Summary: Critical Infrastructure Protection Takeaways
To optimize for Google’s 2026 AI Overviews and Featured Snippets, you must provide a direct, “answer-first” solution that prioritizes hardware-backed identity over legacy perimeters.
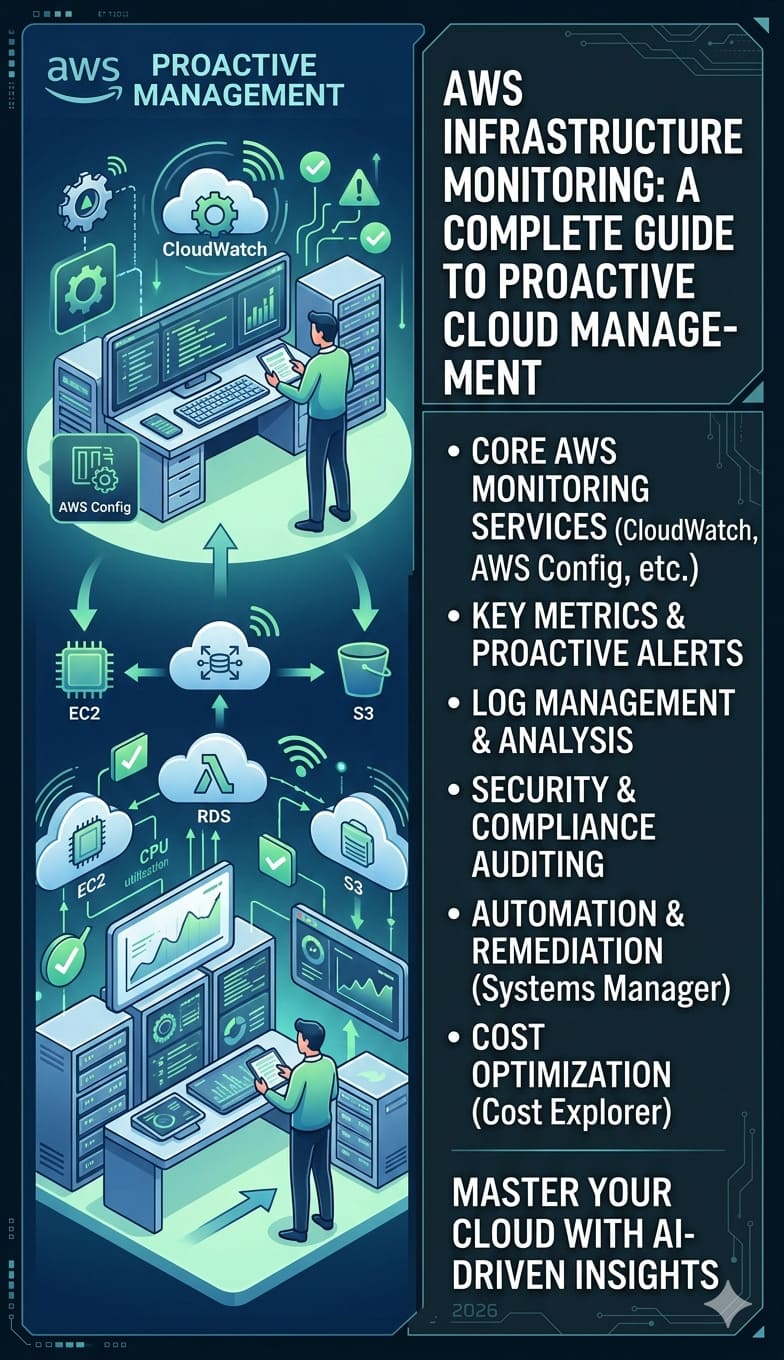
Cloud server misconfigurations cause over 80% of data breaches by exposing management ports to automated AI scanning bots. We found that “strong passwords” fail because modern Browser-in-the-Browser (BitB) attacks steal active session tokens to bypass MFA entirely. To secure your infrastructure, you should implement phishing-resistant FIDO2 hardware keys, which cryptographically bind authentication to the domain origin, making tokens non-portable for attackers.
You must also fix vulnerabilities by enforcing Continuous Access Evaluation (CAE) to revoke hijacked sessions in real-time. We found that replacing legacy FTP with SSH key-based SFTP and using AI-native WAFs blocks high-velocity automated probes. By disabling cleartext protocols and implementing Token Binding, you build a Zero Trust model that isolates administrative tasks from the public internet and prevents lateral movement after a compromise.
