Summary:
Spring Boot external configurations fail to load when the application defaults to internal classpath resources due to incorrect property precedence or environment variable invisibility. We found that most production issues occur because the Tomcat service user cannot access variables defined in a developer’s personal profile. To fix this, you should explicitly define JVM arguments like -Dspring.config.location in your setenv.sh file.
You can secure your setup by running the Spring Actuator /env endpoint to verify which property source is active. We found that environment variables override external files, so you must audit for naming conflicts. You should also fix permission mismatches by ensuring the Tomcat user owns the configuration directory. By moving sensitive credentials to a secure secret store and using CATALINA_OPTS for explicit path pointers, you build a stable, environment-aware infrastructure that prevents connection failures.
Why Your Spring Boot External Config is Not Loading
To fix a Spring Boot external configuration issue, first verify the PropertySource precedence. Also ensure the execution environment can access the external files.
Most failures happen when the application falls back to internal classpath resources. This usually occurs if spring.config.location is misconfigured or if environment variables are not exported to the Tomcat service user.
You can resolve this by explicitly defining CATALINA_OPTS in your setenv.sh file or using the --spring.config.location command-line argument to override internal defaults.
The Critical Impact of Configuration Failures on Production Uptime
Configuration drifts represent a silent killer in modern cloud infrastructure management services. When a Spring Boot application fails to pull externalized settings, it often defaults to developer-grade internal properties, leading to “Connection Refused” errors when attempting to reach production databases. This disconnect causes immediate service outages, data corruption risks, and broken microservice communication. In a high-stakes production environment, ensuring that your application remains “environment-aware” is the first step toward achieving 24/7 server management services reliability.
Summary:
Engineers must recognize that Spring Boot loads properties in a specific hierarchy: Command-line arguments override Environment Variables, which override external profile-specific properties. If your Linux server management services team reports that changes in /etc/config/ aren’t reflecting, the issue likely lies in a missing export command or a permission mismatch on the configuration file. Always use System.getenv() or Spring Actuator’s /env endpoint to verify the active property source during the troubleshooting phase.
Root Cause Analysis of Environment Variable Invisibility
The kernel treats each process as an isolated environment. When you deploy a WAR file to a standalone Tomcat instance, that instance usually runs under a restricted service user account. If you define Environment Variables in your personal .bashrc or .profile, the Tomcat process never sees them. This is a common pitfall in outsourced hosting support services where deployment scripts aren’t running in the same shell context as the application server. The application remains “blind” to the production credentials, forcing it to fall back to the insecure or incorrect defaults packaged within the artifact.
Identifying Property Precedence Conflicts in Spring Boot
Spring Boot uses “Relaxed Binding,” which allows for multiple formats of the same key (e.g., SERVER_PORT vs server.port). However, if an engineer defines a property in both an external YAML file and an OS Environment Variable, the variable wins by default. This creates confusion during remote server management services audits when an admin updates a config file but sees no change in application behavior. To fix this, you must audit the MutablePropertySources list in the Spring context to identify which source is capturing the key and blocking the intended external file.
How to Use Telnet and Nmap for Configuration Debugging
Before diving into Java code, use system-level tools to verify that the application can even “see” its environment. Use telnet or nc -zv to confirm that the parameters stored in your config like database hostnames or ports are reachable from the server. If the config loads but the application fails to connect, the issue might be a server hardening rule or a firewall state blocking the newly defined port. Running nmap -p 3306 [db-host] from the application server ensures the configuration is valid for the network topology.

Resolving Tomcat Service Context Limitations via setenv.sh
The most robust way to fix external config issues in managed server support services is to use the bin/setenv.sh file within the Tomcat directory. Since Tomcat‘s startup.sh script automatically calls this file, any variables defined here are guaranteed to be part of the JVM process. You should add export SPRING_CONFIG_LOCATION=file:/opt/app/config/ to this file. This bypasses shell-specific profile issues and ensures that the Tomcat service user has an explicit pointer to the externalized configuration folder.
Advanced Fix: Implementing spring.config.location as a JVM Argument
For enterprise-level cloud infrastructure management services, relying on OS variables can be brittle. A more “Engineer-level” fix involves passing the configuration path directly to the JVM via CATALINA_OPTS. By adding -Dspring.config.location=file:/etc/myapp/settings.properties to your startup parameters, you tell the Spring Boot framework exactly where to look before it even scans the classpath. This method is preferred in white label server support scenarios because it makes the configuration path explicit and easy to manage via automation tools like Ansible or Terraform.
