What Are the First Steps When a Website Goes Down?
Cpanel,cPanel & WHM,Server Management,Overview: How to Quickly Diagnose and Fix a Website Downtime Issue A website goes down when failures occur across the DNS layer, server infrastructure, or application stack. The fastest way to recover is to first confirm whether the outage is global or limited to your network using external monitoring tools. Once confirmed, check DNS resolution…
Read moreSolving High Churn: How 24/7 Outsourced Hosting Support Stops Client Attrition
Cpanel,cPanel & WHM,Server Management,Overview: How 24/7 Outsourced Hosting Support Stops Client Attrition Outsourced hosting support is a direct strategy to stop client churn by ensuring 24/7 technical expertise is available to fix server issues the moment they arise. When hosting providers struggle with slow response times or technical bottlenecks, client trust breaks down and attrition follows. By integrating…
Read moreAI Finds 271 Hidden Flaws in Your Browser
cyber security,IT Management,Overview For years, browsers have been treated as a safe and neutral layer between users and the internet. However, that assumption no longer holds true in today’s complex digital environment. Modern browsers are deeply integrated with business systems, cloud platforms, and sensitive data workflows. Recent AI-driven discoveries have revealed that many vulnerabilities were always present…
Read moreYour VPN Is the Unlocked Back Door Hackers Are Walking Through Right Now
Cloud Infrastructure,cyber security,IT Infrastructure,Overview For a long time, VPNs were treated like the gold standard of remote access. If someone connected through the VPN, they were considered “inside” the network and therefore safe to trust. That model worked when offices were fixed, users were limited, and applications lived in one place. That world is gone. Today, employees work…
