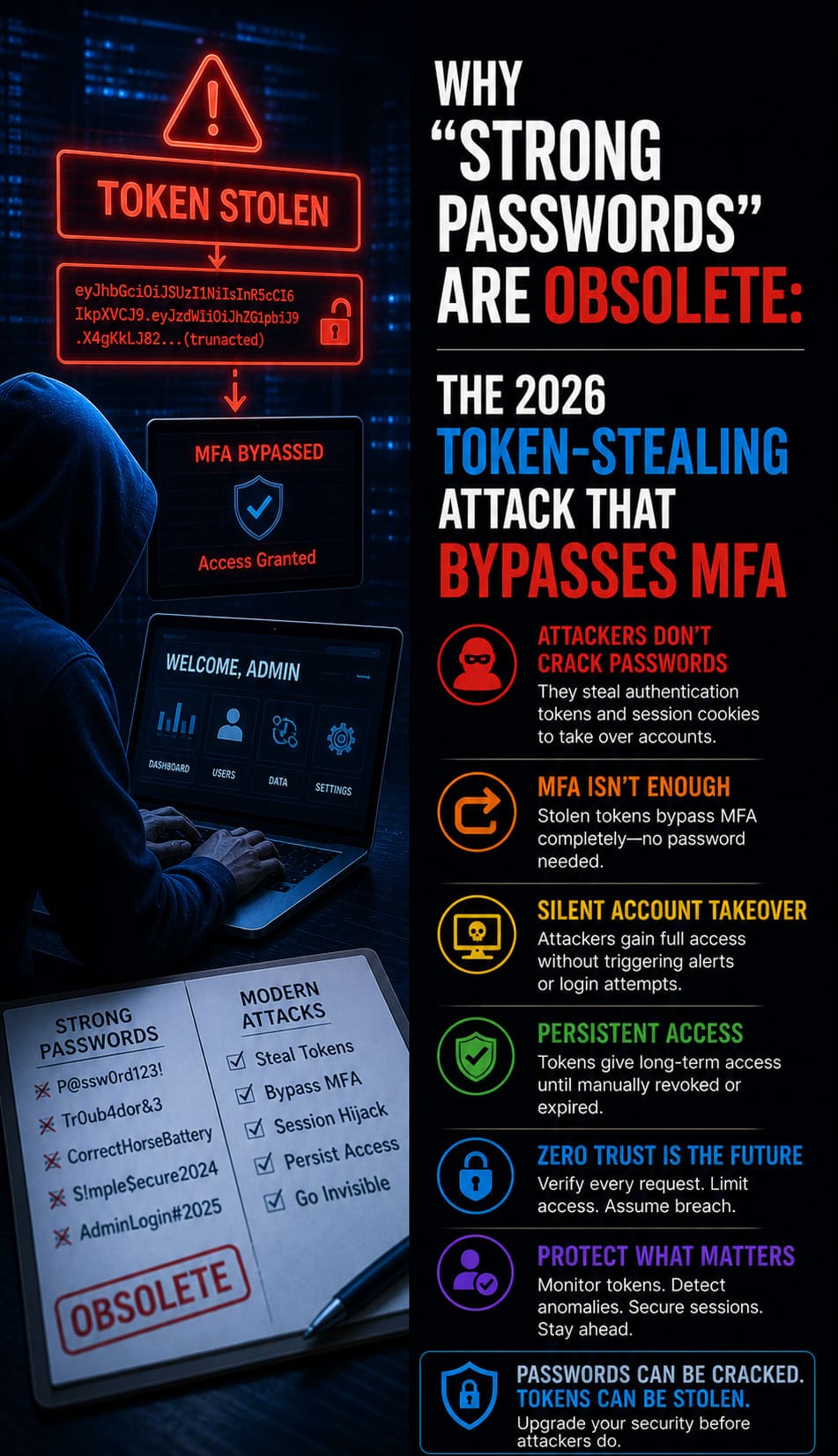
Why “Strong Passwords” Are Obsolete: The 2026 Token-Stealing Attack That Bypasses MFA
Linux General,Machine Learning,Quick Breakdown: Your Browser Is the New Security Hole Strong passwords and traditional MFA have collapsed because modern Adversary-in-the-Middle (AiTM) and Browser-in-the-Browser (BitB) attacks steal authenticated session tokens directly from browser memory. We found that phishing kits like EvilProxy now bypass 6-digit SMS codes by acting as a live proxy to capture session cookies in…
Read moreYour AI Agent Has Root Access, But Who Controls It? The Ghost Command Risk
AI in IT Support & Infrastructure,Machine Learning,Quick Insight: Leaked AI agents grant hackers root access by exposing internal source code or handshake protocols, allowing them to inject “Ghost Commands” that mimic trusted activity. We found that these exploits bypass traditional firewalls because AI agents often hold high-privilege permissions to manage cloud resources and system files. To secure your private network, you…
