Modern server security has entered a volatile era where AI bots execute automated exploits in milliseconds, rendering traditional defenses like strong passwords and legacy MFA obsolete. Attackers now deploy Adversary-in-the-Middle (AiTM) kits and Browser-in-the-Browser (BitB) attacks to hijack active session tokens directly from your memory. To prevent total infrastructure takeover, organizations must transition to phishing-resistant FIDO2 hardware keys and implement Continuous Access Evaluation (CAE) to cryptographically bind identities to physical hardware.
Summary: Protecting Infrastructure from Automated Token Theft
The rapid evolution of AI-driven exploitation means that a single leaked session token grants a hacker root access without ever needing to crack a password. Key defenses involve moving away from “Point-in-Time” authentication to Zero Trust architectures. FIDO2 hardware keys provide the only definitive defense against AiTM phishing by requiring a hardware-level cryptographic handshake. Additionally, enforcing Conditional Access policies that monitor IP reputation and device compliance ensures that stolen cookies cannot be replayed from unauthorized machines.
The Problem: Why Traditional MFA Fails Against AI Bots
Most infrastructure leads still rely on SMS-based MFA or Push Notifications, but these methods contain a fatal flaw: they do not verify the “origin” of the request. AI bots automate the creation of Browser-in-the-Browser (BitB) windows that look identical to legitimate login portals. When an admin enters their credentials, the bot proxies the request to the real server and intercepts the resulting session token. Because this token-stealing attack bypasses MFA, the attacker gains immediate access to cPanel, AWS Consoles, or root shells while the admin remains unaware of the breach.
The Agitation: 30 Seconds to Total Server Takeover
The speed of AI-powered exploitation creates a terrifying reality for server management teams: once a bot has your token, it is you. The bot does not need to bypass MFA again because it already holds the “key” to the active session. Within 30 seconds, an automated script can pivot from a compromised Gmail account to your cloud infrastructure, rotate your SSH keys, and delete your offsite backups. This level of automated identity theft allows hackers to lock you out of your own data center permanently before your security team receives a single alert.
Root Cause: The Vulnerability of Portable Session Tokens
