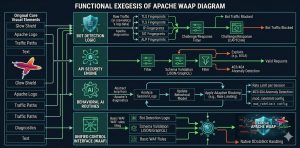
Apache WAAP (Web Application and API Protection) is the essential evolution of traditional firewalls designed to secure modern web environments. It integrates signature-based filtering with behavioral AI and API-specific security to block sophisticated 2026 threats. Unlike a standard WAF, WAAP handles bot mitigation and DDoS protection natively. This unified control ensures that infrastructure remains resilient against automated exploits that bypass legacy rules.
The Fundamental Shift from Static WAF to Adaptive WAAP
Legacy Web Application Firewalls primarily rely on static signatures to identify known attack patterns like SQL injection. In 2026, attackers use polymorphic malware and AI-driven bots that change their signatures in real-time. This shift makes signature-based defense insufficient for production-grade environments. Engineers now require Apache WAAP because it analyzes intent rather than just matching characters. It monitors user behavior over time to distinguish between a legitimate customer and a malicious script. By adopting WAAP, organizations move from reactive blocking to proactive threat neutralization.
Understanding the Root Cause of WAF Failure in Modern Stacks
The primary issue with older security models is their inability to inspect deep API traffic. Modern applications rely heavily on REST and GraphQL endpoints which traditional WAFs often overlook or misinterpret. Malicious actors exploit this visibility gap by tunneling attacks through legitimate-looking API calls. Furthermore, the rapid adoption of multi-cloud infrastructure has fragmented the security perimeter. Without a centralized WAAP, engineers face “alert fatigue” from inconsistent logs across different cloud providers. This lack of visibility is the root cause of many successful data breaches today.
How Engineers Diagnose Security Gaps in Apache Servers
Diagnosis begins with a comprehensive audit of current server headers and traffic patterns. Infrastructure leads use tools like mod_security logs combined with ELK Stack visualization to find anomalies. When an attack occurs, engineers look for specific patterns in /var/log/apache2/error.log or /var/log/httpd/error_log. They check for high frequencies of 403 Forbidden or 404 Not Found errors originating from single IP blocks. High CPU usage on the httpd process often indicates a botnet attempting to brute-force a login. Identifying these patterns early allows for the creation of more resilient security policies.
Step-by-Step Implementation of WAAP Logic in Apache
To transition toward a WAAP-style architecture, engineers first harden the core Apache configuration. They begin by disabling unnecessary modules that increase the attack surface. Use the command httpd -M to audit active modules and prune the list. Next, integrate an advanced module like mod_security2 with the latest OWASP Core Rule Set. This provides the baseline filtering needed for common web vulnerabilities. Engineers then layer behavioral analysis tools to monitor traffic flow. This step involves configuring rate limiting via mod_ratelimit to mitigate automated scraping attempts.
Configuring Advanced Behavioral Detection Rules
True WAAP functionality requires moving beyond simple IP blocking to session-based analysis. Engineers configure the server to track user behavior across multiple requests. This is done by setting up unique session identifiers and monitoring request rates per session. If a session exceeds a predefined threshold, the server automatically triggers a challenge, such as a CAPTCHA. This method stops bots without impacting the experience for real human users. It creates a dynamic defense layer that adapts to the intensity of incoming traffic.
Real-World Production Scenarios for API Protection
In a live production environment, protecting API endpoints is the highest priority for server administrators. An engineer might manage a Java Spring Boot application that handles sensitive financial data. They would implement strict JSON schema validation within the Apache layer to ensure data integrity. Any request that does not match the expected schema is rejected before it reaches the application. This prevents “Broken Object Level Authorization” attacks, a common threat in 2026. This strategy saves backend resources and provides an immediate response to malicious probes.
Essential Tools for Monitoring WAAP Performance
Effective security management requires real-time visibility into server health and threat levels. Engineers utilize Prometheus and Grafana to visualize security metrics gathered from Apache logs. They also integrate Nagios for active monitoring of server uptime and response times. If the WAAP layer introduces too much latency, it must be optimized. Cloud-native environments might use AWS CloudWatch or Azure Monitor to track these security events across a global fleet. These tools provide the data needed to justify further infrastructure investments.
Impact of WAAP on Server Performance and Security
Implementing a WAAP layer significantly improves security posture while requiring careful performance tuning. While deep packet inspection consumes CPU cycles, it prevents the massive resource drain caused by DDoS attacks. Engineers use ab (Apache Benchmark) or h2load to test the server under security-heavy configurations. They aim for a balance where protection does not increase latency beyond 100 milliseconds. Effective caching strategies via mod_cache can often offset the overhead of security processing. This ensures a fast and safe experience for the end user.