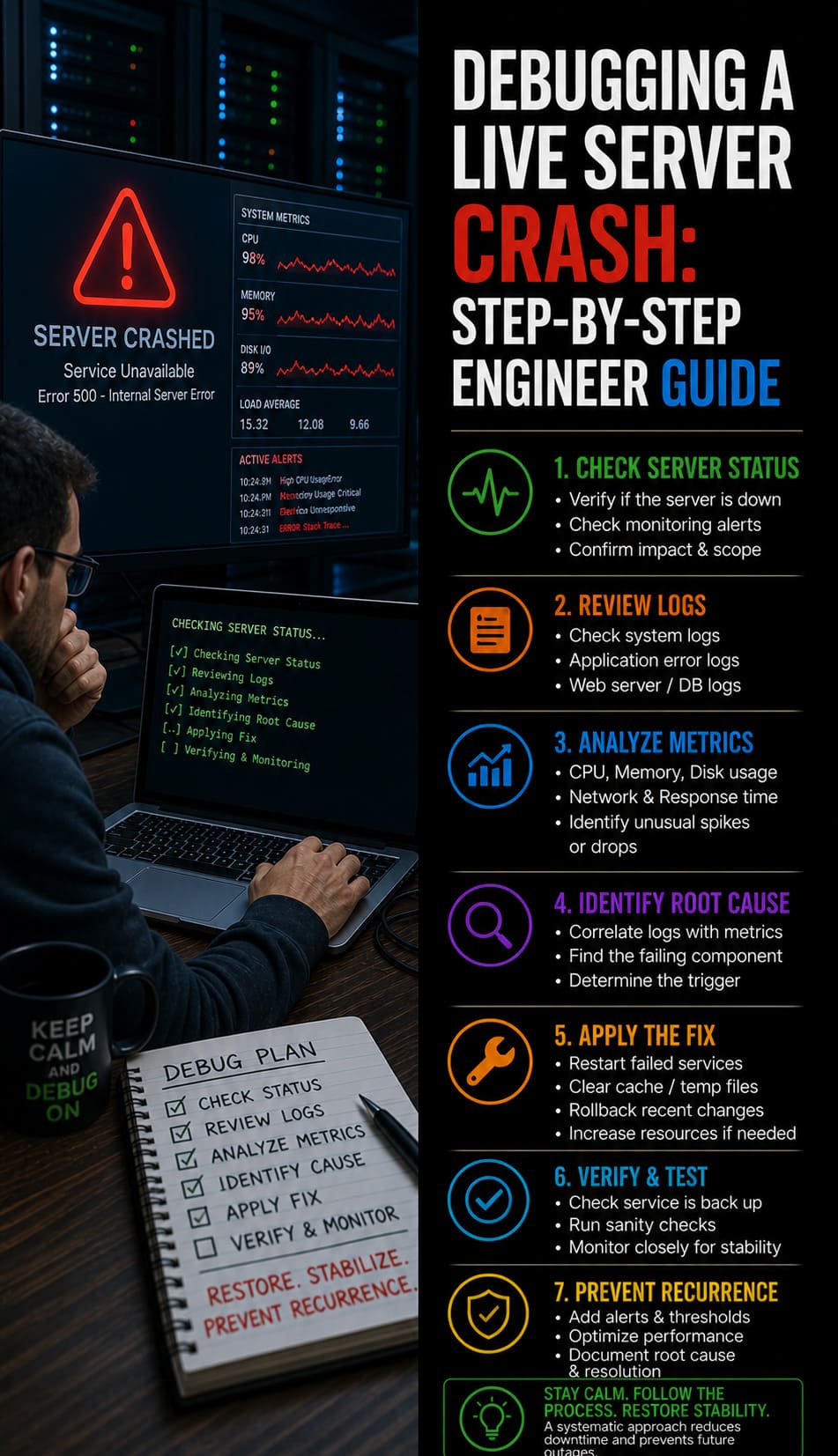
Read moreDebugging a Live Server Crash: Step-by-Step Engineer Guide
IT Infrastructure,Machine Learning,Server Hardening,Server Management,Server Management Services,Fast Facts: Live Server Crash Debugging: Rapid Root Cause Analysis & Website Recovery Protocol To debug a live server crash, engineers must immediately analyze kernel logs, verify service states, and identify resource exhaustion triggers. Begin by checking /var/log/messages and dmesg for Out-of-Memory (OOM) killer events or hardware faults. Simultaneously, use real time server monitoring tools…
Read moreRevolutionizing Server Support: How AI and AIOps Lead in 2025
AI on AWS,Machine Learning,Server Management,AI, AIOps & Zero Trust: The Future of IT Support Server support in AI, AIOps, and Zero-Trust Security is rapidly reshaping the future of IT support in 2025. As companies scale their digital operations-and with remote work becoming the norm-traditional support models are proving inadequate. Businesses now require advanced, fast, and secure server support systems…
Read more