Read moreCybersecurity Mistake: Are You Allowing Too Many Login Attempts on Your cPanel Server?
Cpanel,cPanel & WHM,cyber security,Key Intelligence: To protect your server, you must limit cPanel login attempts by combining application-layer security with network-level firewall rules. Unrestricted retries allow botnets to exhaust CPU resources through constant PAM authentication requests. You should enable cPHulk Brute Force Protection and integrate ConfigServer Security & Firewall (CSF) to drop malicious traffic before it reaches the…
Read moreCybersecurity Threat: Is Public WiFi Safe? How to Secure Public WiFi & Stop WiFi Hacking Risks
cyber security,Firewall/Iptables/Security,Overview: Public WiFi is inherently hostile because it lacks mandatory encryption and identity validation at the protocol level. We found that attackers exploit these vulnerabilities using VPN tunnels and Zero-Trust models to intercept data through Man-in-the-Middle (MITM) attacks, ARP spoofing, and “Evil Twin” rogue hotspots. Without protection, your session tokens and credentials transmit in plaintext…
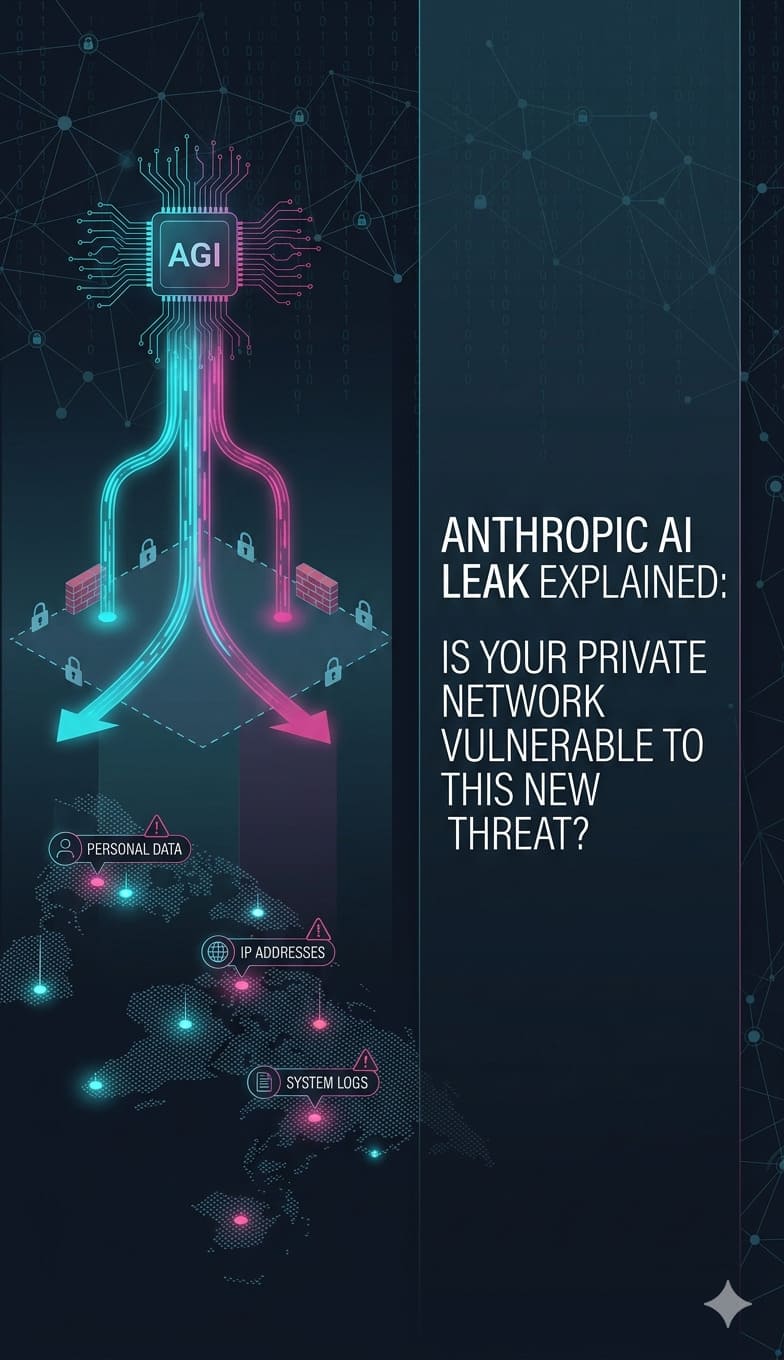
Read moreAnthropic AI Leak Explained: Is Your Private Network Vulnerable to This New Threat?
AI in IT Support & Infrastructure,IT Infrastructure,IT Management,Summary: The accidental exposure of Anthropic’s Claude Code source code in April 2026 has introduced severe risks, including CVE-2026-35022, which allows remote code execution via shell metacharacter injection. This leak gives hackers a roadmap to bypass security filters and hijack agentic AI systems to exfiltrate API keys, SSH credentials, and environment variables. To fix these…
