Managing network traffic is a critical aspect of any organization and a tricky job for system administrators. Knowing what traffic to allow and what to block can be a matter of being safe or vulnerable to cyber-attacks.
A firewall is a tool built to aid system administrator’s in regulating incoming and outgoing traffic. System administrators working with Linux servers must be familiar with Iptables. Iptables is a flexible firewall tool built for Linux operating systems. Iptables can seem intimidating, but knowing a few tricks and commands could make working with Iptables much easier.
1. What is Iptables and how to view them
Iptables is a command-line based firewall utility that works on the principal of ‘rules’ to allow or block incoming and/or outgoing traffic. When traffic hits the firewall, Iptables looks for rules matching the connection type, IP or Port and resorts to action set for the rule.
The first command is a simple one to view the Iptables which also works to install/update it.
sudo apt-get install Iptables
2. Check Input, Output and Forward Chains
Iptables utilizes 3 different chains:
- Input: This chain is used to control the nature of incoming traffic. For example, if your server acts as a mail server and receives POP/IMAP connections, it will cross check the IP and port with an input rule.
- Output: In this the chain is used control the behaviour if outgoing connections. For example, if you search for www.google.com, once the outgoing connection hits the Linux server, the Iptables firewall checks if the domain google.com, the port or connection has any rule set to it.
- Forward: This chain is used from traffic that hits your Linux server but is intended to be routed to another destination. The Linux server acts as a ‘forwarding’ server.
