms, eCommerce stores, and remote digital operations for revenue generation and customer engagement. Even a few minutes of downtime can result in lost…
Read moreDual-Core vs Quad-Core vs Hexa-Core vs Octa-Core: Which Processor is Best for Gaming in 2026?
Server Hardening,Server Management,Server Management Services,Understanding Modern Processor Technology in 2026 The processor market has changed dramatically over the last few years. Earlier, users only compared dual-core vs quad-core processors, but modern computing now includes hexa-core, octa-core, and even AI-powered processors built specifically for gaming, streaming, content creation, virtualization, and multitasking. In 2026, modern CPUs from Intel Core Ultra, AMD…
Read moreHow ActSupport Delivers 24×7 Server Management, Monitoring, and DevOps Support for High-Availability Infrastructure
Server Hardening,Server Management,Server Management Services,Introduction: Why High Availability Fails in Real Infrastructure Modern infrastructure does not fail suddenly. It degrades silently long before users notice downtime. CPU spikes remain unnoticed until applications freeze. Disk usage grows gradually until writes fail. Database connections saturate until login systems collapse. Network latency increases until APIs start timing out. High availability fails when…
Read moreWhat CTOs Look for Before Hiring a Managed Infrastructure Support Company
Server Management,Server Management Services,Managed server support services require a high degree of technical competence and cultural alignment to successfully bridge the gap between internal development cycles and external infrastructure stability. When a CTO evaluates a potential partner, they do not simply look for a list of supported technologies; they look for operational maturity, proactive risk mitigation, and a…
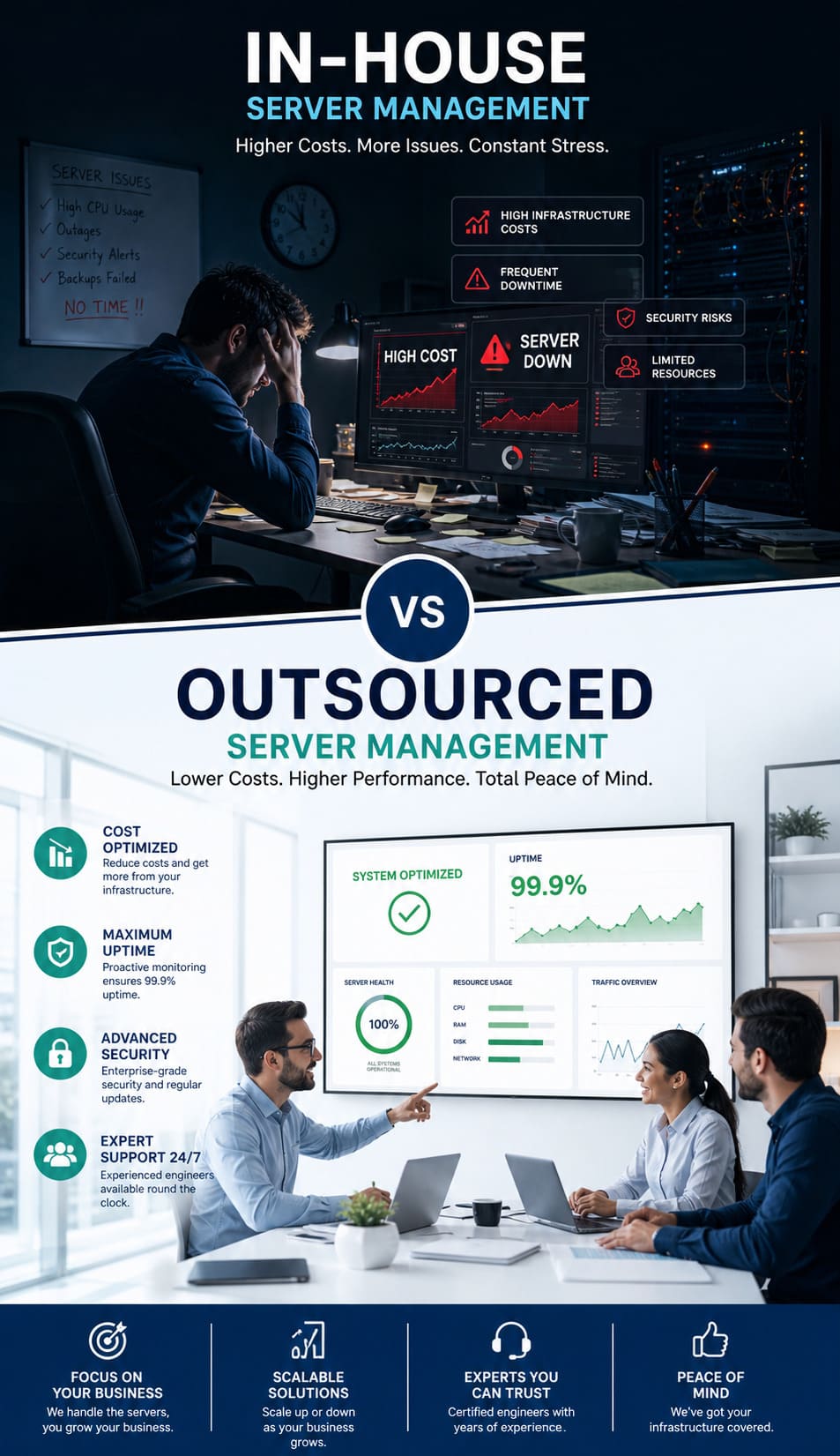
Read moreIn-House vs Outsourced Server Management: Fixing High Server Costs & Downtime
Server Management,Server Management Services,Summary Managing infrastructure in-house often leads to rising server costs and unexpected downtime. This happens due to the high cost of specialized talent and the need for 24/7 monitoring. Outsourced server management offers a scalable and cost-effective solution. It gives you access to senior-level engineers and proactive maintenance. All this comes at a fraction of…