Read moreAI Pentesting for Business: How to Catch Security Gaps Before Hackers Use AI?
AI on AWS,Cloud Infrastructure,Key Takeaways: AI pentesting for business uses autonomous, agentic models to simulate real-world cyberattacks and identify exploit paths that legacy scanners miss. While traditional tools flag isolated vulnerabilities, we found that AI agents chain multiple security gaps to reveal how attackers move laterally through your network. In 2026, this shift from static annual audits to…
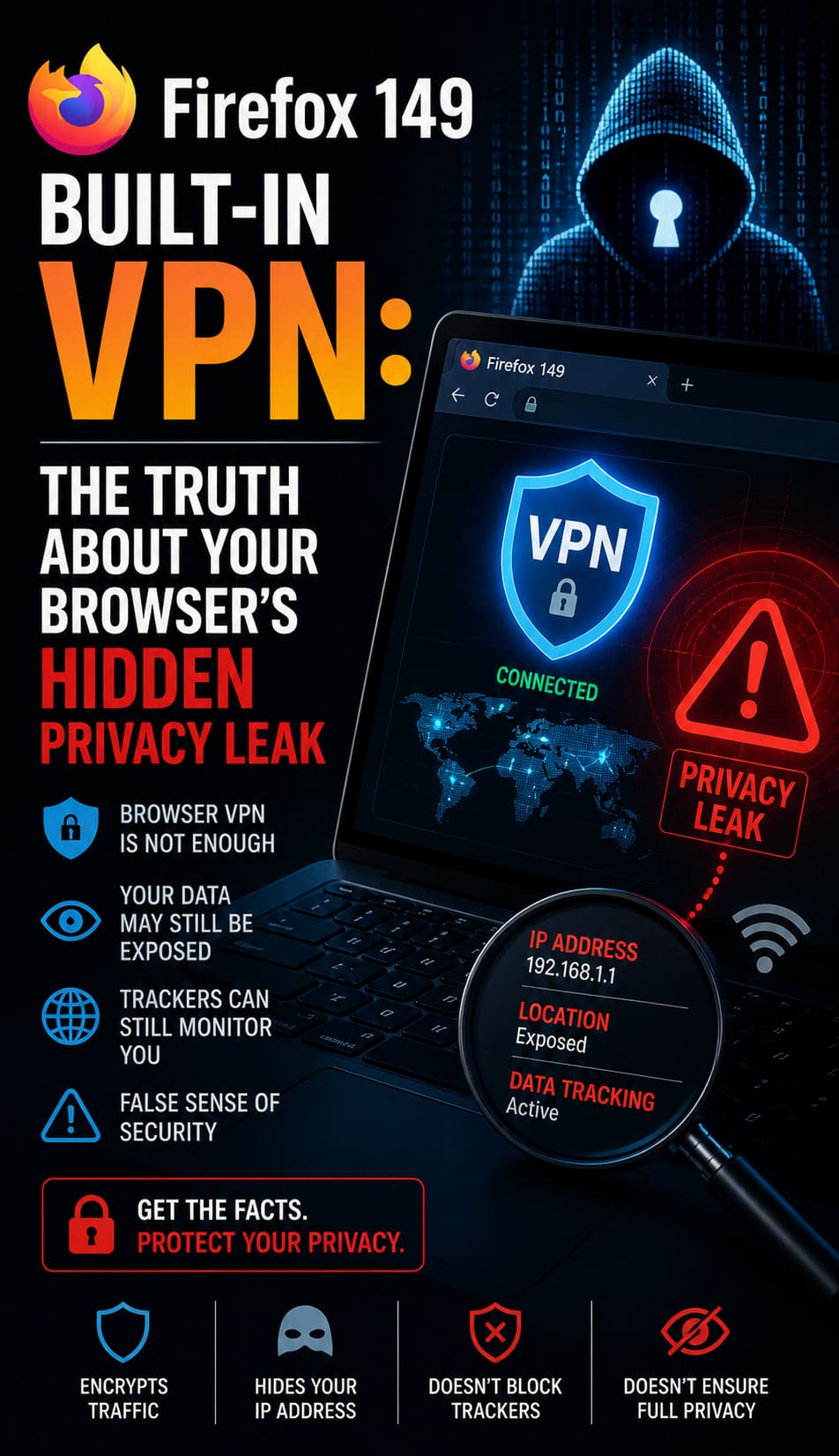
Read moreFirefox 149 Built-In VPN: The Truth About Your Browser’s Hidden Privacy Leak
Firewall/Iptables/Security,IT Infrastructure,Linux General,What You Need to Know: Firefox 149 Built-In VPN Direct Impact Analysis Firefox 149 features a native, built-in browser VPN designed to stop the “Hidden Privacy Leak” where websites and ISPs harvest your real IP address. Unlike standard private browsing modes that only clear local history, this integrated proxy creates a secure, zero-log tunnel for…
Read moreGoogle Drive Ransomware Protection: Why Your Cloud Files are Still at Risk?
backup and recovery,Cloud Infrastructure,Quick Breakdown: Google Drive Ransomware Protection Analysis Google Drive is vulnerable to automated ransomware because desktop sync clients treat encrypted files as legitimate updates, instantly mirroring corrupted data to the cloud. We found that the core risk lies in bidirectional synchronization; when a local machine is hit, the sync tool replaces clean cloud files with…
Read more