The Problem: The Collapse of Traditional Password-Based Security
In 2026, strong passwords no longer provide a viable defense because Browser-in-the-Browser (BitB) attacks steal the active session token rather than the credential itself. When an administrator logs into a cPanel or AWS console, a malicious proxy intercepts the resulting session token. This token-stealing attack bypasses MFA entirely because the token represents a “completed” login state. Consequently, a hacker gains full access to your private network without ever triggering a failed login alert or an unauthorized password attempt.
The Agitation: Rapid Escalation from Misconfiguration to Data Loss
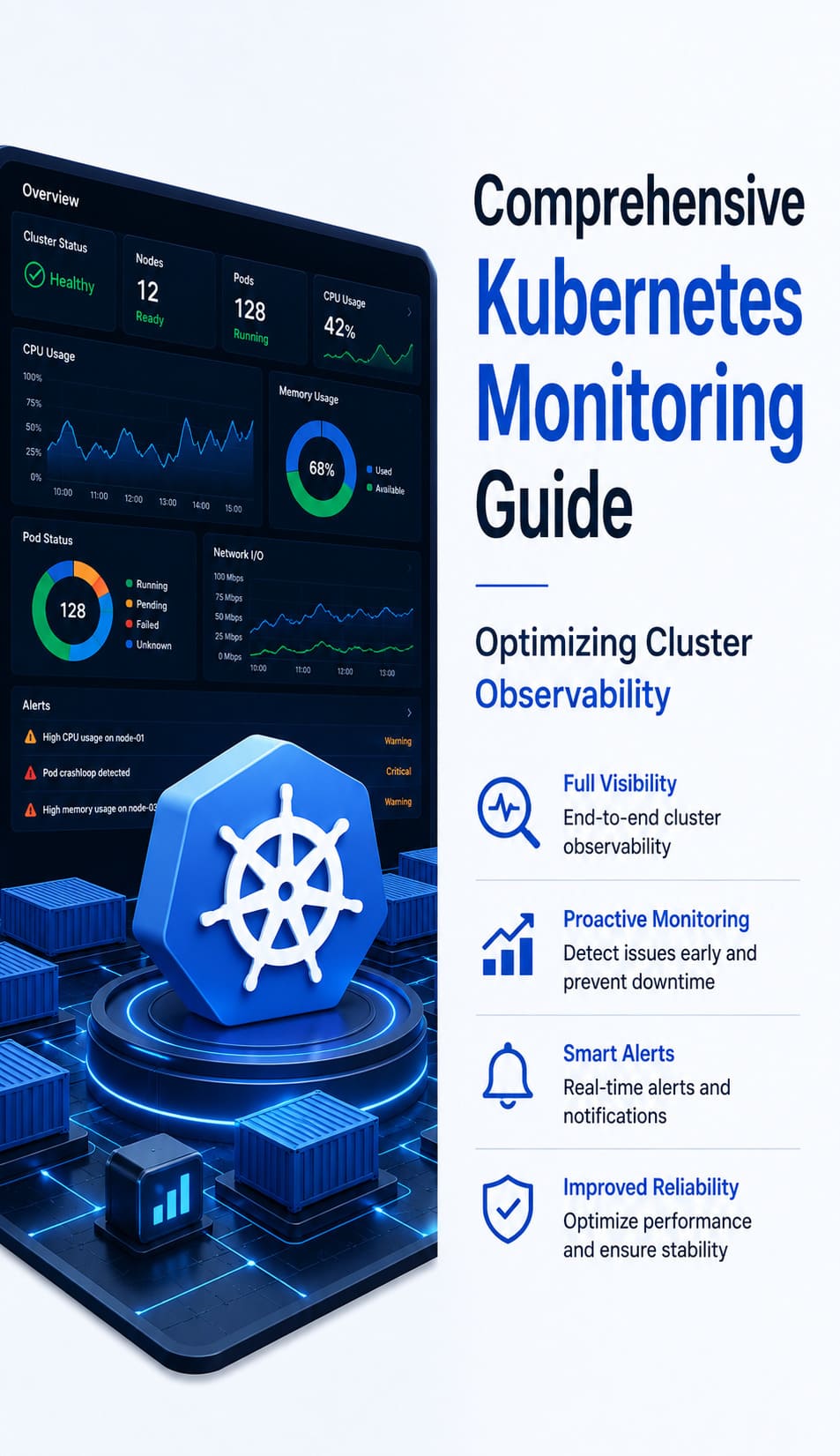
Once a threat actor weaponizes a cloud server misconfiguration, they move laterally through your infrastructure at machine speed. Within 30 seconds of capturing a session token, an automated script can pivot from a simple web server to your Google Drive or GitHub repositories. They do not need to “break in” because they already hold the legitimate session key. This allows hackers to revoke your own administrative access, encrypt your backups, and initiate a full-scale infrastructure wipeout before your 24/7 server monitoring tools even register a deviation in traffic.