To check the input, output and forwarded data through the Linux box running Iptables Firewall, type:
Picture Credit
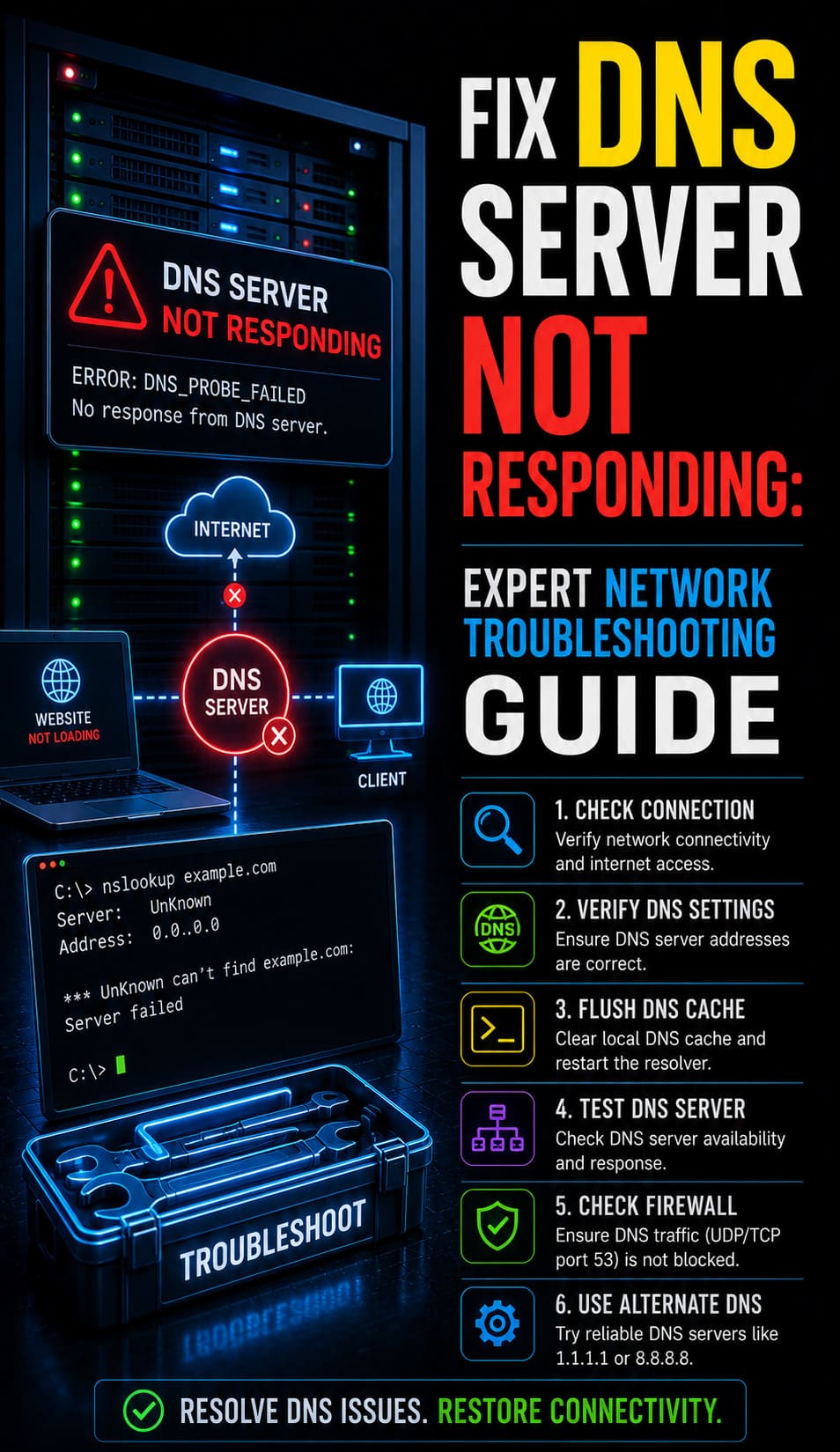
The above image shows, in Gigabytes, how much traffic came in, went out and was forwarded.
3. Default settings for Input, Output and Forward chains
Iptables works by way of rules. When a connection hits the Linux server, it checks if there is an existing rule for the connection, if not, it applies the default rule. It is good to know what the default rule is, before going about setting new rules. To find the default rules for Input, Output and Forward chains, type:
# iptables -L -n –v
For a Firewall with no rules configured, an output similar to the below one will be displayed:
Picture Credit
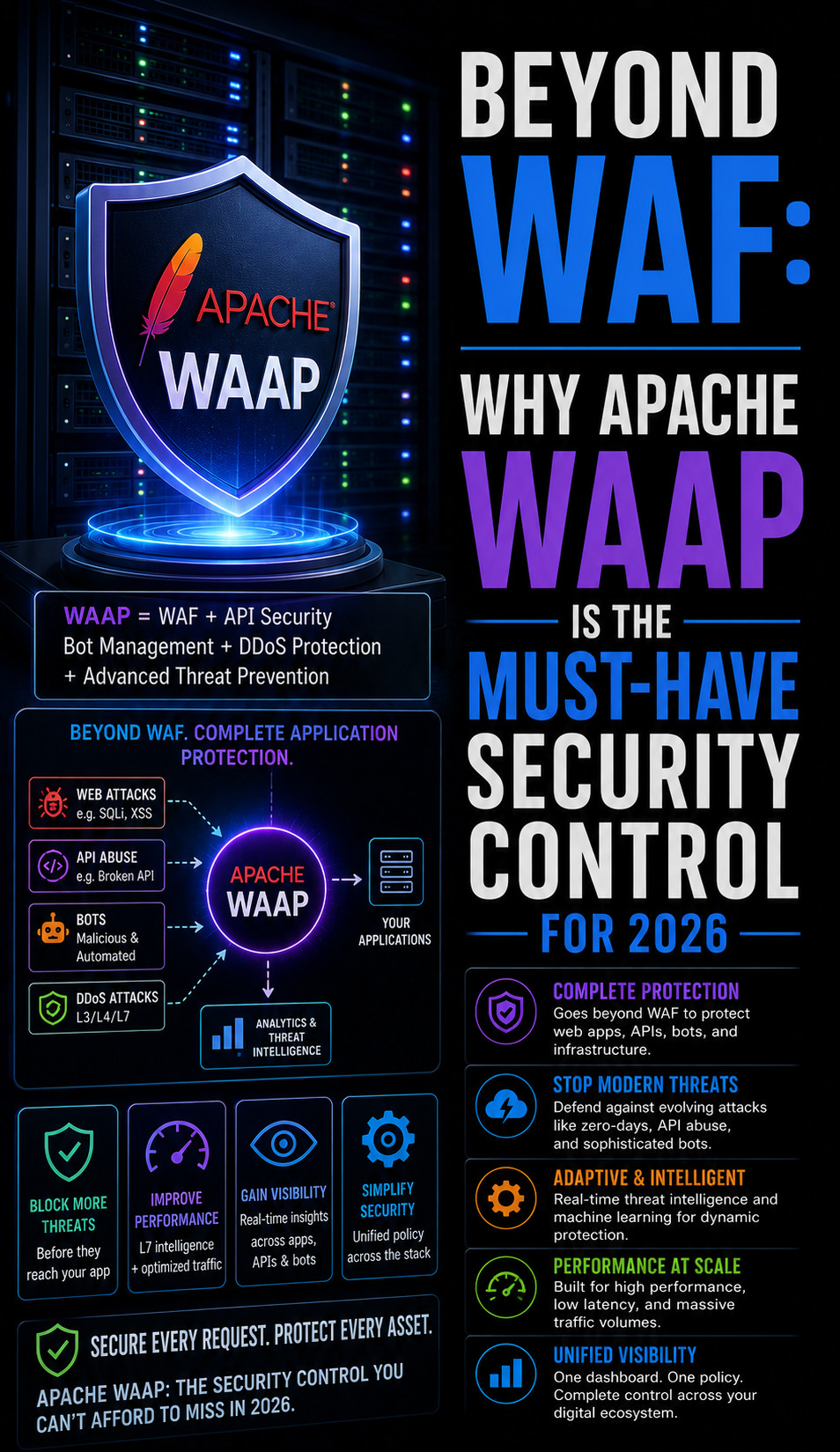
The setting basically says your Firewall is allowing all traffic in, out and forward if required. For a Firewall with rules set should look something like this:
Picture Credit
In this image it is clearly seen the firewall is accepting some connections and dropping ones that go against a rule.
4. Deny All Chains
A shortcut to deny one or any of the chains is:
iptables --policy INPUT DROP
iptables --policy OUTPUT DROP
iptables --policy FORWARD DROP
Now that you know what your default settings are, you can go about configuring rules to make your firewall behave the way you want it to.
5. Basic Rule Formatting
You can set rules with 3 settings:
- Accept: Accepts incoming, outgoing connections or forwards a connection.
- Drop: Drops incoming, outgoing or forward requests with no error responses.
- Reject: Drops incoming, outgoing or forward requests but sends back error responses.
You can use these to Accept, Drop or Reject specific IP’s, IP ranges or ports that hit the Input, Output or Forward chain.