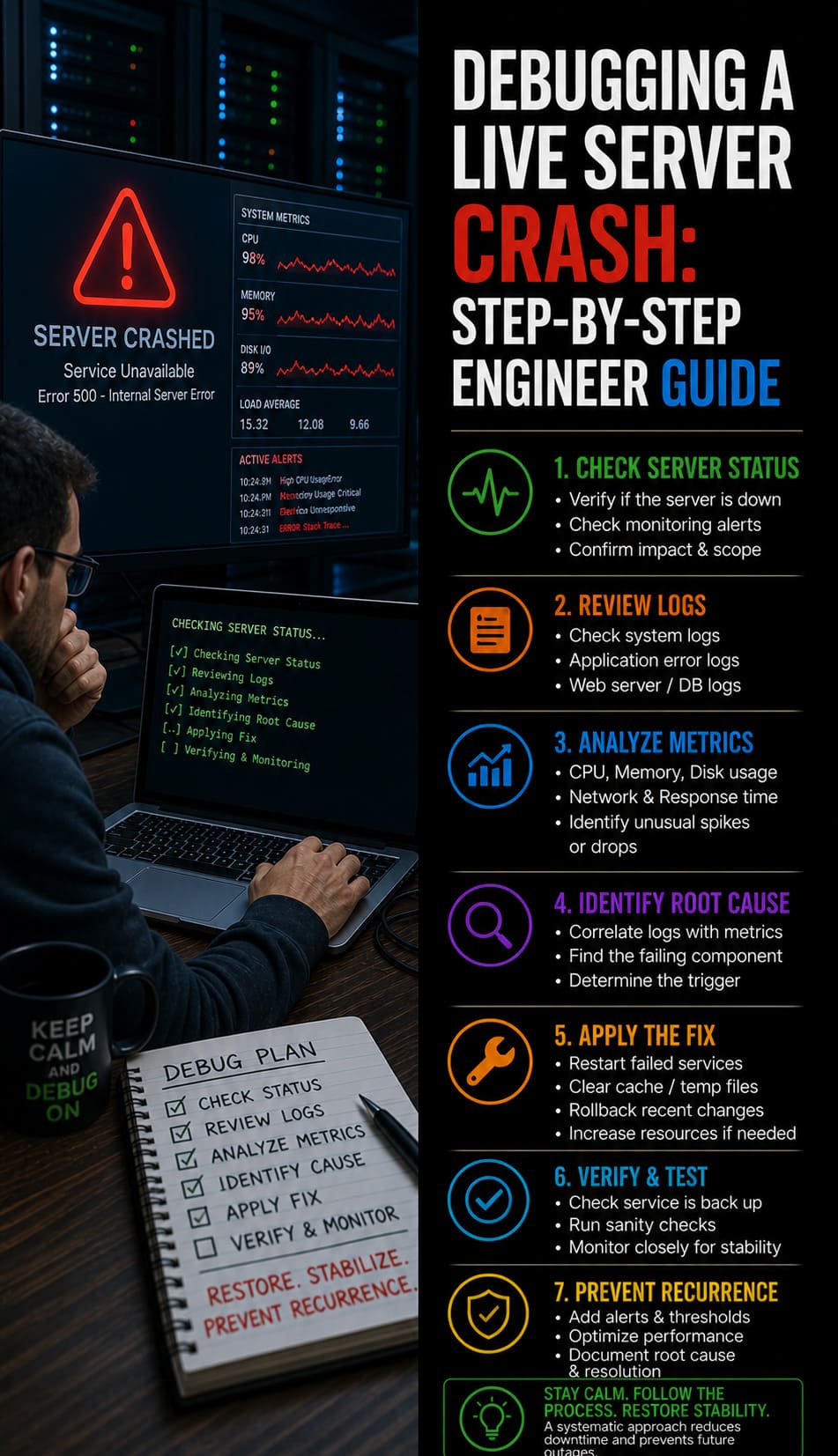
Read moreDebugging a Live Server Crash: Step-by-Step Engineer Guide
IT Infrastructure,Machine Learning,Server Hardening,Server Management,Server Management Services,Fast Facts: Live Server Crash Debugging: Rapid Root Cause Analysis & Website Recovery Protocol To debug a live server crash, engineers must immediately analyze kernel logs, verify service states, and identify resource exhaustion triggers. Begin by checking /var/log/messages and dmesg for Out-of-Memory (OOM) killer events or hardware faults. Simultaneously, use real time server monitoring tools…
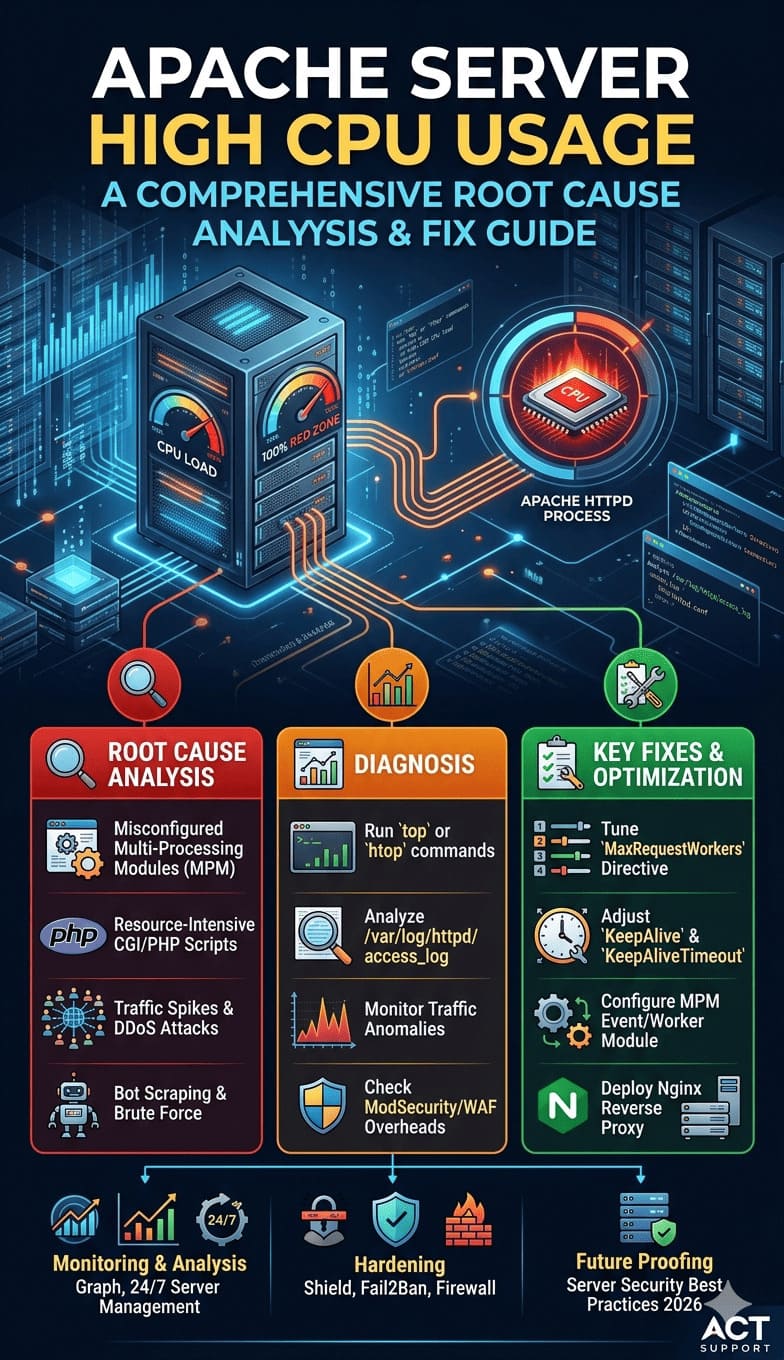
Read moreApache Server High CPU Usage: A Comprehensive Root Cause Analysis and Fix Guide
cPanel & WHM,IT Management,Linux General,Server Management,Server Management Services,What you need to Know: To fix Apache server high CPU usage, you must tune the MPM modules, reduce KeepAliveTimeout to 3 seconds, and optimize MaxRequestWorkers to prevent process loops. To resolve this, engineers must tune the MaxRequestWorkers directive, optimize KeepAlive settings, and identify bottlenecked PHP-FPM processes or database queries. Implementing proactive Linux server management…