The technical root of this crisis lies in the “portability” of session cookies and JWT (JSON Web Tokens). When a server authenticates a user, it issues a token that the browser stores. Unless you implement Token Binding, this token is just a string of data that can be copied and re-played from any IP address. AI bots specialize in extracting these tokens from browser memory or local storage. Because the server only checks if the token is valid—not if it is coming from the same physical hardware the MFA bypass becomes a trivial task for modern malware.
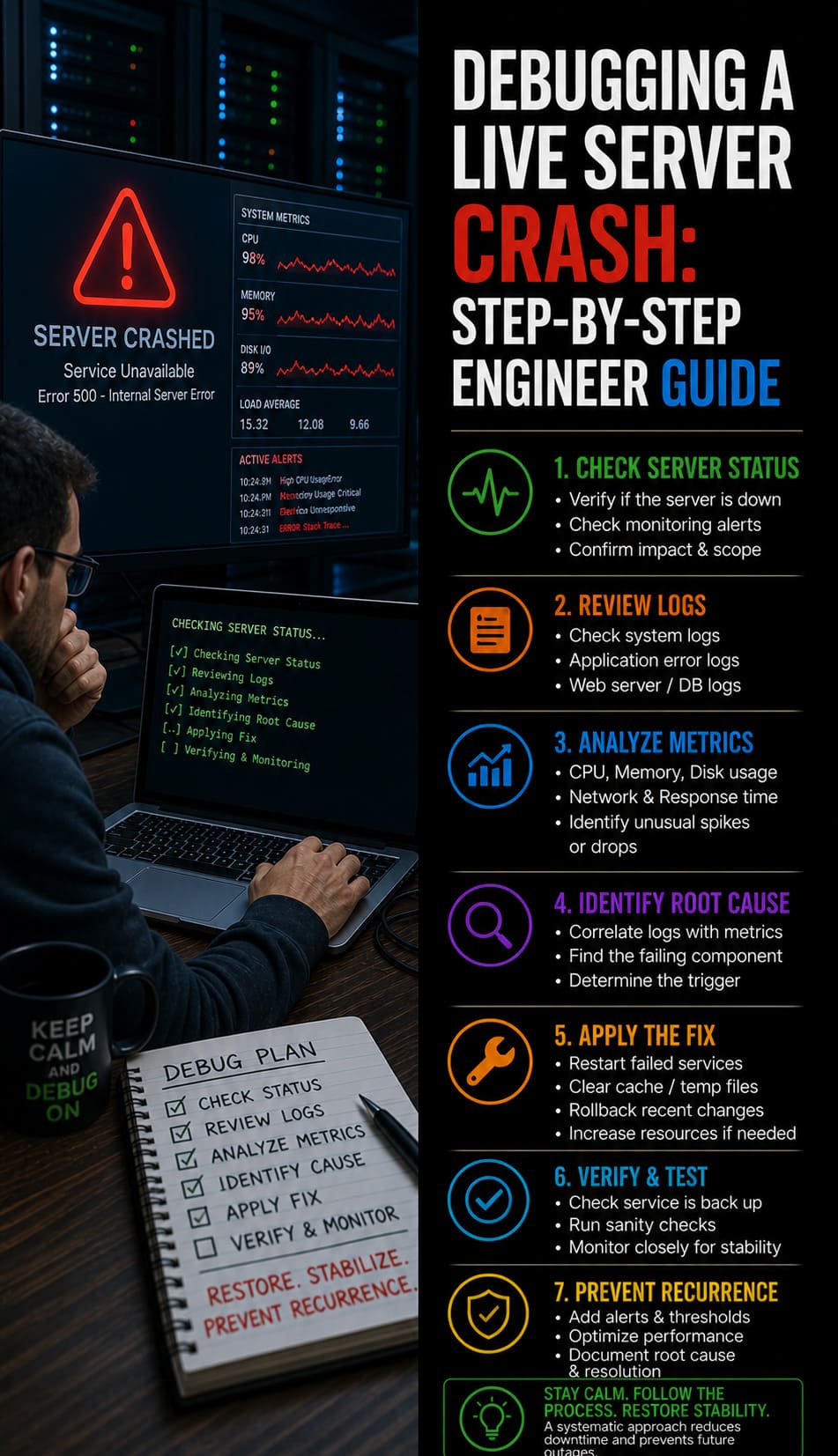
Problem Diagnosis: Auditing for Hidden AI Probes and Reverse Proxies
Engineers must move beyond simple log monitoring to identify AI-driven scanning. Bots often use low-and-slow tactics to map your open ports and firewall states. Use nmap with advanced scripts to detect if your server is being proxied through a malicious “Adversary-in-the-Middle” node. Run nmap -sV --script http-phishing-check <target> to look for signature patterns of common phishing kits. Additionally, audit your auth logs for “impossible travel” patterns, where a single session token appears to migrate between different ASNs or geographic regions in under an hour.
Architecture Insight: Active vs. Passive Security Handshakes
To stop AI bots, you must understand the difference between active and passive security. Standard firewall-cmd rules are passive; they only block what you tell them to. An AI-native WAF, however, performs active interrogation of the client. It checks for headless browser signatures and automated mouse movements that characterize a bot-driven BitB attack. If the handshake fails to prove a human is at the other end of the terminal, the session token must be invalidated immediately. This proactive approach is the only way to defend high-traffic Linux servers in 2026.

Step-by-Step Resolution: Deploying FIDO2 and WebAuthn
Transitioning to phishing-resistant MFA requires a systematic rollout of FIDO2 hardware keys like YubiKeys. Unlike TOTP codes, FIDO2 uses a public-key cryptography system where the private key never leaves the hardware. During login, the server sends a challenge that only the physical key can sign. Crucially, the key checks the Origin URL; it will refuse to sign a challenge from a phishing site even if the site looks 100% legitimate. This hardware-level check is the definitive solution to stop token-stealing attacks from succeeding.