- To add a ‘drop‘ rule to the ‘Input‘ chain for a particular IP, you can use the command:
# iptables -A INPUT 2 -s 200.58.10.5 -j DROP
- Now, to ‘drop‘ an ‘IP‘ range from ‘Input’ chain, type:
# iptables -A INPUT -s 10.10.10.0/24 -j DROP
You can also specify a specific type of connection and a port, to block connections of that nature only. - To add a ‘drop‘ ‘ssh connections‘ rule for IP ‘10.10.10.10’ on an ‘Input‘ chain, use command:
iptables -A INPUT -p tcp --dport ssh -s 10.10.10.10 -j DROP
- All changes made to Iptables must be saved, or they will be flushed the next time the server is rebooted. To save new rules, type:
# service iptables save
- To ‘block‘ ‘outgoing‘ connections (from you organization to the world), for example connections to ‘www.facebook.com’, first find the IP of the destination address using the command:
# host -t a www.facebook.com
Note down the IP that is displayed on your screen, then use the command:
# iptables -A OUTPUT -p tcp -d XX.XX.XX.XX -j DROP
Where XX.XX.XX.XX stands for Facebook.com’s IP noted after first command. - You can also use the domain name directly, like:
# iptables -A OUTPUT -p tcp -d www.facebook.com -j DROP
- To ‘allow‘ particular IPs through your Firewall, use the ‘Input‘ chain and the ‘Accept‘ Parameter.
iptables -A INPUT -p tcp --destination-port 80 -m iprange --src-range 192.168.1.100-192.168.1.200 -j ACCEPT
This allows ‘TCP’ connections from IP range mentioned through port ‘80′
With these basic rules understood, you should be able to set up rules to build a stable firewall system. If you need further assistance, please do not hesitate to contact us.
To get more updates you can follow us on Facebook, Twitter, LinkedIn
Subscribe to get free blog content to your Inbox
-
Previous Post
403 Forbidden Error – Causes and Fixes