What is Linux Server Firewall Configuration and How It Secures Your Server
Linux server firewall configuration is the process of securing a server by controlling incoming and outgoing traffic using rule-based filtering at the operating system level. In real-world production environments, infrastructure engineers configure firewalls using tools like UFW and nftables to allow only trusted services such as HTTP, HTTPS, and SSH while blocking all unauthorized access attempts. This approach ensures that malicious traffic never reaches the application layer, effectively protecting servers from brute-force attacks, port scanning, and unauthorized intrusion. A properly configured firewall acts as the first line of defense and is a foundational requirement in any secure server deployment.
Why Firewall Configuration is Critical for Server Security in 2026
In 2026, automated bots and AI-driven systems scan the internet for open ports within seconds of deployment. Even fully patched servers become vulnerable if unnecessary ports remain open. Engineers follow a Zero Trust model by blocking all incoming traffic by default and allowing only required connections. By enforcing this “implicit deny” approach, engineers drastically reduce the attack surface and prevent unauthorized communication at the network layer before it can impact applications or data.
PROTECT YOUR SERVER WITH ENTERPRISE-GRADE FIREWALL SECURITY
Are weak firewall rules leaving your Linux servers exposed to cyber threats?
Open ports, outdated firewall rules, and poor monitoring can expose production servers to brute-force attacks and unauthorized access. Our engineers help secure Linux environments using UFW, nftables, proactive monitoring, and advanced server hardening strategies.
How Engineers Configure Linux Firewall Using UFW in Production Environments
When engineers configure firewalls using UFW, they follow a structured and cautious process to ensure security without disrupting services. The configuration begins by setting default policies that deny all incoming traffic while allowing outgoing connections required for system functionality. Engineers first allow HTTP and HTTPS to ensure web access. They then restrict SSH to trusted IPs to prevent unauthorized logins. After validating the rules, they enable the firewall and confirm that only intended traffic is allowed. This methodical approach ensures that the server remains secure while maintaining uninterrupted service availability.
Why Outdated Firewall Rules Fail in Modern Cloud Infrastructure
One of the most common reasons for firewall-related security breaches is configuration drift, where outdated or unnecessary rules remain active long after the services they were meant to protect are no longer in use. Traditional firewall tools such as iptables often struggle to manage complex and dynamic rule sets in modern cloud environments. These legacy configurations can leave unintended ports open, creating entry points for attackers. To address this, engineers have shifted toward nftables, which provides a more efficient and scalable framework for managing firewall rules with better performance and reduced system overhead.
How Infrastructure Engineers Diagnose Firewall Issues and Network Threats
When servers experience connectivity issues or unusual behavior, engineers rely on a structured diagnostic approach to identify the root cause. They begin by analyzing active network ports and services to ensure that only expected processes are listening for connections. Firewall logs are then reviewed to detect blocked or suspicious traffic patterns, helping identify whether legitimate requests are being denied or if malicious activity is targeting the server. In more complex scenarios, engineers capture live network traffic to observe how packets are being handled in real time. This data-driven troubleshooting method enables precise identification of misconfigurations and potential threats.
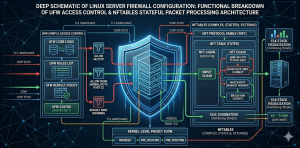
Advanced Firewall Security Using Nftables for High-Performance Servers
For high-traffic production environments, nftables has become the preferred firewall framework due to its efficiency and scalability. Nftables simplifies rule management across multiple protocols, reducing complexity and improving performance. Engineers use it for rate limiting, IP blocking, and kernel-level packet filtering. This stops malicious traffic early and ensures high availability with low latency.
Real-World Scenario: How Engineers Prevent DDoS Attacks Using Firewall Rules
In real-world production environments, servers often face distributed denial-of-service (DDoS) attacks designed to overwhelm network resources. Engineers mitigate these threats by implementing intelligent firewall rules that limit the number of requests from a single source and drop suspicious packets before they reach the application layer. By applying rate limiting and early packet filtering, engineers can prevent resource exhaustion and maintain service availability even under high traffic conditions. This proactive approach ensures that legitimate users continue to access services without disruption.
Common Firewall Misconfigurations That Cause Downtime and Security Risks
Despite the importance of firewall configuration, improper setups can lead to significant downtime and security vulnerabilities. One of the most common mistakes is accidentally blocking SSH access, which results in administrators losing remote connectivity to the server. Other issues include leaving unnecessary ports open, creating inefficient rule sets that impact performance, and failing to monitor firewall activity. Engineers avoid these problems by carefully validating configurations, testing changes before deployment, and maintaining proper logging and monitoring practices.
Monitoring Firewall Activity Using Prometheus, Grafana, and Zabbix
Effective firewall management requires continuous monitoring to detect and respond to threats in real time. Engineers use Prometheus for metrics, Grafana for visualization, and Zabbix for alerts. Centralized monitoring provides visibility into dropped packets, suspicious IPs, and attack patterns. This enables proactive threat detection and rapid response to emerging security risks.
Cloud Security Groups vs Linux Firewall: Why Engineers Use Both Layers
Modern cloud infrastructure relies on a layered security approach that combines cloud-level security groups with server-level firewall configurations. Cloud security groups act as the first line of defense by controlling traffic at the network level, while Linux firewalls provide granular control within the server itself. This dual-layer strategy prevents unauthorized access and enhances security, even if one layer is misconfigured. Engineers synchronize these layers to maintain consistent and effective protection across the infrastructure.
Best Practices for Linux Server Firewall Configuration Used by Experts
Experienced infrastructure engineers follow best practices like least privilege, restricted access to critical services, and automated firewall rule deployment. They also perform regular audits to identify unused rules and ensure that configurations remain aligned with current infrastructure requirements. By continuously refining firewall policies and monitoring system behavior, engineers maintain a secure and efficient server environment.
Linux Server Firewall Configuration FAQ:
What is Linux server firewall configuration and why is it important?
Linux server firewall configuration secures your server by controlling incoming and outgoing traffic using rule-based filtering. It blocks unauthorized access and ensures that only trusted services like HTTP, HTTPS, and SSH are allowed, protecting your infrastructure from attacks.
Which firewall is better in Linux: UFW or nftables?
UFW is best for beginners and simple rule management, while nftables is ideal for advanced, high-performance environments. Engineers prefer nftables for scalability, efficiency, and handling complex firewall rules in modern cloud infrastructure.
Why do firewall misconfigurations cause downtime or security risks?
Firewall misconfigurations can block critical services like SSH or leave unnecessary ports open. This can either lock administrators out of the server or expose it to attacks, leading to downtime and security breaches.
How do engineers detect firewall issues in Linux servers?
Engineers analyze open ports, review firewall logs, and monitor network traffic to identify issues. They also use real-time packet inspection and monitoring tools to detect blocked legitimate requests or suspicious activity.
What is the best way to secure a Linux server firewall in 2026?
The best approach is to follow a Zero Trust model by blocking all incoming traffic by default and allowing only required services. Combine this with continuous monitoring, regular rule audits, and layered security using cloud security groups and server-level firewalls.
Final Thoughts: Building a Secure and Scalable Firewall Strategy in 2026
Linux server firewall configuration is not a one-time setup but an ongoing process that evolves with the infrastructure. Engineers treat firewalls as dynamic systems that require continuous optimization, monitoring, and updates to remain effective against modern threats. By combining structured configuration, nftables, and real-time monitoring, organizations can build a secure and high-performance infrastructure. In 2026, mastering firewall configuration is essential for ensuring both security and scalability in any cloud or server environment.