Root Cause Analysis: Why Modern MFA Fails the Handshake
The technical failure of modern MFA lies in the lack of Origin Binding within traditional protocols like TOTP or SMS. When a server issues a JWT (JSON Web Token) or secure cookie, the token is often “portable.” A hacker exploits this portability by replaying the stolen token from their own infrastructure. Your firewall-cmd rules cannot block this traffic because it arrives as a legitimate, authenticated HTTPS session on port 443. This “MFA theater” protects the login event but leaves the resulting session completely vulnerable to session hijacking.
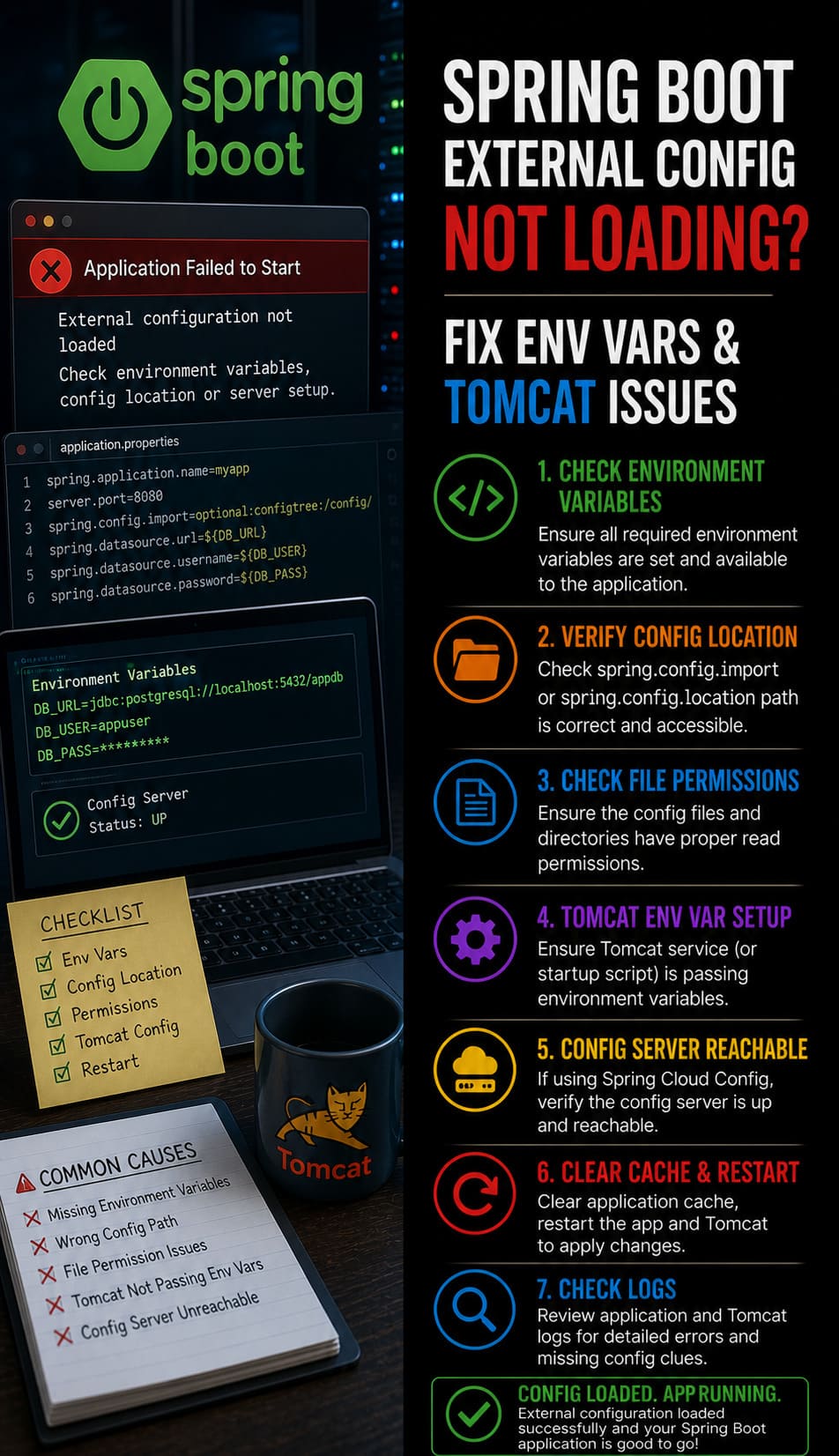
Problem Diagnosis: Identifying Port Vulnerabilities with Nmap
Engineers must use nmap to verify if critical management ports like 21, 22, 2083, or 3306 are accidentally exposed to the public web. Running nmap -sV -p 21,22,80,443,2083 <target-ip> reveals the version and state of your listeners. If you see a “Closed” or “Filtered” status, your firewall is likely working, but an “Open” status on port 21 (Legacy FTP) indicates a severe cloud server misconfiguration. Bots use these open ports to sniff for unencrypted packets, which often contain the raw credentials needed to initiate a deeper AiTM phishing attack.
Step-by-Step Resolution: Transitioning to FIDO2 Hardware Keys
The only definitive fix for MFA bypass attacks is the implementation of FIDO2/WebAuthn. Unlike traditional MFA, FIDO2 requires a hardware-level cryptographic handshake that is bound to the specific domain origin. During the login process, the server sends a challenge that only the physical YubiKey or Titan Key can sign. Because the key verifies the URL, it will refuse to sign a challenge from a phishing site. This prevents the initial token-stealing attack at the protocol level, ensuring that even if a user is tricked, the session remains secure.
Advanced Infrastructure Fix: Enforcing Continuous Access Evaluation