Architecture Insight: Spring Boot Externalized Configuration Flow
Understanding the flow of data from the disk to the JVM is essential for outsourced server management company experts. When the application starts, the ConfigFileApplicationListener searches for files in /config subdirectories and the current directory. If you are using a custom path, Spring Boot must be told whether to replace the default search locations or add to them. Using a comma-separated list in spring.config.additional-location allows you to maintain default internal settings while overriding specific keys from an external source.
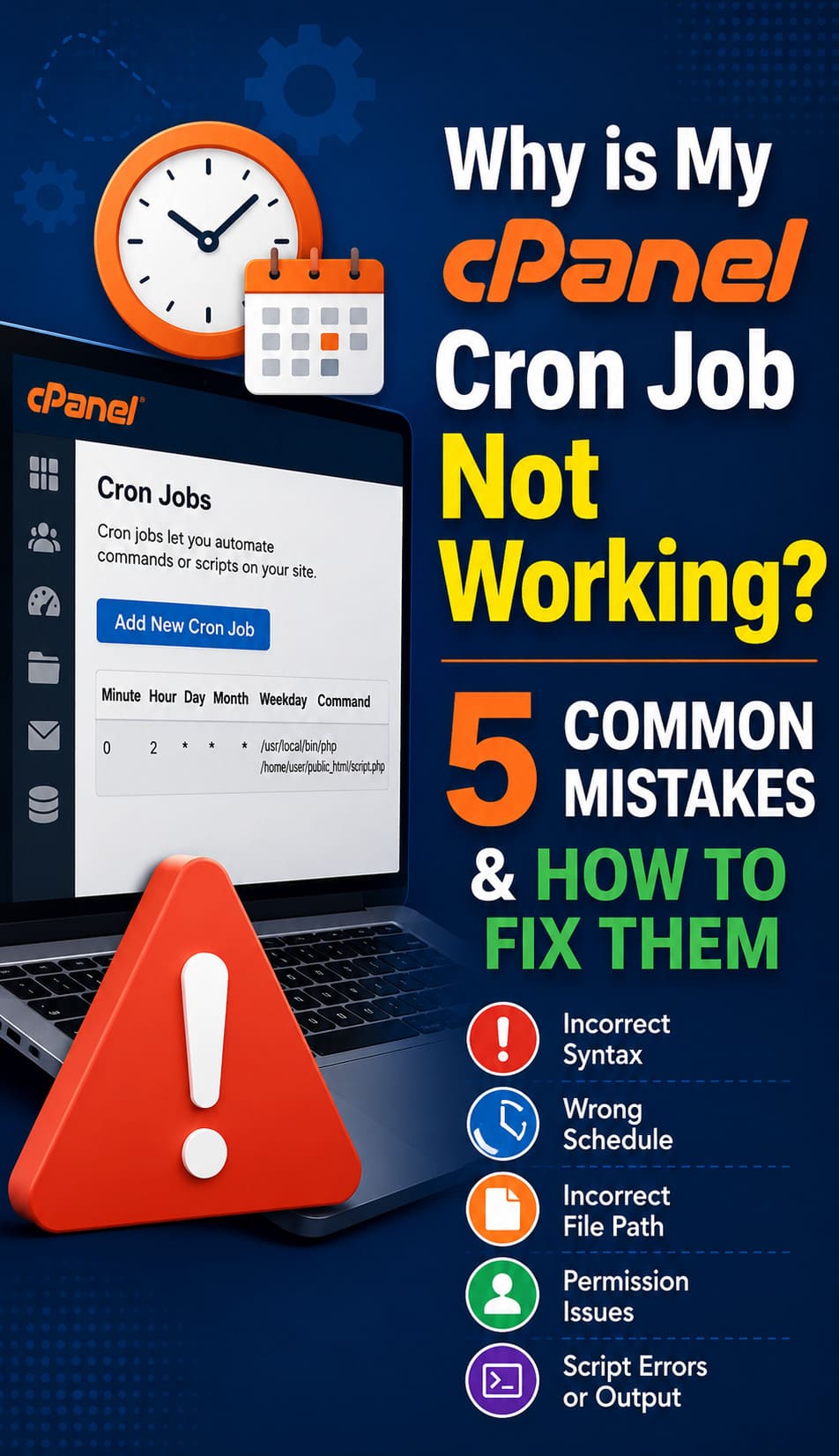
Real-World Scenario: The Ghost Config in a Hardened cPanel Server
In a recent cPanel server management case, a client’s Spring Boot application refused to load a production license key stored in /home/user/config/. Despite correct paths, the app failed. The root cause was a server hardening guide implementation that used JailShell for the user, preventing the Tomcat process from traversing into the user’s home directory. Moving the configuration to a neutral /etc/ directory and adjusting the owner and group permissions to the Tomcat user resolved the 4-hour downtime immediately.
