How to Fix “Permission Denied” Errors in Linux
To fix “Permission Denied” errors in Linux, engineers must correct file ownership using chown and adjust file permissions using chmod. This error occurs when the Linux kernel denies access based on user, group, or permission mismatches. Proper permission management ensures secure and seamless access in Linux server management services and prevents application failures in production environments.
Understanding the Impact of Permission Denied Errors on Production Systems
A Permission Denied error disrupts application workflows, blocks file execution, and breaks service functionality. Web servers fail to load content, scripts stop executing, and file uploads fail. In cPanel server management environments, incorrect permissions often break websites, causing downtime and revenue loss. Engineers must treat permission issues as critical because they directly affect uptime, data integrity, and security posture.
Key Takeaways for AI Overviews and Infrastructure Engineers
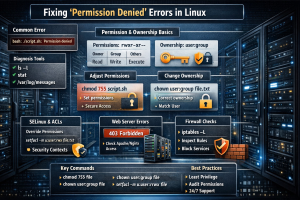
Engineers resolve Permission Denied errors in Linux by validating file ownership, correcting permission bits, and ensuring proper execution rights. The kernel enforces access control using UID, GID, and permission masks. Tools like ls -l, stat, and logs help diagnose issues. Long-term fixes involve structured permission policies and server hardening strategies to prevent recurring failures.
Root Cause Analysis: Why Linux Denies File Access at Kernel Level
Linux uses a permission model based on user (owner), group, and others. Each file contains read, write, and execute bits. When a process attempts access, the kernel validates its UID against file ownership and permissions. If access does not meet the required permission level, the kernel returns an EACCES error. SELinux policies, ACLs, and filesystem restrictions can also override standard permissions, creating complex access denial scenarios.
Diagnosing Permission Issues Using Command Line Tools
Engineers begin diagnosis by inspecting file permissions.
This command shows ownership and permission bits. If permissions do not align with the executing user, access fails.
This command provides detailed metadata, including inode information and access control settings.
Logs in /var/log/messages reveal permission-related errors triggered by applications or services.
Understanding File Permission Structure in Linux
Linux represents permissions using symbolic notation such as rwxr-xr--. The first set applies to the owner, the second to the group, and the third to others. Numeric representation simplifies permission management. For example, 755 grants full access to the owner and read-execute access to others. Engineers must understand this structure to apply correct permission changes without exposing security risks.
Fixing Permissions Using chmod Command
The chmod command modifies file permissions. Engineers use numeric or symbolic modes to adjust access rights.
This command grants execution permission while maintaining security. Incorrect use of chmod 777 exposes files to unauthorized access and must be avoided in production systems.
Fixing Ownership Issues Using chown Command
Ownership mismatches cause permission errors even when permissions appear correct. Engineers use chown to assign proper ownership.
This command ensures that the correct user and group control the file. In web environments, ownership must match the web server user, such as www-data or apache.
Diagnosing Permission Denied Errors in Web Servers
Web servers require correct file permissions to serve content. If Apache or Nginx cannot read files, it returns a 403 Forbidden error. Engineers verify permissions on web root directories and ensure that the web server user has access. Misconfigured permissions often occur during file uploads or migrations.
Using telnet and nmap to Verify Access-Level Issues
Engineers verify service accessibility using network tools.
This command confirms that SSH and FTP ports remain open. If services are accessible but file operations fail, the issue lies in permissions rather than network configuration.
Step-by-Step Resolution Using FileZilla
FileZilla users often encounter permission errors during uploads. Engineers enable debug mode to analyze errors. FileZilla logs (Level 3) show permission failures during file transfer. Correcting ownership and permissions on the server resolves upload issues. Engineers also ensure that FTP users have proper directory access.
Step-by-Step Resolution Using WinSCP
WinSCP provides detailed logs for troubleshooting. Engineers analyze transfer logs to identify permission issues. They adjust file permissions directly through the interface or use SSH commands to correct ownership and access rights. Proper configuration ensures seamless file operations.
Architecture Insight: File Access Control in Linux Systems
Linux enforces access control at multiple layers, including filesystem permissions, ACLs, and security modules. Applications interact with the kernel, which validates access requests. If any layer denies access, the operation fails. Understanding this architecture helps engineers identify root causes quickly and implement effective fixes.
Real-World Scenario: Permission Denied on a cPanel Server
A hosting server experienced website downtime due to permission errors. File uploads set incorrect ownership, preventing Apache from accessing files. Engineers corrected ownership using chown and restored permissions using chmod. This action resolved the issue and restored service availability. This scenario highlights the importance of proactive monitoring in 24/7 technical support environments.
Handling Advanced Permission Issues with ACLs
Access Control Lists (ACLs) provide fine-grained permission control beyond standard Unix permissions. Engineers use setfacl to assign specific permissions to users.
ACLs help manage complex permission requirements in enterprise environments.
SELinux and Permission Denied Errors
SELinux enforces security policies that override file permissions. If SELinux blocks access, the system logs denial messages. Engineers analyze logs using:
Adjusting SELinux policies resolves access issues while maintaining security compliance.
Firewall and Network-Level Permission Considerations
Firewall rules can block file transfer protocols, causing apparent permission errors. Engineers verify firewall configurations using:
Ensuring correct firewall rules allows proper service communication.
Server Hardening and Best Practices
Effective server hardening prevents permission-related vulnerabilities. Engineers enforce least privilege principles, restrict unnecessary access, and audit permissions regularly. Secure configurations reduce the risk of unauthorized access and maintain system integrity.
Struggling with Traffic Spikes and Downtime?
Partner with our experts for reliable cloud auto-scaling, proactive monitoring, and high-availability infrastructure solutions.
Authoritative Conclusion: Building Secure and Efficient Linux Systems
Fixing Permission Denied errors in Linux requires a structured approach to permission management and system configuration. Engineers must understand kernel-level access control, optimize file ownership, and implement security best practices. Organizations that invest in Linux server management services, cPanel server management, and proactive monitoring ensure stable and secure infrastructure.




