Google Drive Ransomware Protection: Why Your Cloud Files are Still at Risk?
backup and recovery,Cloud Infrastructure,Quick Breakdown: Google Drive Ransomware Protection Analysis Google Drive is vulnerable to automated ransomware because desktop sync clients treat encrypted files as legitimate updates, instantly mirroring corrupted data to the cloud. We found that the core risk lies in bidirectional synchronization; when a local machine is hit, the sync tool replaces clean cloud files with…
Read moreYour Backup Failed When You Needed It Most: Why Most Server Backups Don’t Work in Real Disasters (And How to Fix It)
backup and recovery,Database,Abstract: Why Backups Fail ? Server backup recovery systems fail primarily due to silent data corruption, unverified RTO/RPO metrics, and the lack of immutable storage. We found that modern “Browser-in-the-Browser” attacks bypass traditional MFA, allowing hackers to hijack session tokens and delete offsite archives in seconds. To fix this, you should build a “restoration-first” architecture…
Read moreWhy Your Server Works Fine After Restart but Slows Down Over Time
backup and recovery,Linux General,Quick Breakdown: A server slows down over time due to cumulative resource exhaustion caused by memory leaks, log file growth, and background process accumulation. While a restart temporarily restores speed by clearing the RAM and resetting the system state, it fails to fix the underlying inefficiencies. We found that most long-term performance degradation stems from…
Read moreFixing “Account Over Quota” Errors: Advanced Disk Space Management and Clean-up Automation
backup and recovery,Linux General,To fix “Account Over Quota” errors on a Linux server, administrators must identify the specific partition reaching its limit using the df -h command and locate high-capacity directories with du -sh. Resolving these errors requires clearing expired log files in /var/log, purging redundant cPanel backups, and removing orphaned session files from /tmp. Implementing automated bash…
Read moreHow to Configure Immutable cPanel Backups: Ransomware Protection via S3
backup and recovery,Cpanel,cPanel & WHM,Firewall/Iptables/Security,To implement immutable backups in cPanel, administrators configure the Backup Configuration tool to point toward an off-site S3-compatible storage provider that supports Object Lock. Enabling Object Lock in compliance mode ensures that once data reaches the remote bucket, no user or ransomware script can modify or delete the files for a predetermined retention period. This…