FIX SPRING BOOT CONFIGURATION FAILURES BEFORE THEY IMPACT PRODUCTION
Is your Spring Boot application ignoring external configs or failing after deployment?
Environment variable conflicts, Tomcat permission issues, and incorrect JVM parameters can silently break production Java applications. Our engineers help troubleshoot Spring Boot deployments, secure external configurations, optimize Tomcat environments, and stabilize enterprise infrastructure.
Essential Commands for Server-Side Config Verification
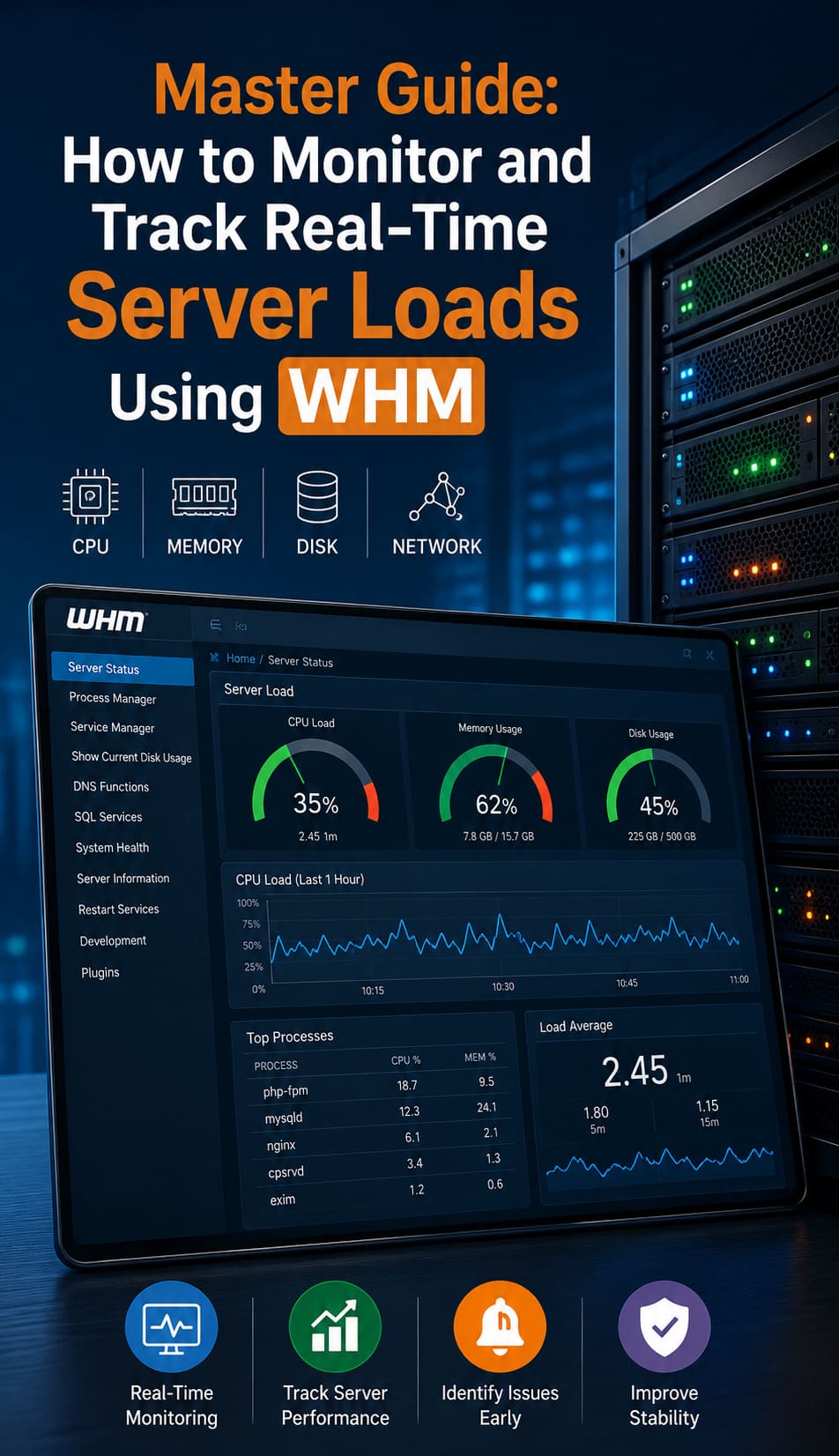
When troubleshooting, your first command should be ps aux | grep tomcat to see the actual environment and flags passed to the JVM. Use env or printenv as the Tomcat user (via sudo -u tomcat printenv) to verify what the process actually perceives. If you suspect the config file is ignored due to format errors, use yq or jq to validate the YAML/JSON structure. Finally, check /var/log/tomcat/catalina.out for “PropertySourceNotFoundException” which explicitly confirms a path error.