Advanced Fix: Implementing Continuous Access Evaluation (CAE)
For Senior Infrastructure Engineers, the goal is to kill compromised sessions in real-time. By enforcing Continuous Access Evaluation (CAE), your identity provider (like Azure AD or Okta) can revoke a session token the moment a risk is detected. For example, if a server detects an unauthorized visudo change or a sudden MySQL connection error indicating a data dump, it can signal the IDP to terminate all active sessions for that user. This tight integration between server monitoring and identity management prevents hackers from maintaining persistence after a successful MFA bypass.
Hardening Best Practices: Moving to SFTP and SSH Key Pairs
While web-based portals are a major target, FTP remains a critical vulnerability. Legacy FTP sends credentials in plain text, making it a playground for AI bots to sniff traffic. Organizations must enforce SFTP (SSH File Transfer Protocol) and disable password authentication entirely in favor of SSH Key Pairs. By generating a 4096-bit RSA key and storing the private key on a FIDO2 device, you ensure that even if a hacker steals an admin’s laptop, they cannot access the production servers without the physical security token.
Real-World Use Case: The CSF Firewall vs. Automated Botnets
Consider a scenario where a cPanel server is under a distributed token-stealing campaign. The attackers are using a botnet to attempt passive port connections to bypass the CSF (ConfigServer Security & Firewall). While the firewall might block repetitive IP addresses, it cannot stop a bot that has a valid session token. The only way to stop this is to configure the firewall to work with device-based certificates. By ensuring that only devices with a specific MAC address and verified certificate can hit the management ports, you neutralize the bot’s stolen token.
STOP AI-DRIVEN SERVER EXPLOITS BEFORE THEY TAKE OVER YOUR INFRASTRUCTURE
Could AI bots exploit your servers and bypass traditional security controls within seconds?
Modern AI-driven attacks now steal active session tokens, bypass MFA, and rapidly compromise cloud infrastructure. Our engineers help secure production environments using Zero Trust security, FIDO2 authentication, AI-aware monitoring, and advanced server hardening strategies.
The Engineer’s Toolkit: Commands for Token and Session Audit
To protect your infrastructure, use these essential Linux commands to audit active connections and verify server security:
-
Check for suspicious active sessions:
worwho -ato see all logged-in users and their source IPs. -
Monitor real-time network sockets:
ss -atpto identify persistent connections to unknown external IPs on port 443. -
Audit authentication failures:
grep "Failed password" /var/log/auth.logto see if bots are testing legacy credentials. -
Identify kernel-level anomalies:
dmesg | grep -i "segmentation fault"which can indicate an AI bot attempting a buffer overflow exploit to escalate privileges.
Why Businesses Need Managed Server Security in 2026
As AI-speed exploits become the norm, maintaining a secure environment in-house is increasingly difficult. The benefits of outsourcing technical support include access to 24/7 SOC (Security Operations Center) teams that specialize in automated threat hunting. A managed server support provider doesn’t just wait for an alert; they proactively hunt for leaked session tokens on the dark web and implement kernel-level hardening that generic admins often overlook. This is the difference between surviving a bot attack and facing a catastrophic data breach.
Securing cPanel and Web Hosting Environments
For hosting providers, the cpanel security hardening guide must now include a total ban on non-encrypted legacy protocols. Every administrative account should have MFA enforced via WebAuthn to stop token-stealing. Furthermore, administrators should monitor for how to fix disk space 100% linux server errors, as bots often use compromised accounts to host massive “proxy relay” logs, which can fill up /var partitions and crash the entire server. Proactive server health monitoring is essential to identify these subtle signs of a breach.
Authoritative Conclusion: Identity as the Final Perimeter
The 2026 security landscape proves that network perimeters are porous, and passwords are fragile. As AI bots continue to automate token-stealing attacks, the only reliable defense is to treat Identity as your primary firewall. By adopting FIDO2 hardware keys, enforcing SSH key-based access, and implementing continuous session validation, you can ensure your cloud infrastructure management remains resilient. The era of “set and forget” security is over; only those who cryptographically bind their identities to their hardware will survive the next wave of automated exploits.