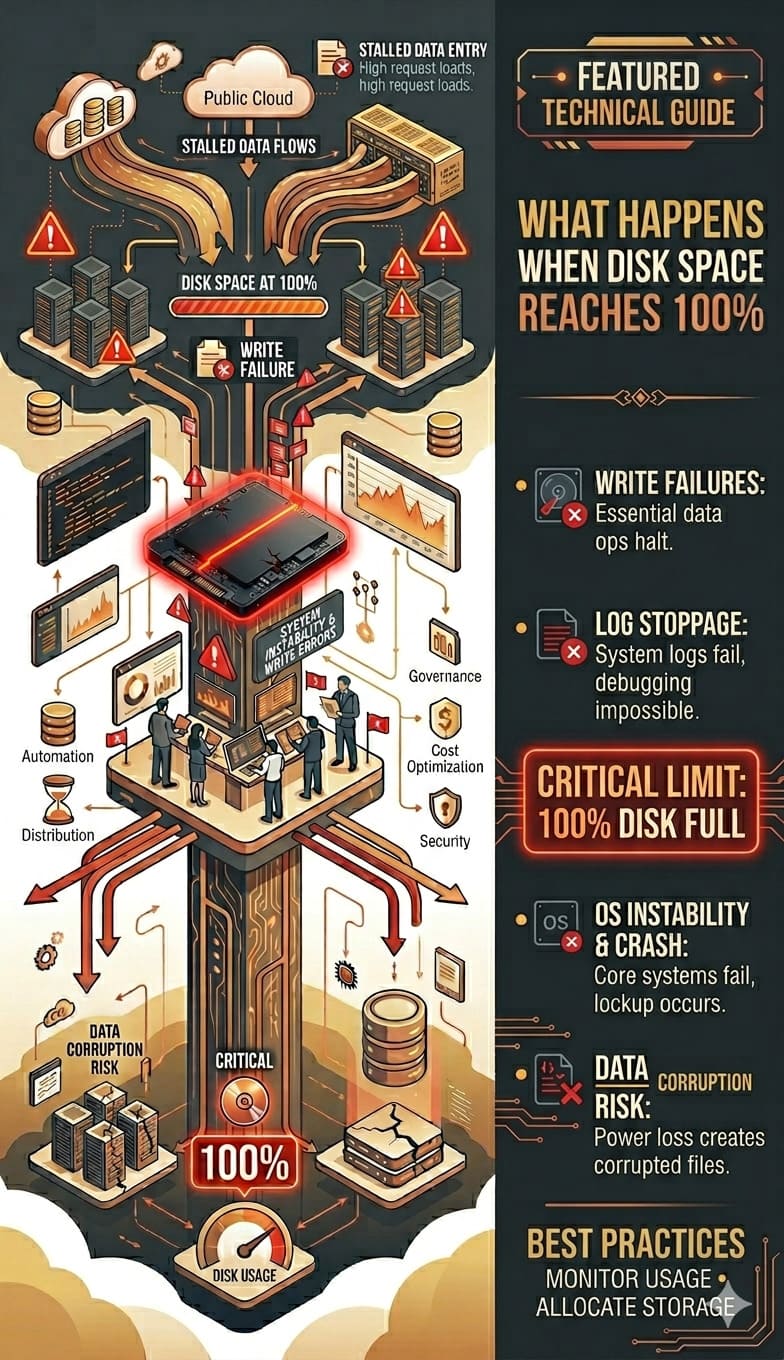
Read moreWhat Happens When Disk Space Reaches 100%
backup and recovery,Introduction: What Happens When Disk Space Reaches 100% in Real Servers When disk space reaches 100%, a server does not just slow down it begins to fail in critical ways. Applications stop writing data, databases crash or become read-only, logs fail to record events, and in many cases, services completely stop responding. This disk space…
Read moreThe SaaS 99.99% Blueprint: Managed Infrastructure & Disaster Recovery
backup and recovery,IT Infrastructure,Managed Services IT,SaaS Operations,For modern SaaS platforms, uptime is not simply a performance metric. It is a fundamental business requirement that directly affects revenue, customer trust, and product reliability. A SaaS platform that experiences frequent outages quickly loses customer confidence. Even a few minutes of downtime can interrupt business workflows, delay customer transactions, and create support escalations. Industry…
Read moreWhat Is a Network Database? Definition, Architecture, Examples & Use Cases
backup and recovery,IT Infrastructure,IT Management,Understanding the Network Database Model A network database is a type of database management system (DBMS) designed to handle complex data relationships efficiently. Unlike simple hierarchical structures, the network database model allows multiple parent-child relationships; therefore, it is ideal for applications where data is deeply interconnected. As a result, as modern enterprises generate and process…
Read moreWhy Backups Fail: Common Causes and How to Build a Reliable Backup Strategy
backup and recovery,Data is the backbone of every modern business. Whether you're running an eCommerce store, SaaS platform, or enterprise system, a reliable backup is the only insurance against disasters like server crashes, ransomware attacks, or accidental deletions.
Read moreTop BCDR Trends Redefining Backup Strategies in 2025
backup and recovery,outsourced web hosting support,Server Management Services,BCDR Is No Longer Just About Backup Backup no longer ensures survival. In today’s digital landscape, cyberattacks, hardware failures, and natural disasters strike without warning. As a result, recovery speed defines continuity. Even a short delay in operations can cause significant losses. Therefore, recovery must be seamless, and operations must resume without disruption. To achieve…
Read more