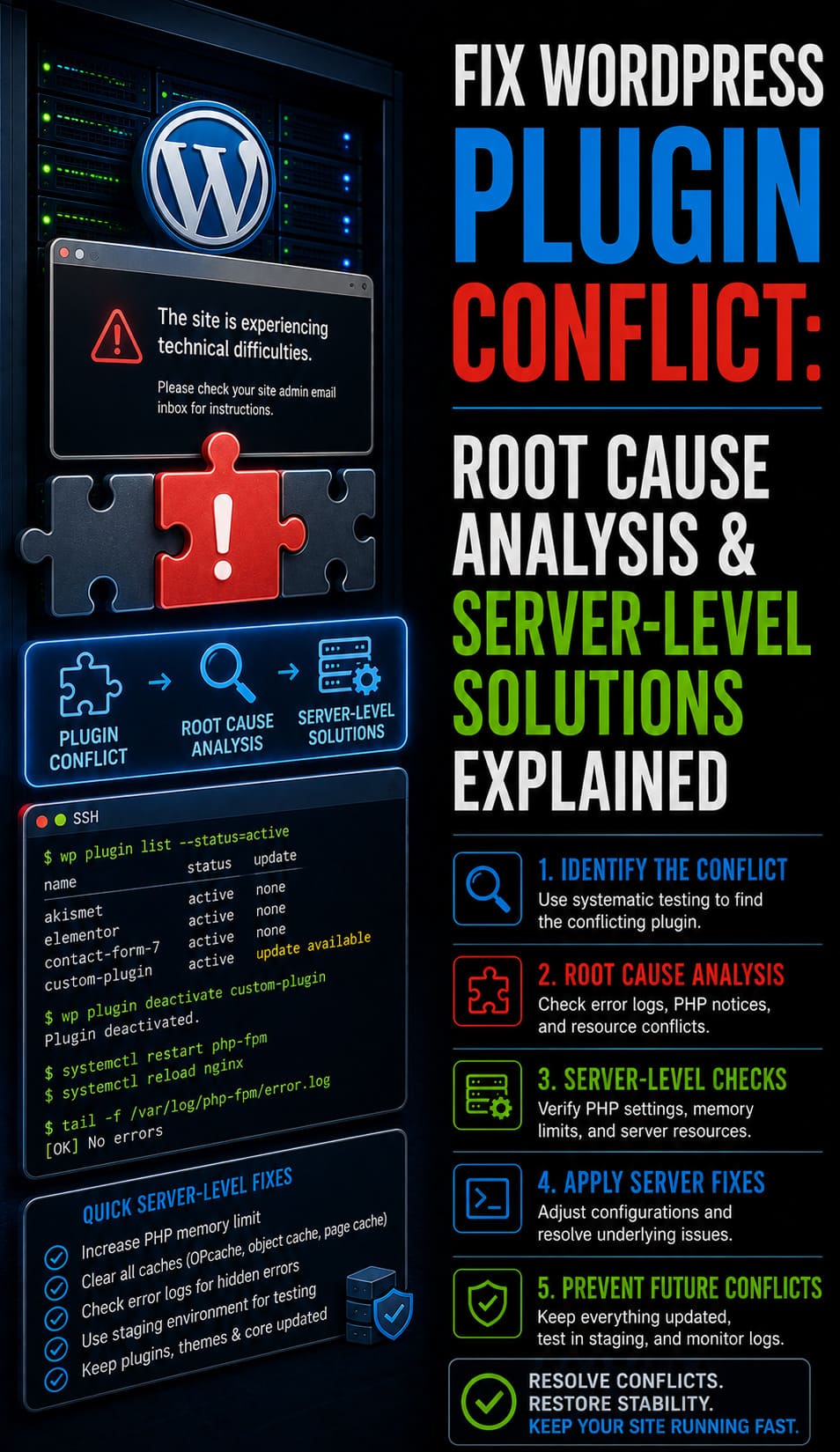
Read moreFix WordPress Plugin Conflict: Root Cause Analysis & Server-Level Solutions Explained
Linux General,Server Management Services,Wordpress,Wordpress,Infrastructure engineers fix WordPress plugin conflicts by performing deep root cause analysis at the server level rather than relying on trial-and-error dashboard clicks. This process involves isolating PHP execution errors, database deadlocks, and resource contention issues using command-line tools and system logs. Resolving a Fix WordPress Plugin Conflict scenario requires a systemic approach to identify…
Read moreEssential Server Security Best Practices: Protecting Production Infrastructure
Server Management,Server Management Services,Server security best practices involve implementing a multi-layered defense strategy including regular patching, robust identity management, network micro-segmentation, and continuous monitoring. These measures protect critical data from unauthorized access while ensuring system availability across Linux and Windows environments. By adopting a “Zero Trust” approach, infrastructure architects can mitigate modern cyber threats and maintain a resilient…
Read more