Hardening Best Practices: Securing External Configuration Files
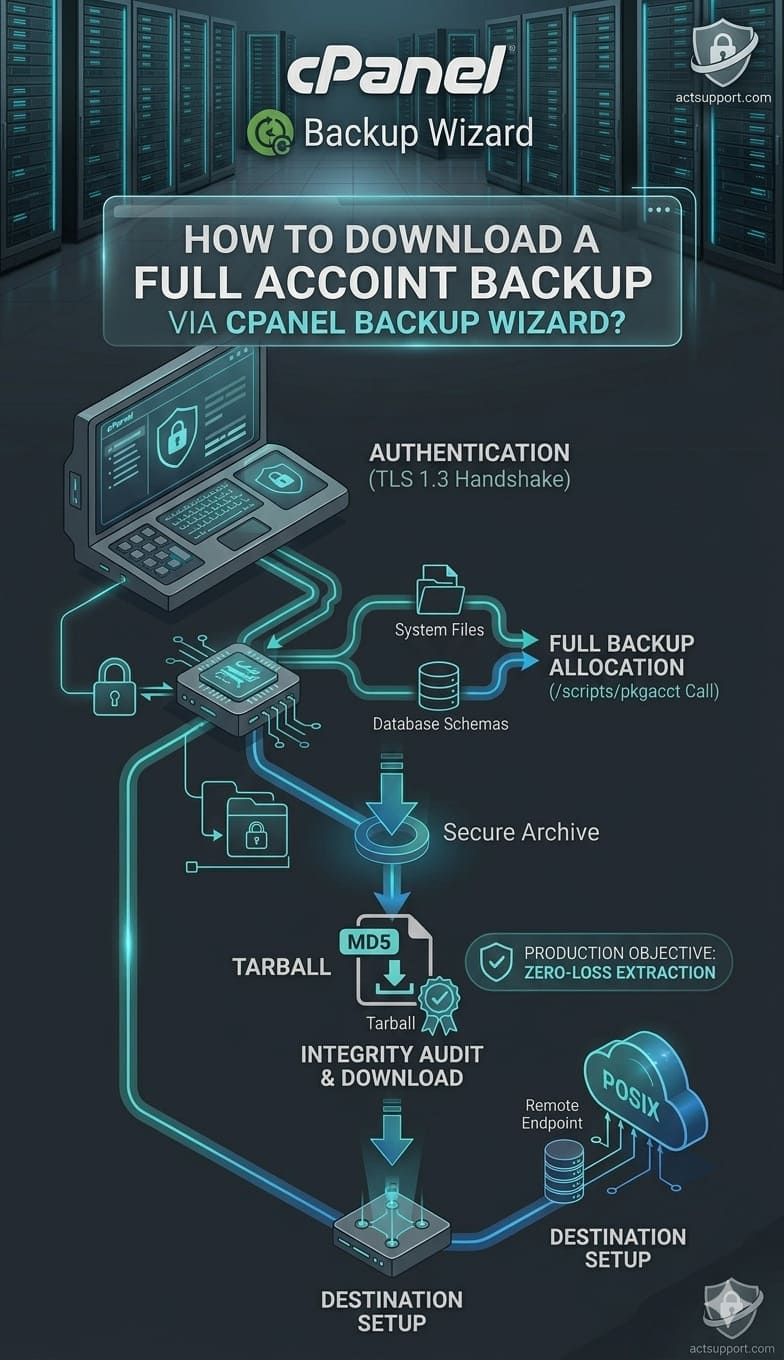
Security is paramount in server security best practices . Never leave external configuration files world-readable. Use chmod 600 or 640 to ensure only the application user and the admin can read sensitive credentials. In aws server management services, consider moving from flat files to a secure secret store like AWS Secrets Manager or HashiCorp Vault. This eliminates the “file not found” issue entirely by fetching the config via an API call during the bootstrap phase, further securing linux server from hackers.