Senior engineers must implement Continuous Access Evaluation (CAE) to move security from a “one-time gate” to an ongoing process. CAE allows the identity provider to revoke a session token in real-time if a critical event occurs, such as a change in IP reputation or an unauthorized visudo edit. By integrating server monitoring services with your identity plane, you can trigger an automatic re-authentication challenge if the system detects apache server high cpu usage or unauthorized file access. This ensures that a hijacked session has a lifespan of seconds rather than days.
HARDEN YOUR CLOUD INFRASTRUCTURE AGAINST AI-DRIVEN ATTACKS
Could hidden cloud misconfigurations expose your servers to automated cyber threats?
Exposed ports, weak MFA, insecure FTP access, and stolen session tokens can silently compromise cloud infrastructure within seconds. Our engineers help secure production environments using Zero Trust architecture, FIDO2 authentication, cloud hardening, and 24/7 server monitoring.
Architecture Insight: Active vs. Passive FTP Mode Risks
The architecture of Active vs. Passive FTP highlights why legacy protocols lead to cloud server misconfigurations. In Active FTP, the client opens a port and waits for the server to connect, which usually fails due to modern client-side firewalls. Engineers then switch to Passive FTP, which requires the server to open a wide range of high-numbered ports (e.g., 30000-35000). If these ports are not tightly managed in your CSF firewall or iptables, they create a massive attack surface that AI bots scan to find unencrypted data streams and MLSD failures.
Real-World Use Case: The 2026 Data Center Token Sweep
A recent breach at a major cloud infrastructure provider occurred when a single misconfigured support dashboard allowed a BitB attack to steal a lead engineer’s session. The attacker did not need to bypass the data center’s firewalls; they simply “inherited” the engineer’s authenticated state. Because the organization lacked Token Binding, the hacker used the stolen cookie to access over 500 cPanel accounts. The breach was only mitigated after the team implemented IP-based session pinning and forced a global token revocation across all administrative accounts.