Best Practices Used by Senior Infrastructure Engineers
Experienced architects always follow the principle of “Defense in Depth” when securing Linux server management services. They never rely on a single tool to protect the entire stack. Instead, they layer firewall rules at the OS level using iptables or nftables beneath the Apache WAAP. They also ensure that patch management is automated to close vulnerabilities as soon as they are discovered. Regular server hardening audits are performed using tools like Lynis to find configuration weaknesses. These habits ensure a consistently high level of security across all managed assets.
Comparing Traditional WAF with Modern WAAP Solutions
A direct comparison shows that WAF is a subset of the broader WAAP umbrella. WAF focuses on the application layer, while WAAP adds API security, bot management, and DDoS protection. In 2026, a WAF is seen as a basic requirement, but WAAP is the competitive standard. Organizations using WAAP report a 60% reduction in successful bot attacks compared to those using only WAF. Furthermore, WAAP solutions offer better integration with DevOps pipelines through API-driven configuration. This allows for security to be treated as code during the deployment process.
Case Study: Mitigating a Large-Scale Botnet Attack
A global e-commerce client recently faced a massive credential stuffing attack targeting their login API. Their traditional WAF failed because the attack used thousands of rotating residential IP addresses. The engineering team quickly deployed an Apache WAAP configuration with behavioral fingerprinting. By analyzing the “TLS Fingerprint” of incoming requests, the team identified the botnet’s signature. They blocked 99% of the malicious traffic within thirty minutes without affecting legitimate users. This real-world success highlights the necessity of adaptive security controls.
STOP MODERN WEB & API ATTACKS BEFORE THEY REACH YOUR SERVER
Is your traditional WAF failing to block modern bot attacks and API exploits?
AI-driven attacks, API abuse, and automated bot traffic can bypass outdated security layers. Our engineers help implement advanced WAAP protection, server hardening, bot mitigation, and proactive monitoring to secure high-traffic production environments.
Troubleshooting Common WAAP Configuration Errors
When a WAAP is too aggressive, it can lead to false positives where real users are blocked. Engineers diagnose this by searching the audit logs for specific rule IDs that triggered the block. Use the command grep "ModSecurity: Access denied" /var/log/apache2/error.log to find these entries. Once the problematic rule is identified, it can be tuned or put into “Detection Only” mode. This allows the engineer to observe its impact before fully enforcing the block. Proper tuning is an ongoing process that requires constant attention to traffic trends.
Using Cloud Infrastructure for Enhanced WAAP Scaling
Cloud-based WAAP solutions offer the benefit of massive scale and global threat intelligence. Services like Google Cloud Armor or AWS WAF can be integrated with on-premise Apache servers. This “Hybrid WAAP” model allows for heavy traffic to be scrubbed at the edge of the network. It keeps malicious traffic far away from the origin server, preserving local bandwidth. Engineers use these cloud tools to manage global blocklists that update in real-time based on worldwide threats. This collaborative approach is vital for defending against modern organized cybercrime.
Summary of Key Takeaways for Server Administrators
Transitioning to Apache WAAP is no longer optional for high-traffic environments in 2026. The shift requires a combination of robust tools, behavioral logic, and constant monitoring. Engineers must focus on API protection and bot mitigation to stay ahead of automated threats. Utilizing proactive server hardening and white label support can help maintain a secure infrastructure. By following these expert practices, you ensure that your servers remain both fast and impenetrable.
FAQ: Apache WAAP and Modern Web Application Security
How does Apache WAAP work?
Why does a traditional WAF fail against modern attacks?
How do engineers fix false positives in Apache WAAP?
How to prevent Apache security breaches in 2026?
Final Thoughts: Securing the Future with Apache WAAP
The transition from a standard WAF to a comprehensive Apache WAAP framework is a necessity for any infrastructure lead in 2026. As cyber threats evolve into AI-driven, automated botnets, your defense strategy must become equally intelligent and adaptive. Relying on static signatures is no longer a viable security posture for production environments handling sensitive API data or high-volume web traffic.
By implementing the behavioral analysis, API protection, and rigorous server hardening techniques discussed in this guide, you move beyond simple compliance toward true operational resilience. This proactive approach not only protects your data but also preserves your server performance and SEO rankings by eliminating malicious overhead.
For engineers managing complex environments whether on cPanel, AWS, or private Linux clusters the goal remains the same: total visibility and rapid response. Start by auditing your current mod_security logs today and begin layering the behavioral controls that will keep your infrastructure secure through 2026 and beyond.