Fork Bomb on Linux/Unix:
Q. Explain following bash code or bash fork() bomb?
: () { : | :& };:
A. This is a bash function. It gets called recursively (recursive function). This is most horrible code for any Unix / Linux box. It is often used by sys admin to test user processes limitations (Linux process limits can be configured via /etc/security/limits.conf and PAM).
Once a successful fork bomb has been activated in a system it may not be possible to resume normal operation without rebooting, as the only solution to a fork bomb is to destroy all instances of it.
Understanding : (){ : | :& };: fork() bomb code
******************************************************************************
WARNING! These examples may crash your computer if executed and please dont try this on any live servers
******************************************************************************
: (){ : | :& };:
Understanding the above:
: () # define ‘:’ — whenever we say ‘:’, do this:
{ # beginning of what to do when we say ‘:’
: # load another copy of the ‘:’ function into memory…
| # …and pipe it’s output to…
: # …another copy of ‘:’ function, which has to be loaded into memory
# (therefore, ‘:|:’ simply gets two copies of ‘:’ loaded whenever ‘:’ is called)
& # disown the functions — if the first ‘:’ is killed, all of the functions that it has started should NOT be auto-killed
} # end of what to do when we say ‘:’
; # Having defined ‘:’, we should now…
: # …call ‘:’, initiating a chain-reaction: each ‘:’ will start two more.
Given that ‘:’ is an arbitrary name for the function, an easier to understand version would be:
Example forkbomb code:
forkbomb(){ forkbomb|forkbomb & } ; forkbomb
Here is more human readable code:
bomb() {
bomb | bomb &
}; bomb
How to prevent from fork bomb attack?
To protect a system against such attacks, there is a file for limiting the number of processes for each user. It is /etc/security/limits.conf. Add the following two lines to it:
@users soft nproc 100
@users hard nproc 150
The lines prevent anyone in the users group from having more than 150 processes, and issue a warning at 100 processes.
Your system may not have a users group, so you may need to edit the lines to suit your needs.
List command line history with timestamp
If the command line history could provides the date time of the commands being executed, that may really narrow down the scope of the user actions that cause the server malfunction. By default, history do not append with timestamp, but it is easy to configure it to display timestamp, you just need to set one environment variable HISTTIMEFORMAT.
export HISTTIMEFORMAT=”%F %T “
Add the above line into ~/.bash_profile(for users) as well as/root/.bash_profile(for root).
Then run ‘history’ command
Output:
985 2009-08-02 08:01:15 ll
986 2009-08-02 08:01:21 rm -rvf lampp/
987 2009-08-02 08:02:01 tar -xvzf xampp-linux-1.7.1.tar.gz -C /opt
988 2009-08-02 08:02:36 /opt/lampp/lampp start
989 2009-08-02 08:03:24 nmap localhost
How to change Mac address(virtually) on Linux box?
Log into the system as root(Superuser)
# ssh root@IP(host)
shutdown the interface
# ifdown eth0
Then execute the following command
# ifconfig eth0 hw ether 00:05:6f:62:ea:b3
start the interface
# ifup eth0
Now your system will use the above given mac address as your h/w address of your NIC
That’s it folks ![]()
-
Previous Post
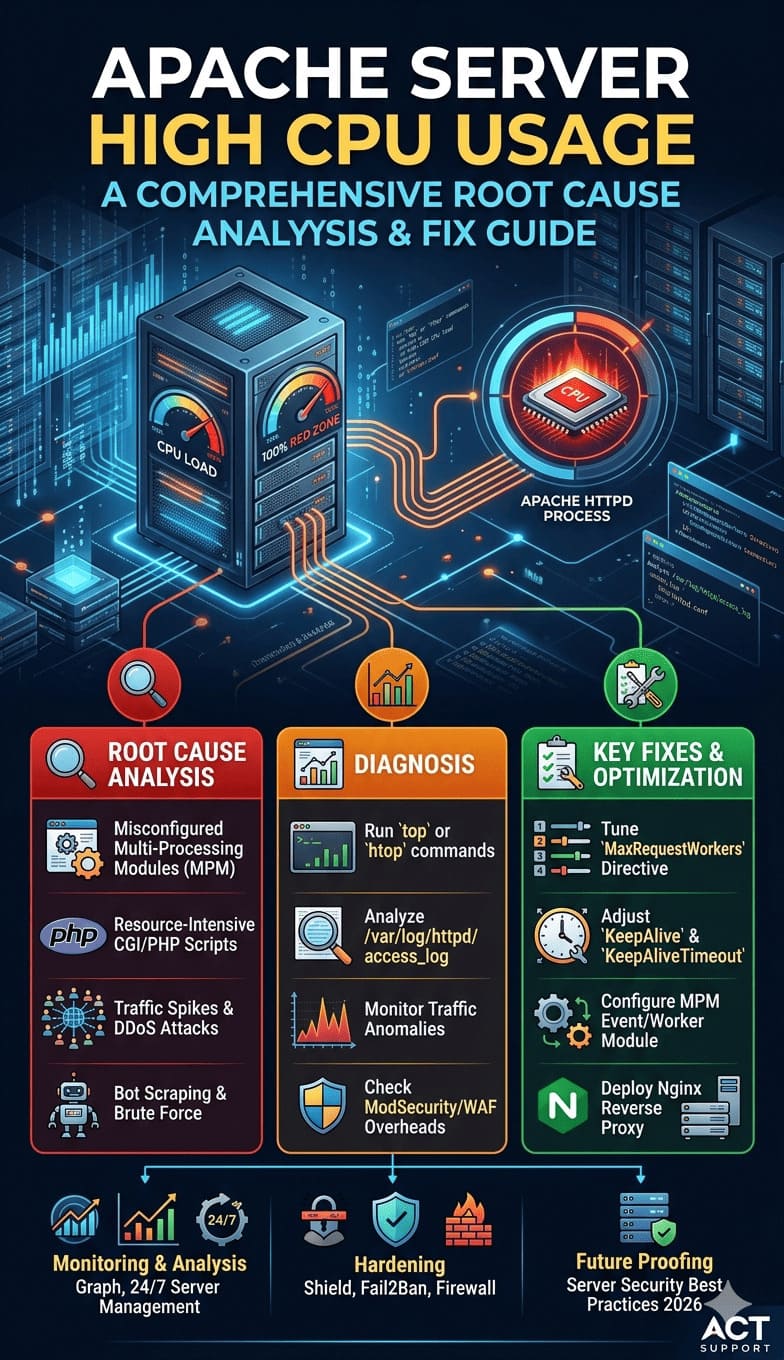
How to identify CPU resource problem?
-
Next Post
Linux – Ethernet bonding








KAYSWELL
March 9, 2026Thank you for writing this post!
Good Art Design
March 11, 2026I’m so in love with this. You did a great job!!
xsjyBldb
April 3, 2026555
xsjyBldb
April 3, 2026555