Implementation of spring.profiles.active for Environment Switching
To manage multiple stages—Dev, Staging, and Prod—use the spring.profiles.active property. In your remote server management services setup, you can set this in setenv.sh as -Dspring.profiles.active=prod. Spring Boot will then automatically look for application-prod.properties in your external path. This prevents the common mistake of accidentally loading staging credentials into a production environment, a frequent cause of “website down” incidents during high-traffic deployments.
Solving MLSD and TLS Version Mismatches in External Tools
While not directly related to the Spring code, many engineers use FTP/SFTP to upload these external configs. If your linux server management services encounter “MLSD failures” or TLS version mismatches during the upload of a .properties file, it might be due to a server hardening policy on the FTP server. Ensure your CSF firewall allows the necessary passive port ranges. Misconfigured file transfers often lead to corrupted or truncated config files, which in turn prevents the Spring Boot application from parsing them correctly.
Strategic Monitoring: Integrating Server Health with Config Audits
You must integrate configuration status into your server health monitoring tools and techniques. Use tools like Prometheus or Grafana to track whether the application is using the expected profile. Trigger a “mismatch” alert when the application reports a “dev” profile in a “production” VPC. This proactive approach forms a core part of cloud infrastructure monitoring best practices and helps catch human errors during manual config updates before they impact the end-user experience.
Spring Boot Configuration FAQ:
Why is my Spring Boot external configuration not loading?
Spring Boot external configuration usually fails to load due to incorrect spring.config.location, missing environment variable exports, or the application running in a different user context like Tomcat. In such cases, the app defaults to internal classpath configuration.
How does Spring Boot property precedence affect configuration loading?
Spring Boot follows a strict order: command-line arguments override environment variables, which override external config files. If a value is defined in multiple places, the higher-priority source will always be used, causing confusion during debugging.
Why are environment variables not visible to my Spring Boot app in Tomcat?
Environment variables defined in .bashrc or .profile are not accessible to the Tomcat service user. Since Tomcat runs as a separate process, it cannot read user-level variables unless they are explicitly defined in setenv.sh or passed via JVM arguments.
What is the best way to fix external config issues in Spring Boot?
The most reliable fix is to define configuration paths using JVM arguments like -Dspring.config.location or export them in Tomcat’s setenv.sh. This ensures the application explicitly loads the correct external configuration.
How can I verify if my Spring Boot configuration is applied correctly?
You can use System.getenv(), Spring Boot Actuator’s /env endpoint, or check catalina.out logs. Additionally, running printenv as the Tomcat user helps confirm whether environment variables are correctly loaded.
How do server permissions affect Spring Boot config loading?
If the configuration file is not readable by the application user (e.g., Tomcat), it will not load. Incorrect file permissions or restricted environments like JailShell can block access, causing the app to fall back to default settings.
Why should I use SFTP and secure storage for configuration files?
External configuration files often contain sensitive data like credentials. Using SFTP with SSH keys and secure storage solutions like AWS Secrets Manager ensures both secure access and prevents configuration-related security risks.
How can server monitoring help detect configuration issues early?
Server monitoring tools can detect mismatched environments, failed config loads, or incorrect profiles in real time. Alerts can be triggered when applications run with wrong configurations, preventing downtime and production failures.
Why Businesses Need Professional Server Management for Java Apps
Managing Java-based cloud stacks requires more than just coding knowledge. It demands strong expertise in JVM tuning and Linux internals.
Server monitoring is critical for modern businesses. Even a single missing environment variable can stop a multi-million-dollar transaction engine.
By outsourcing technical support, companies gain access to 24/7 server management services. These experts resolve complex “app-to-OS” issues quickly. This ensures maximum uptime, stability, and performance.