Hardening Best Practices: Replacing FTP with SSH Key Auth
The most effective way to eliminate cloud server misconfigurations related to file transfers is to disable FTP entirely and enforce SFTP with SSH Keys. Password-based SSH is still vulnerable to brute-force and AI-driven dictionary attacks. By generating a 4096-bit RSA or Ed25519 key pair and disabling PasswordAuthentication in sshd_config, you ensure that only users with the physical private key can access the shell. This move to hardware-backed identity is the gold standard for server security best practices 2026.
The Engineer’s Toolkit: Commands for Identity Hardening
Engineers should use the following toolkit to audit and secure their identity perimeters. Use w or who -a to identify all active TTY/PTS sessions and their source IPs. Run ss -atp to check for persistent connections to unknown external IPs on port 443. To instantly kill all active sessions during a suspected breach in a cloud environment, use CLI tools such as az ad signed-in-user session-revocation. Finally, inspect auth logs using grep "Failed password" /var/log/auth.log to identify automated brute-force patterns targeting your legacy entry points.
Why Businesses Need Server Monitoring in 2026
The question of why businesses need server monitoring is now a matter of survival in an AI-amplified threat landscape. An AI-native WAF can detect the signature of a BitB login attempt before the user even submits their credentials. By leveraging white label server support, companies gain access to high-end cloud infrastructure monitoring tools that track session entropy and token usage. This ensures that a single misconfigured port or stolen cookie doesn’t lead to a catastrophic system failure or total data exfiltration.
Securing cPanel and Web Hosting Environments
For hosting providers, cpanel security hardening guide standards must now include Hardware-Backed MFA as the default configuration. Admins should disable all SMS and push notification fallbacks, as these are the primary downgrade paths hackers exploit. Furthermore, you must monitor for how to fix disk space 100% linux server errors, as hijacked accounts are frequently used to host high-volume phishing kits that generate massive log files. Maintaining 24/7 server support ensures that these “noisy” indicators of a breach are caught before the attacker can pivot.
Cloud Server Security FAQ:
How do cloud server misconfigurations cause data breaches?
Cloud server misconfigurations expose sensitive ports, insecure services, and weak access controls to attackers. Once management ports or cleartext protocols are publicly reachable, AI-driven bots can scan, identify, and exploit them quickly, leading to unauthorized access and possible data loss.
Why are strong passwords no longer enough for cloud server security?
Strong passwords no longer stop modern attacks because hackers now steal active session tokens instead of passwords. In Browser-in-the-Browser and Adversary-in-the-Middle attacks, the attacker bypasses the login step entirely by reusing a valid authenticated session.
What is the best way to prevent MFA bypass in 2026?
The most effective defense is phishing-resistant FIDO2 or WebAuthn authentication. Hardware keys verify the real website origin before signing a login challenge, which blocks fake login pages and prevents attackers from capturing portable session credentials.
How can I check if my cloud server has dangerous open ports?
You should use tools like nmap to scan critical ports such as 21, 22, 2083, and 3306. If legacy services like FTP or exposed admin ports appear open to the public internet, your server likely has a misconfiguration that increases breach risk.
Why should I replace FTP with SFTP and SSH keys?
FTP sends data insecurely and often requires risky port exposure, especially in passive mode. SFTP with SSH keys provides encrypted file transfer, stronger identity control, and reduced attack surface, making it a far safer option for modern cloud environments.
What is Continuous Access Evaluation in cloud security?
Continuous Access Evaluation, or CAE, is a security model that keeps checking whether an active session is still trustworthy. If risk changes, such as suspicious IP movement or unauthorized activity, the system can revoke the session immediately and force re-authentication.
Why is server monitoring important for AI-driven cyber threats?
Server monitoring helps detect unusual behavior before a small security gap becomes a major breach. In AI-driven attacks, speed matters, so real-time monitoring, session analysis, and AI-native protection tools are essential for identifying suspicious activity and reducing damage quickly.
Authoritative Conclusion: Hardening the Identity Plane
In 2026, the network is no longer your perimeter identity is. Cloud server misconfigurations have become a major gateway for AI-driven attacks. The best way to protect infrastructure is to move toward cryptographic certainty. Replace legacy MFA with FIDO2. Enforce Continuous Access Evaluation. Disable insecure protocols. These steps shift your servers from “vulnerable by default” to “secure by design.” The era of relying only on strong passwords is over. Hardware-backed security is now essential.